A two-way anonymous authentication system and method based on the principle of mimic defense
An anonymous authentication and anonymous authentication protocol technology, applied in the field of two-way anonymous authentication system, can solve the problems of DAA anonymous authentication unable to carry out active defense and poor network information security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
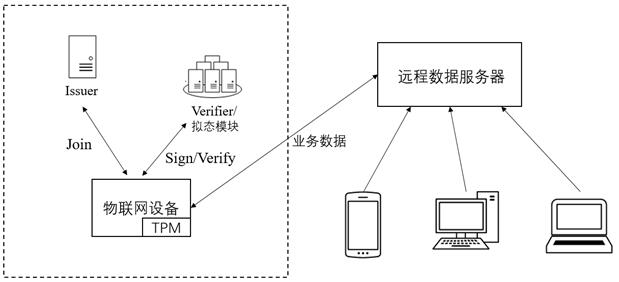
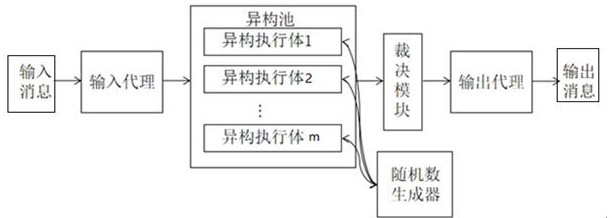
[0054] The invention discloses a two-way anonymous authentication system and method based on the principle of mimicry defense. The scheme will be further described and explained below in conjunction with the accompanying drawings.
[0055] The symbols and their definitions used in this scheme are shown in Table 1;
[0056]
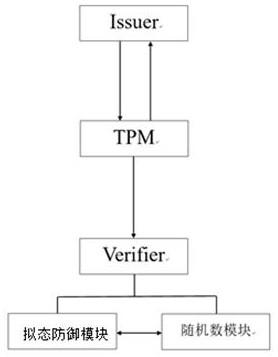
[0057] This solution includes the issuer of the certificate, the signer of the signer, and the verifier of the signature detector. The signer is also called the platform platform, and the platform platform can be divided into: the host host and the trusted computing platform module TPM.
[0058] The basic principles involved in this scheme are as follows:
[0059] 1), CL signature: CL signature is Camenisch-Lysyanskaya signature, which is used in the scenario of group signature or aggregate signature, which can improve the anonymity of signature and reduce the computational complexity of signature. CL signature is also a signature scheme suitable for z...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More