Outsourcing access control method and system aiming at fog computing
An access control and fog computing technology, applied in the field of cloud storage services
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0044] A fog computing-oriented outsourcing access control method provided by the present invention will be described in detail below.
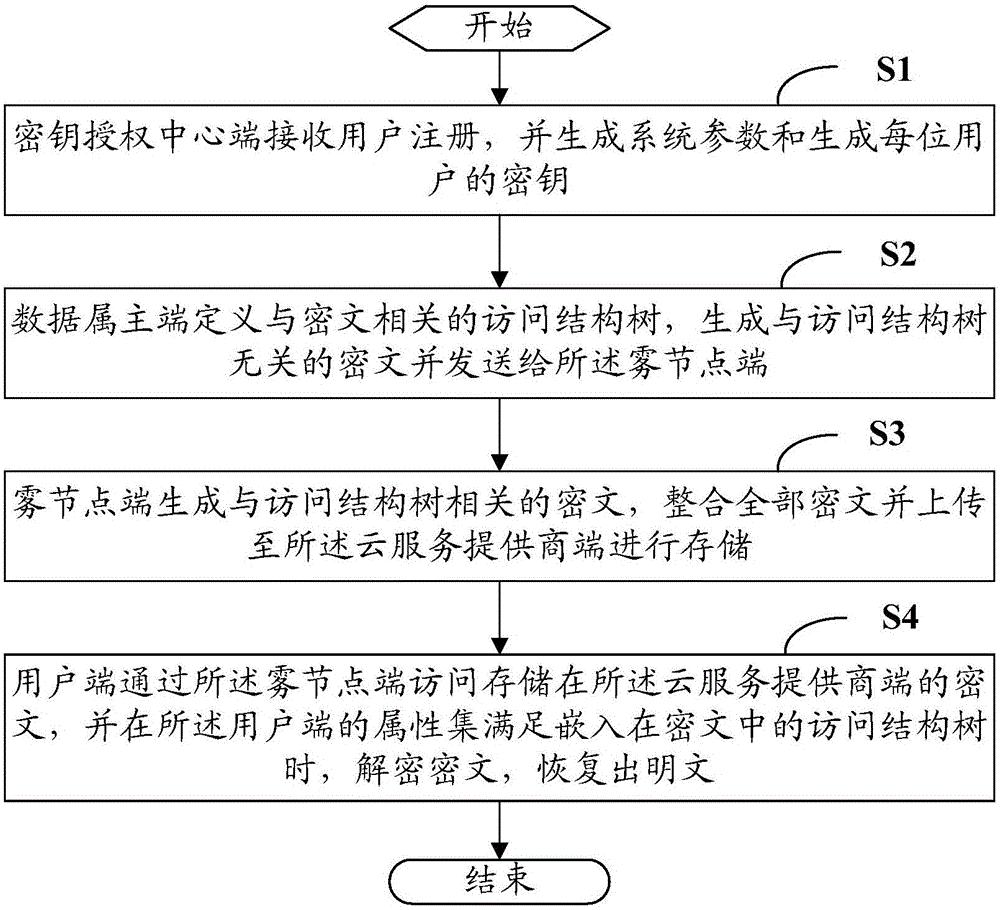
[0045] see figure 1 , is a flow chart of a fog computing-oriented outsourcing access control method in an embodiment of the present invention.
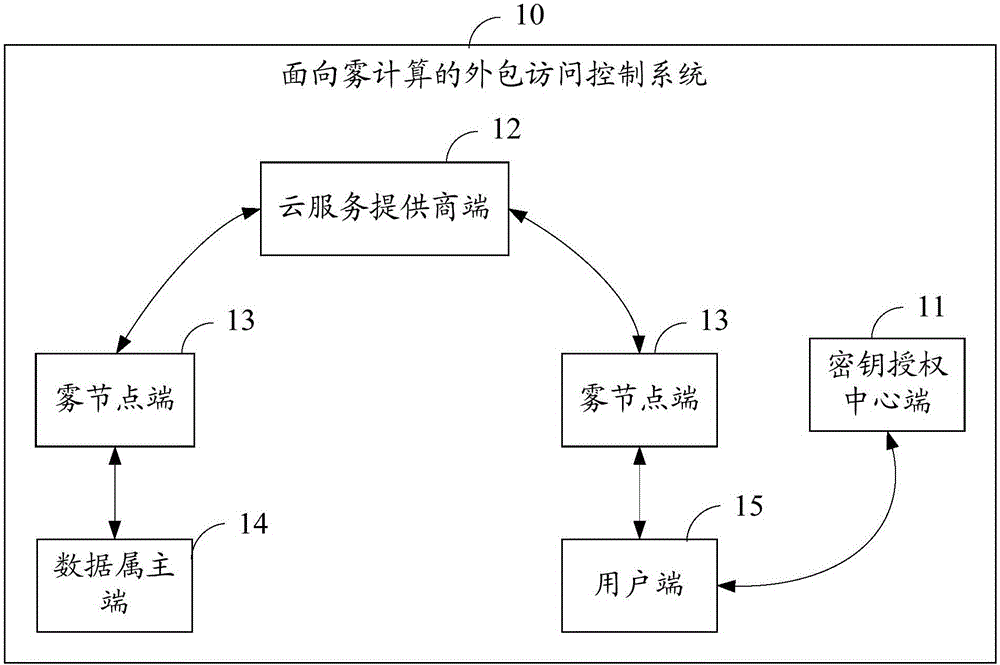
[0046] In this embodiment, the outsourced access control method oriented to fog computing is applied to the key authority center (Key Authority, KA) end, cloud service provider (Cloud Service Provider, CSP) end, fog node (FogNodes) end, An outsourced access control system for fog computing, including the data owner (Dat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More