Data integrity verification method and system
A data integrity and verification method technology, applied in digital data protection, electrical digital data processing, instruments, etc., can solve problems such as low efficiency and low security, and achieve the effect of improving efficiency and high security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
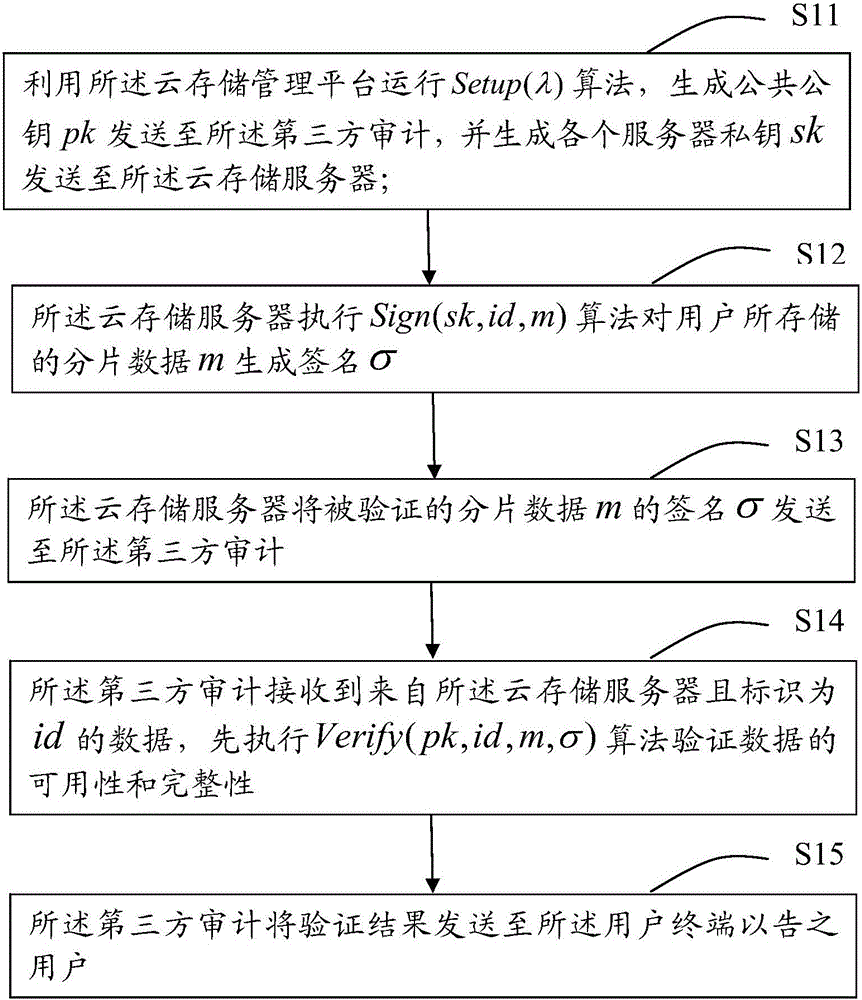
[0035] The specific embodiment of the present invention provides a method for verifying data integrity, which is applied to a cloud storage system. The cloud storage system includes a user terminal, a cloud storage server, a cloud storage management platform, and a third-party audit, wherein the data integrity The authenticity verification method mainly includes the following steps:
[0036] S11. Use the cloud storage management platform to run the Setup(λ) algorithm, generate a public key pk and send it to the third party for audit, and generate each server private key sk and send it to the cloud ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More