A data security exchange system and method based on authority mapping
A technology of data security and exchange system, applied in the field of data security exchange system based on permission mapping, can solve the problems of single function, poor security, low degree of platform coupling, etc., achieve the effect of clear hierarchical structure and improved intelligence
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
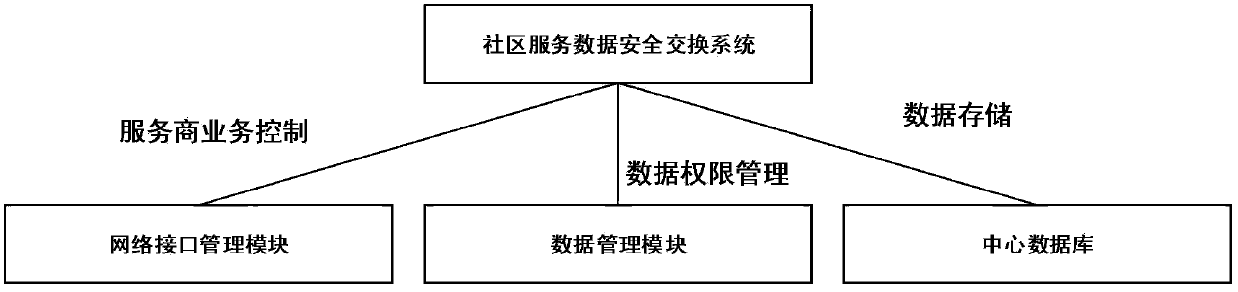
[0050] In the implementation of this example, a data security exchange system based on authority mapping is applied to a network composed of several service requesters and integrates third-party data. The security exchange system includes: a network interface management module, a data management module and central database;
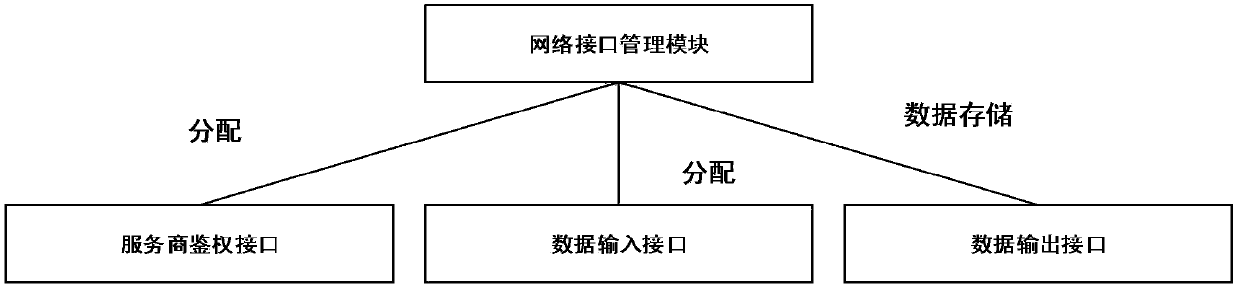
[0051] The network interface management module is used to implement the service requester's response, and allocate different network interfaces according to the service requester's request business, and then process the service requester's request business;
[0052] like figure 1 Shown: the network interface management module includes: service provider authentication interface, business data input interface and business data output interface;
[0053] The data management module is used to realize the interaction of data, and control the authority of the service requester and the central database to ensure the security of data exchange;
[0054] The cent...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More