A method for strengthening an application program of an android system
A technology of application programs and encryption methods, applied in the field of information security, can solve problems such as limited protection effect and inability to guarantee the security of application programs, and achieve the effects of resisting static analysis, integrity protection, and increasing security verification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
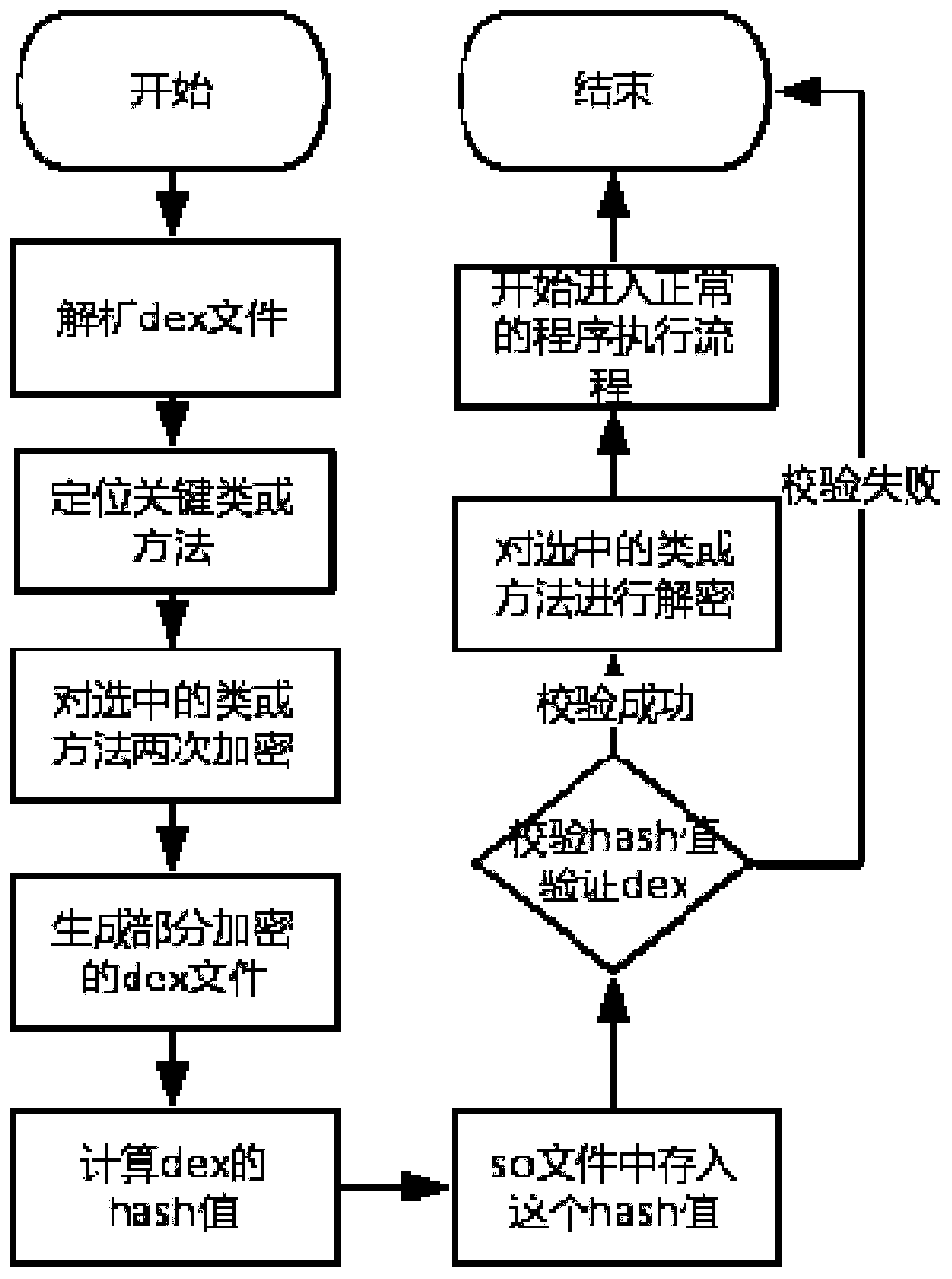
[0034] Below in conjunction with accompanying drawing, further describe the present invention through embodiment, but do not limit the scope of the present invention in any way.
[0035] The invention provides a reinforcement method based on the Android system binary stream encryption technology, figure 1 It is a flow chart of the method provided by the present invention, comprising the following steps:
[0036] A. To encrypt the key code, perform the following operations:
[0037] A1. Parse the classes.dex file;
[0038] A2. Target specific classes and methods;
[0039] A3. Use the key key1 for the first encryption;
[0040] A4. Use the key key2 for the second encryption;
[0041] A5. Update the dex file;
[0042] A6. Calculate the Hash value of the classes.dex file and encrypt the Hash value, and store it in the so file;
[0043] B. To decrypt the encrypted code, perform the following operations:
[0044] B1. Find the starting address of dex;
[0045] B2. Perform Has...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More