Business encryption/decryption method and device
An encryption method and business technology, applied in the computer field, can solve problems such as low key security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
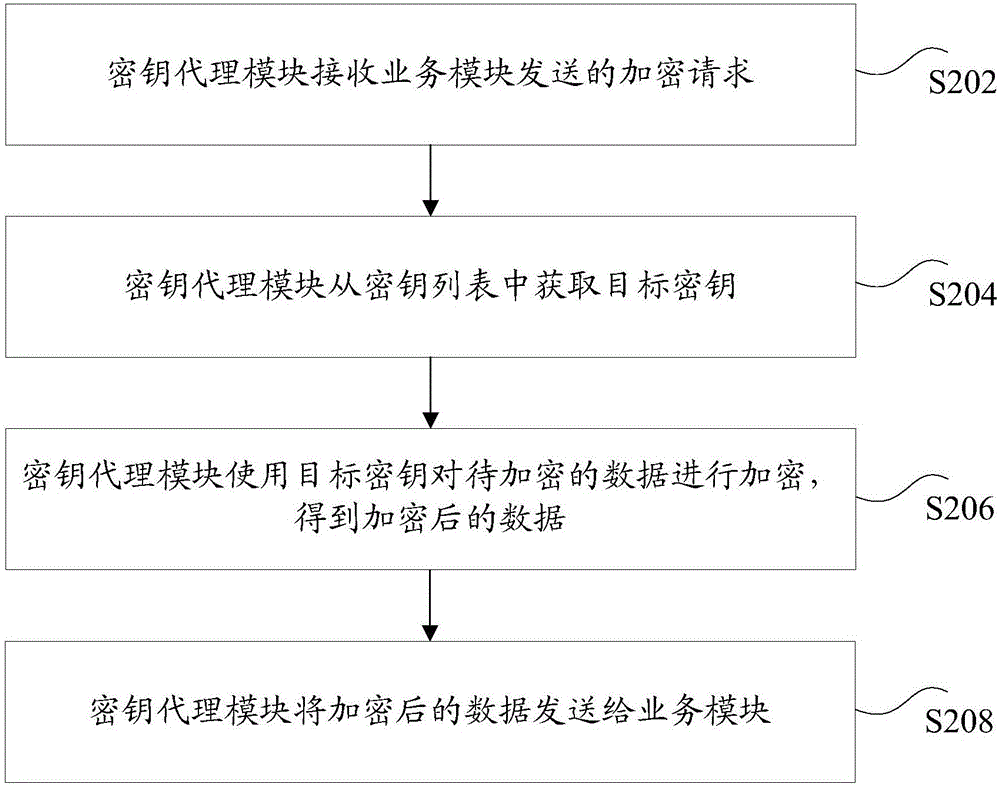
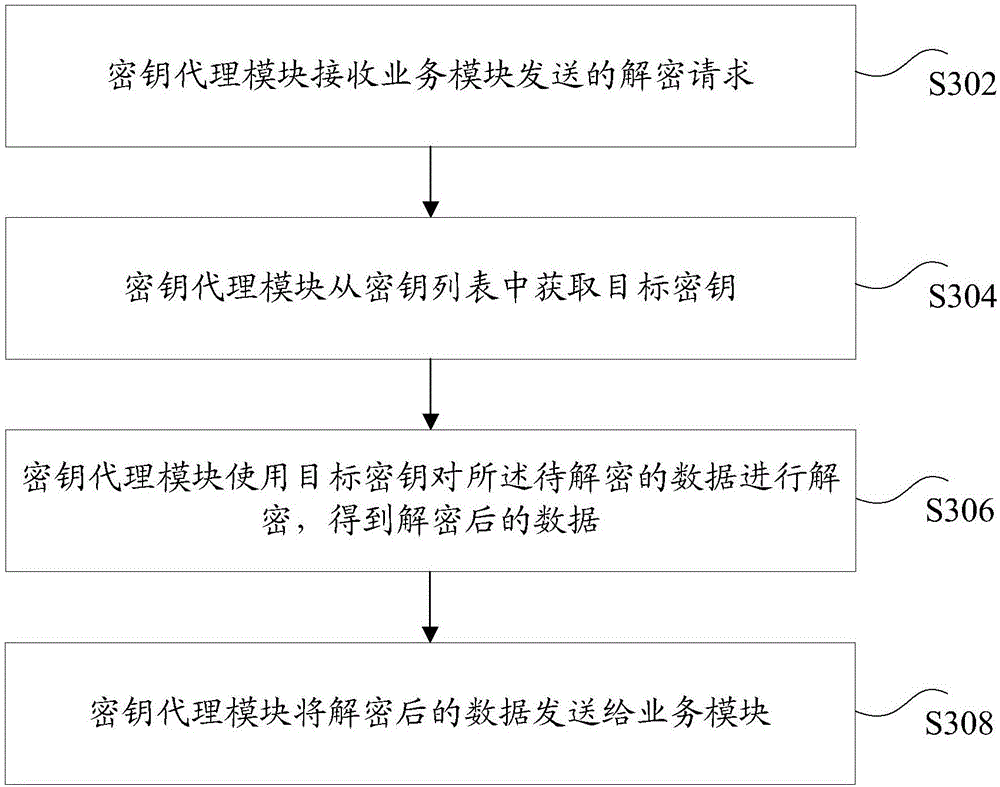
[0025] According to an embodiment of the present invention, an embodiment of a service encryption method is provided.
[0026] Optionally, in this embodiment, the above service encryption method can be applied to figure 1 In the hardware environment constituted by the server 102 and the terminal 104 as shown. Such as figure 1 As shown, the server 102 is connected to the terminal 104 through a network. The above-mentioned network includes but not limited to: a wide area network, a metropolitan area network or a local area network. The terminal 104 is not limited to a PC, a mobile phone, a tablet computer, and the like. The service encryption method in the embodiment of the present invention may be executed by the server 102, may also be executed by the terminal 104, and may also be executed jointly by the server 102 and the terminal 104. Wherein, the service encryption method of the embodiment of the present invention executed by the terminal 104 may also be executed by a cli...
Embodiment 2
[0166] According to an embodiment of the present invention, a service encryption device for implementing the above service encryption method is also provided. Image 6 is a schematic diagram of an optional service encryption device according to an embodiment of the present invention, such as Image 6 As shown, the device may include: a first receiving unit 601, a first obtaining unit 603, a first encrypting unit 605, and a first sending unit 607, wherein:
[0167] The first receiving unit 601 is set in the key agent module and is used for receiving the encryption request sent by the service module, wherein the encryption request carries the data to be encrypted.
[0168] The first acquiring unit 603 is arranged in the key agent module, and is used to acquire the target key from a key list, wherein the key list is pre-pulled from the key server.
[0169] The first encryption unit 605 is set in the key agent module, and is used to encrypt the data to be encrypted using the targ...
Embodiment 3
[0202] According to an embodiment of the present invention, a server or terminal for implementing the above service encryption (or service decryption) method is also provided.
[0203] Figure 8 is a structural block diagram of a terminal according to an embodiment of the present invention, such as Figure 8 As shown, the terminal may include: one or more (only one is shown in the figure) processor 801 (such as the key proxy module in the above embodiment), memory 803, and transmission device 805 (such as the key agent module in the above embodiment) sending device), such as Figure 8 As shown, the terminal may also include an input and output device 807 .
[0204] Among them, the memory 803 can be used to store software programs and modules, such as the program instructions / modules corresponding to the service encryption (or service decryption) method and device in the embodiment of the present invention, and the processor 801 runs the software programs and modules stored i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com