Wireless access authentication method and device
A wireless access and authentication technology, applied in the field of communications, can solve problems such as poor user experience and complex wireless access authentication methods, and achieve the effect of ensuring access security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] Hereinafter, the present invention will be described in detail with reference to the drawings and examples. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
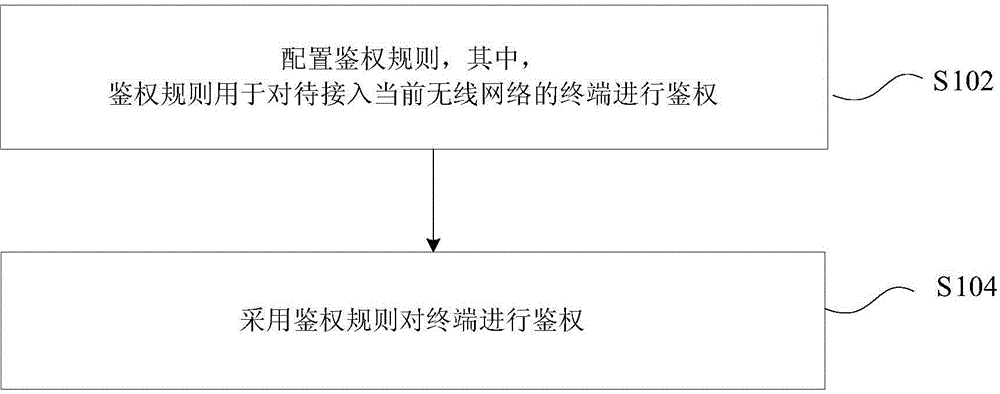
[0027] figure 1 It is a flowchart of a wireless access authentication method according to an embodiment of the present invention. like figure 1 As shown, the method may include the following processing steps:
[0028] Step S102: Configuring authentication rules, where the authentication rules are used to authenticate terminals to be connected to the current wireless network;
[0029] Step S104: Use authentication rules to authenticate the terminal.
[0030] The wireless access authentication method in the related art is relatively complicated, and the user experience is poor. use as figure 1 The method shown effectively curbs terminals attempting to access wireless devices with multiple differe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More