A protection method for access security of IP multimedia subsystem
A multimedia subsystem and security technology, applied in the direction of synchronous sending/receiving encryption equipment, data exchange through path configuration, etc., can solve the problems that the user terminal does not support the use of certificates, cannot authenticate UE identity, etc., and overcomes the problem of weak two-way authentication Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
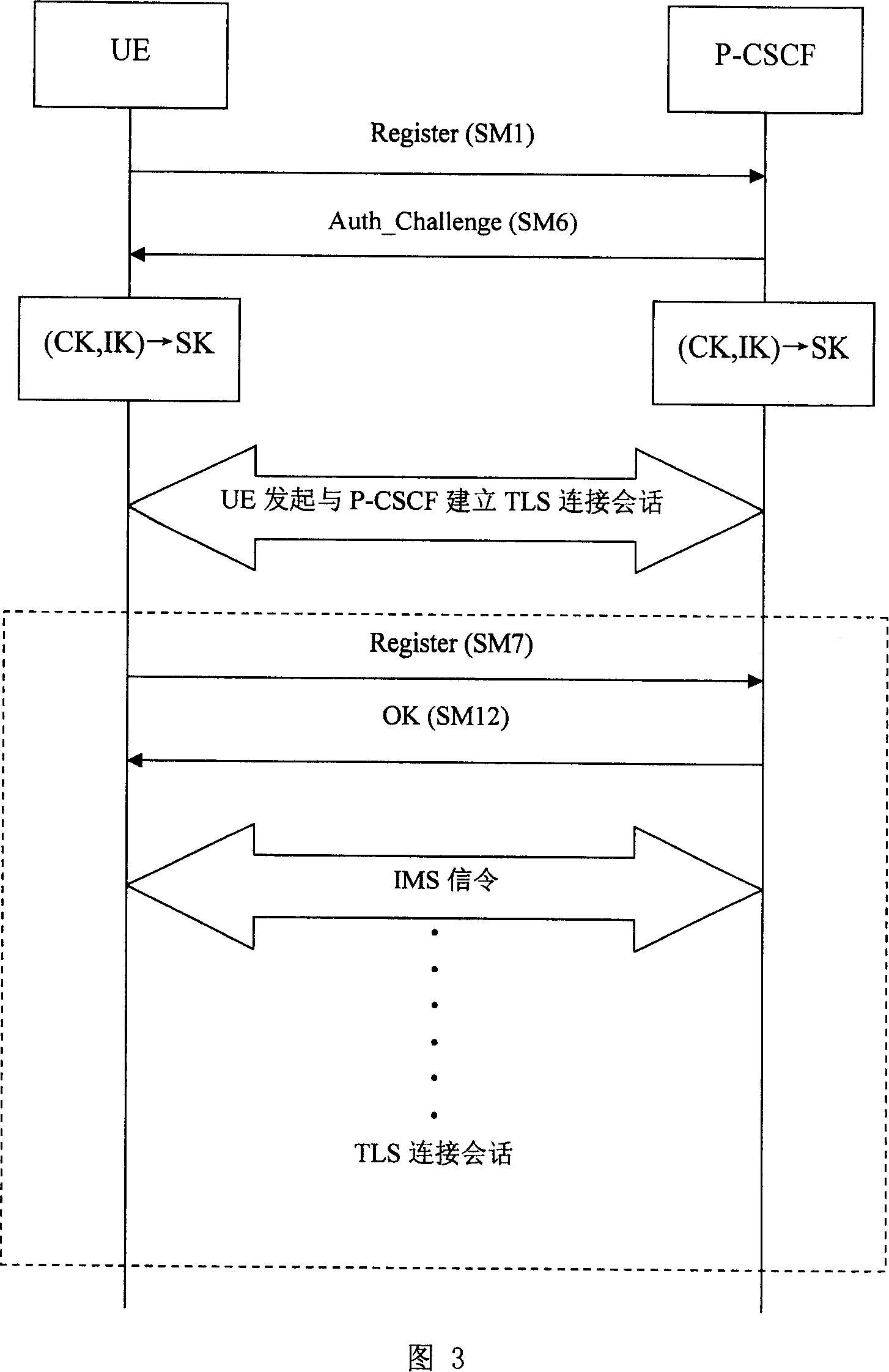
[0051] This embodiment describes the method for protecting IMS access security by using the TLS protocol in the present invention with reference to FIG. 3 . In this embodiment, both the UE and the P-CSCF support three security mechanisms: TLS, IPSec / IKEv2 and IPSec / IMS AKA, and the P-CSCF has a higher priority for TLS support. The UE's IMS access process flow is as follows:
[0052] 1. The UE sends an initial registration message (Register) SM1 to the P-CSCF, and the message includes require, proxy-require, and security-client message headers. The require and proxy-require message headers contain the label "sec-agree" option, indicating that the P-CSCF must support the security mechanism of the UE.
[0053] The Security-client message header contains a list of security mechanisms supported by the UE and their parameters, and its content is "TLS; IPSec / IKEv2; IPSec / IMS AKA, SPI_U, Port_U, list of cipher suites". Three security mechanisms: TLS, IPSec / IKEv2 and IPSec / IMSAKA, whe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More