Industrial control network information security monitoring method based on funnel type white list
An industrial control network and information security technology, applied in the direction of electrical components, transmission systems, etc., can solve problems such as Ethernet monitoring and management that cannot be completely solved
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
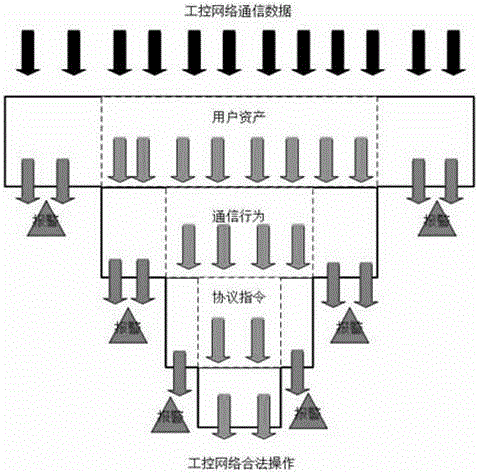
[0018] Such as figure 1 As shown, the funnel-type whitelist-based industrial control network information security monitoring method described in the embodiment of the present invention consists of the following steps:
[0019] ⑴In-depth analysis of industrial communication data: Master the ability to restore industrial communication protocols. Based on this ability, establish a data analysis list, including source IP, destination IP, source MAC, destination MAC, source port, destination port, general protocol type, industrial control Elements such as the protocol type store the obtained sample information in a list through the learning of a certain period of time, and construct the sequence model of instruction flow and information flow on the basis of network flow.
[0020] (2) Establish a trusted architecture for legal operations in the industrial control network: user assets in the industrial control network need to be trusted, which is reflected in the equipment connected ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More