Security control method used for cloud platform network
A technology of security control and cloud platform, applied in data exchange network, user identity/authority verification, digital transmission system, etc., can solve problems such as eavesdropping, and achieve high data transmission security effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
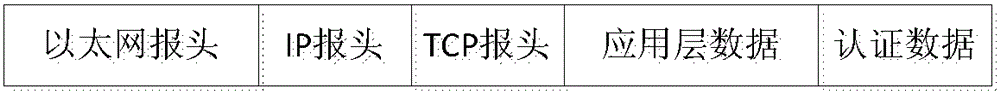
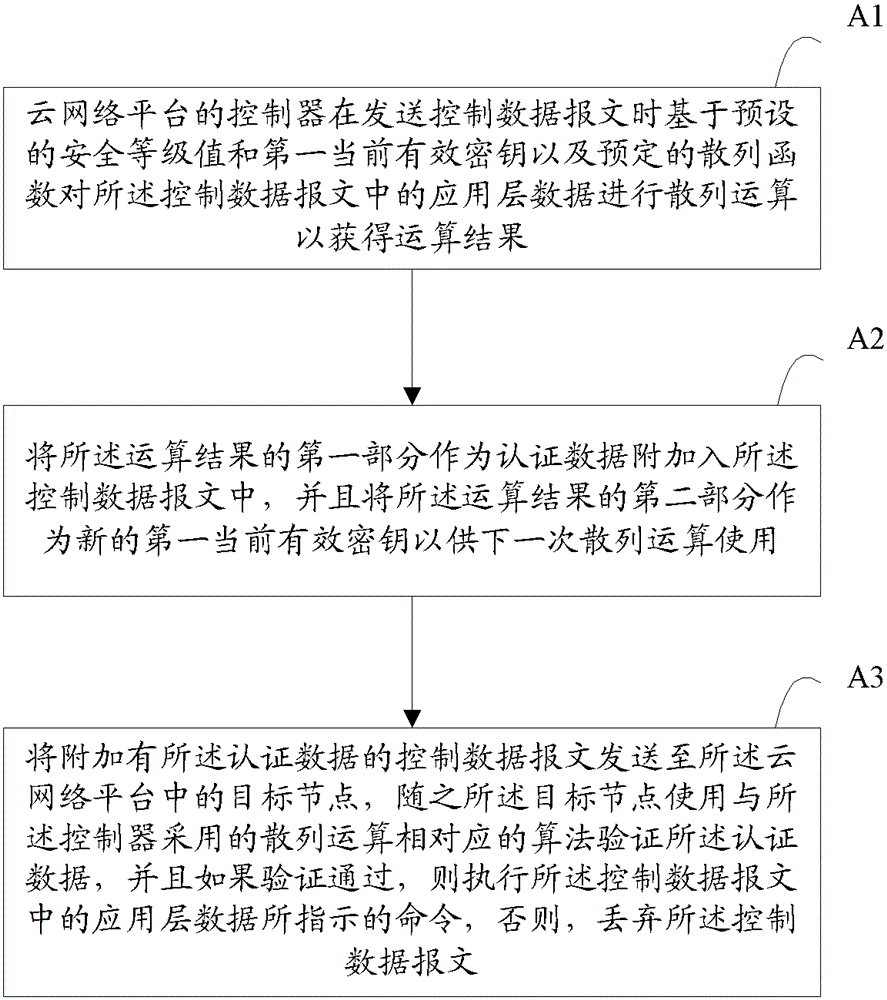
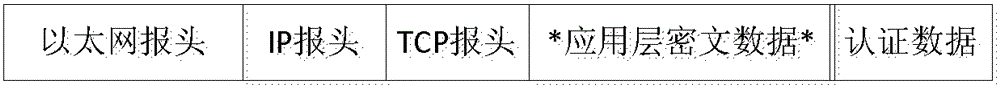
[0022] figure 1 It is a flowchart of a security control method for a cloud platform network according to an embodiment of the present invention. Such as figure 1 As shown, the security control method for the cloud platform network disclosed in the present invention includes the following steps: (A1) When the controller of the cloud network platform sends the control data message, based on the preset security level value and the first current effective encryption key and a predetermined hash function to perform a hash operation on the application layer data in the control data message to obtain an operation result; (A2) attach the first part of the operation result to the control data message as authentication data , and use the second part of the operation result as the new first current valid key for the next hash operation; (A3) Send the control data message with the authentication data attached to the cloud A target node in the network platform, and then the target node v...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More