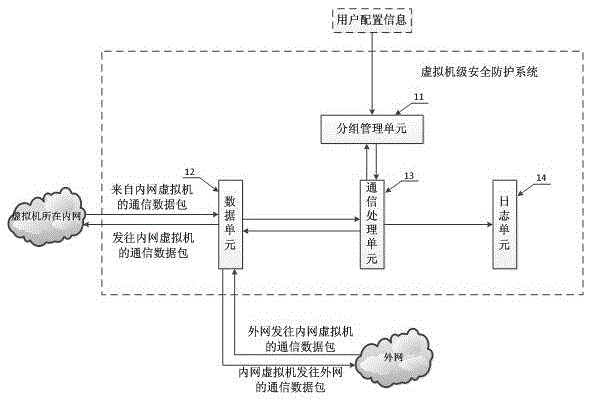
Virtual machine level security protection system and method
A security protection and virtual machine technology, applied in the field of network security, can solve problems such as inability to adapt to logical protection, inability to manage and monitor traffic, and achieve the effect of improving security protection and security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
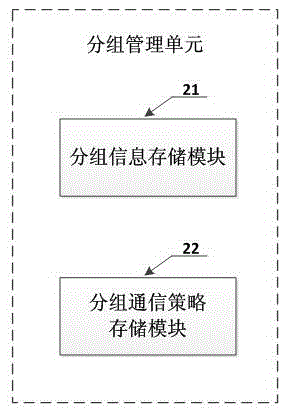
Examples
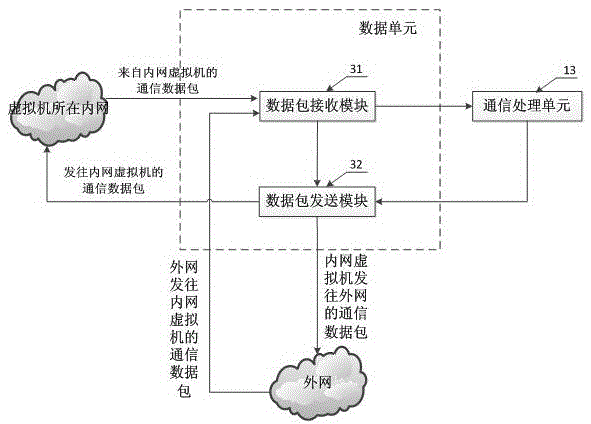
Embodiment approach
[0057] The difference between the virtual machine-level security protection system described in the second preferred embodiment of the present invention and the above-mentioned first preferred embodiment is that a security processing unit 15 is further added behind the communication processing unit 13, such as Figure 4 shown. The communication processing unit 13 receives the communication data packet between the virtual machines sent by the data unit 12, and first inquires the group management unit 11 to determine whether the source virtual machine and the destination virtual machine allow communication, and if the communication is not allowed, the data packet is directly discarded , while generating log information and sending it to the log unit 14 (this process is the same as the corresponding process of the first embodiment above), if the source virtual machine and the destination virtual machine allow communication, the communication processing unit 13 further sends the da...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More