Mobile intelligent device security service implementation method and system supporting attribute based encryption
A mobile smart device, attribute-based encryption technology, applied in the fields of information security and communication, can solve the problem of difficult to run ABE data security for mobile smart devices, and achieve the effect of improving speed, ensuring security, and avoiding overhead.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
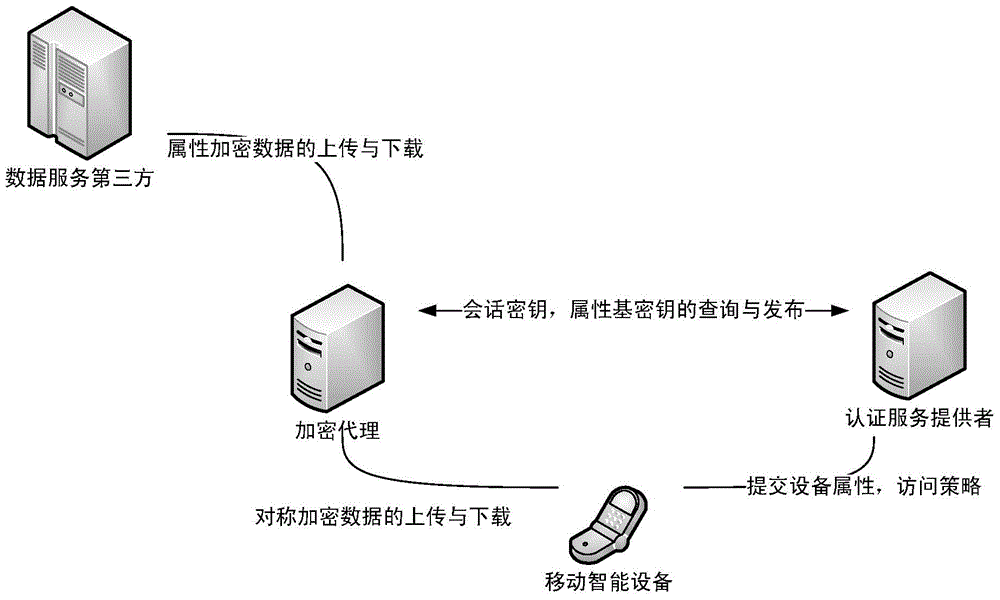
[0038] figure 1 It is a schematic diagram of a typical mobile smart device data security service network environment that supports attribute-based encryption, that is, a mobile smart device data security service implementation system that supports attribute-based encryption. The system mainly includes four parts:
[0039] Mobile smart devices (such as mobile phones, PADs, etc.): are the demand side of services.
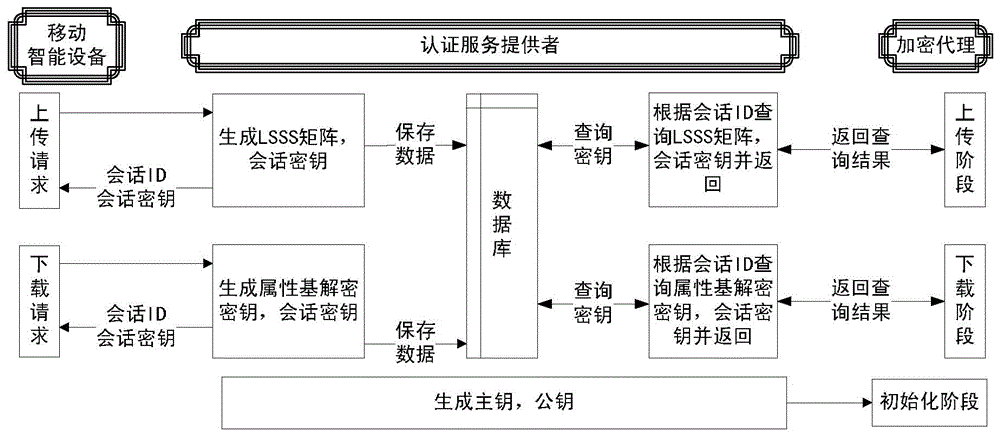
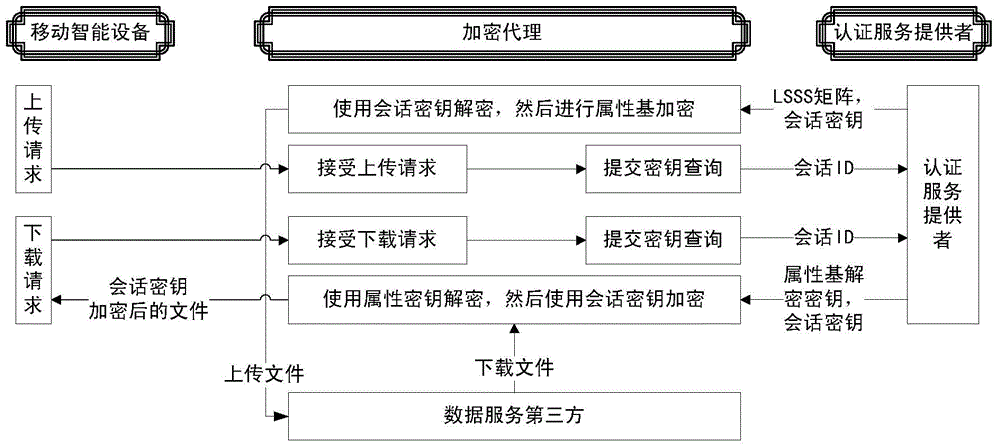
[0040] Authentication service provider: In the system initialization phase, it is mainly responsible for generating the master key and public key of the system; in the data upload phase, it is mainly responsible for uploading the session key and generating the LSSS matrix (Linear Security Shared Scheme Matrix); in the data download phase, it is mainly responsible for Responsible for downloading session keys and generating attribute-based decryption keys; in addition, providing key query services for encryption agents through the Restful interface, and managing informa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More