Digital image secret sharing method, restoration method and devices
A secret sharing and image technology, applied in the field of image information hiding, which can solve the problem of low accuracy in recovering secret images
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
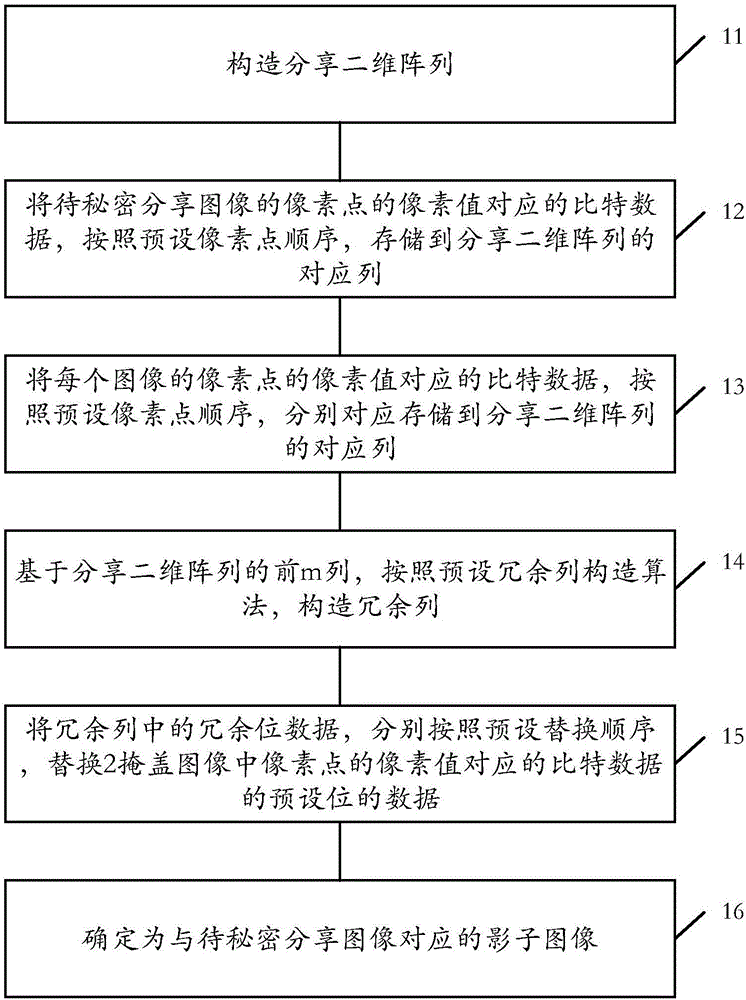
[0080] Embodiment 1 of the present invention provides a secret sharing method for a digital image. For an image to be shared secretly, based on m+1 masked images, the information of the image to be shared secretly is hidden in it, so as to achieve the purpose of secret sharing, as shown in figure 1 As shown, it specifically includes the following processing steps:
[0081] Step 11. Construct a shared two-dimensional array of (m-1)×(m+3), and use the elements of the shared two-dimensional array as the storage space block C i,j , i represents a row, j represents a column, and 0≤i
[0082] Wherein, the two-dimensional array can also be called a STAR code, the first m columns of which are information columns, and the last three columns are check columns.
[0083] Step 12. Obtain the image to be secretly shared, and store the bit data corresponding to the pixel value of the pixel of the image to be secretly shared in the R of the shared...
Embodiment 2
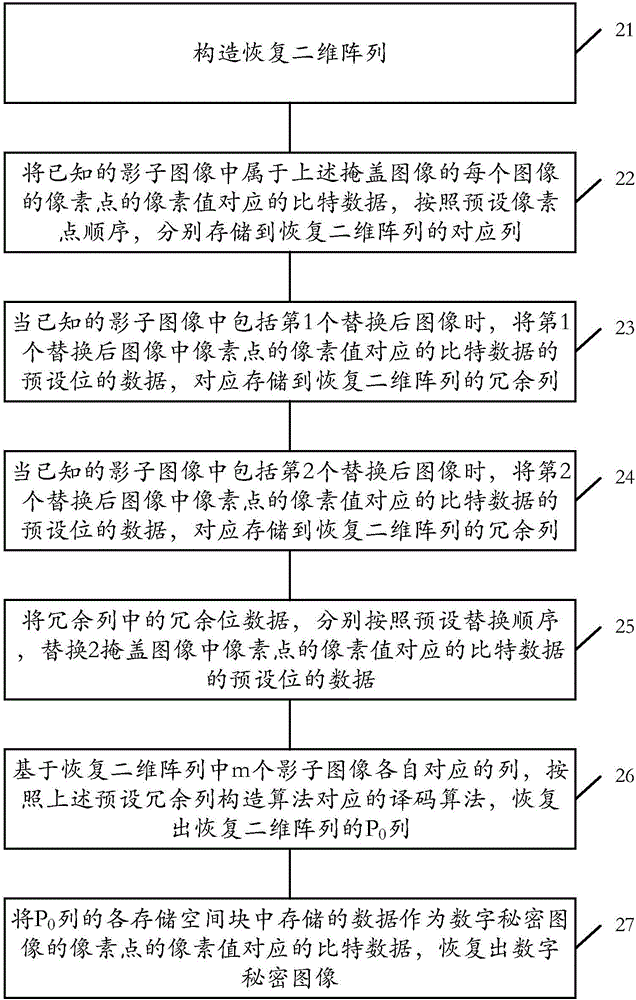
[0106] After the digital image is secretly shared through the digital image secret sharing method provided in the above-mentioned embodiment 1, m+1 shadow images are obtained. This embodiment 2 is based on the above-mentioned sharing method, and accordingly, a digital secret image restoration method is proposed. Based on at least any m shadow images in the m+1 shadow images, the recovery of the shared digital secret image can be realized, K=m, N=m+1 can be set, (K, N) is provided by the embodiment of the present invention The threshold value of the digital image secret sharing method and the recovery method, the specific value can be set according to the actual needs, and it only needs to meet the requirements in the method.
[0107] In the digital secret image recovery method provided by Embodiment 2 of the present invention, m shadow images in the above m+1 shadow images are known, as figure 2 As shown, specifically, the following steps may be included:
[0108] Ste...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More