Method for realizing secure information backup
An implementation method and information security technology, which is applied in the field of information security backup implementation, can solve problems such as logic damage cannot be prevented, and achieve the effects of reliable data storage, simple operation and implementation, and high data security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
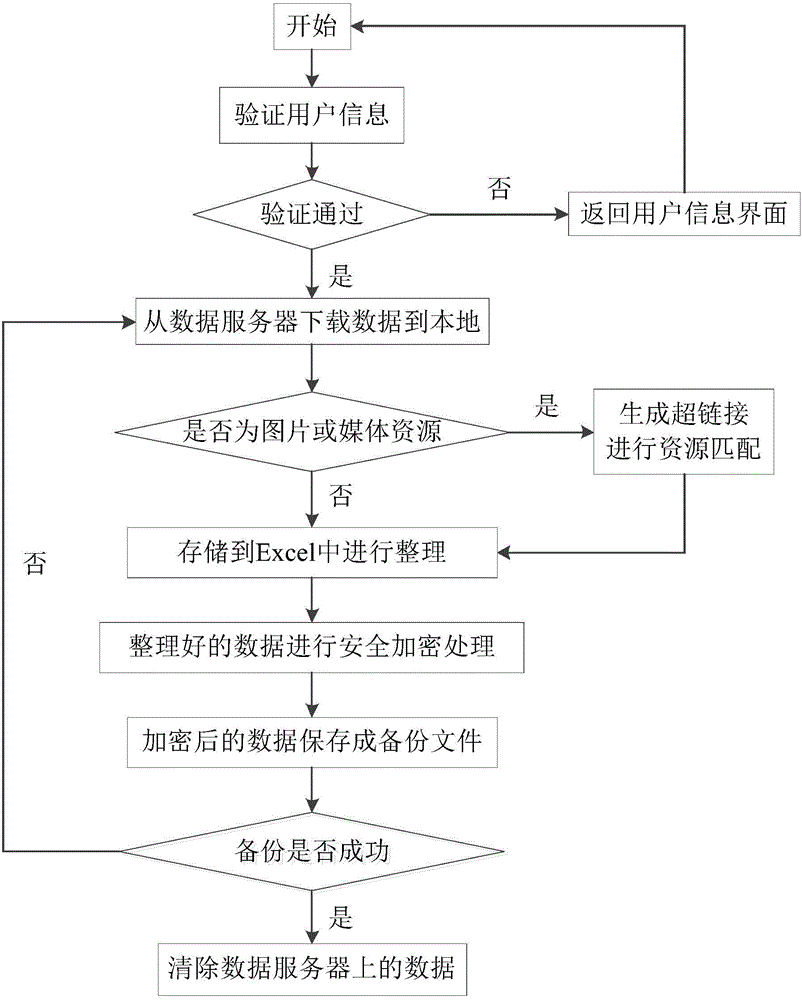
[0026] In order to illustrate the present invention more clearly, the present invention will be further described below in conjunction with preferred embodiments and accompanying drawings. Similar parts in the figures are denoted by the same reference numerals. Those skilled in the art should understand that the content specifically described below is illustrative rather than restrictive, and should not limit the protection scope of the present invention.
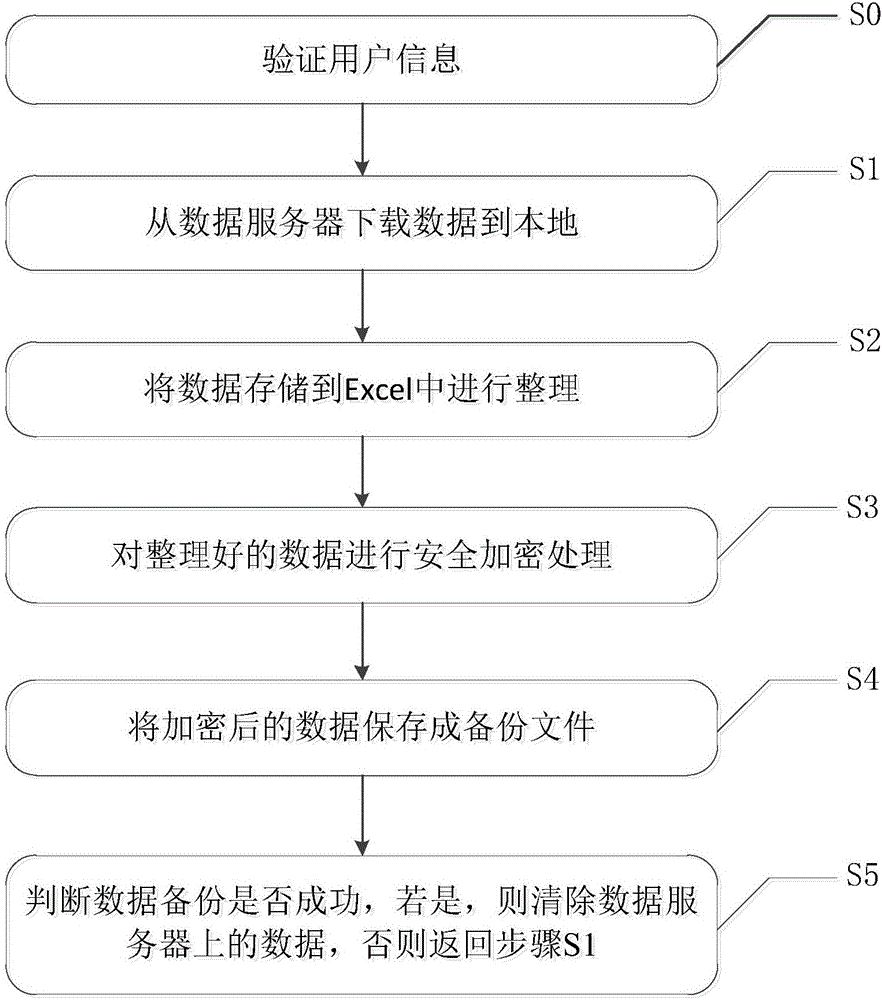
[0027] like figure 1 A method for implementing information security backup is shown, and the method includes the following steps:
[0028] S0: Verify user information, specifically including the following steps:
[0029] S001: Input user information on the user information interface;
[0030] S002: The control server matches the user information with the user information in the user information list pre-stored in the data server or the cloud, and if the matching is successful, the verification is passed, otherwise the ve...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More