Authorization method and system of virtual key and server
A virtual key and server technology, applied in the field of system and server, virtual key authorization methods, can solve problems such as low security and insufficient guarantee of authorization process security, user information privacy, etc., to achieve convenient operation and improve user experience sense, improve the effect of safety
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] It should be noted that, in the case of no conflict, the embodiments of the present invention and the features in the embodiments can be combined with each other.
[0040] The present invention will be described in detail below with reference to the accompanying drawings and examples.
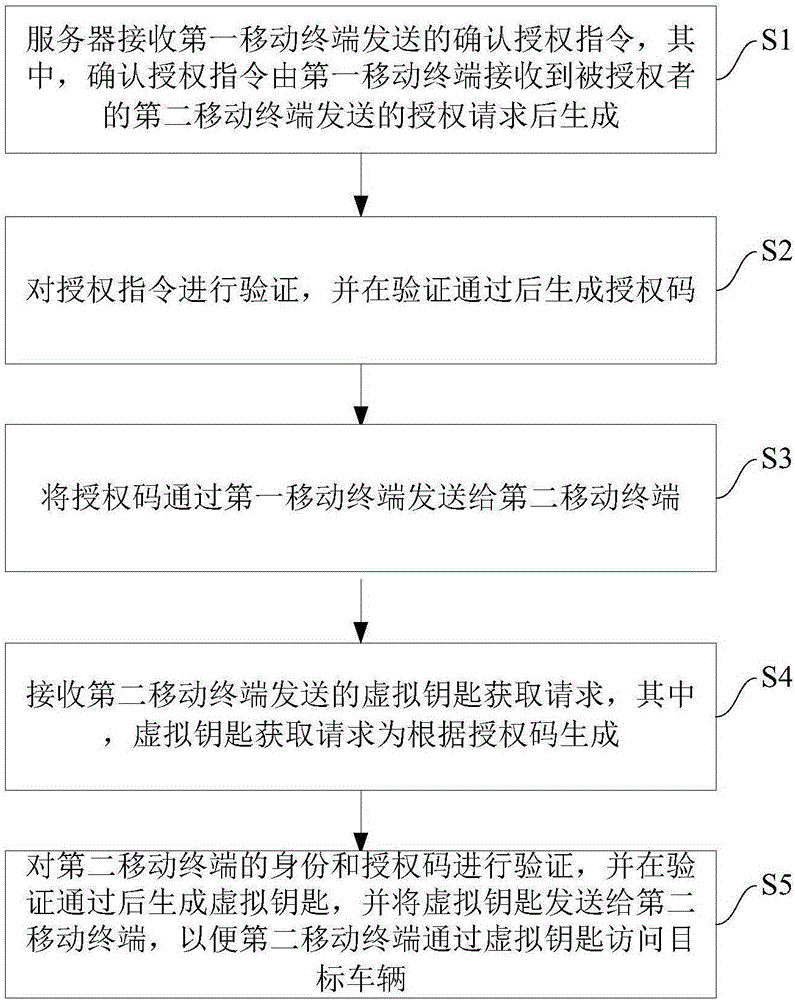
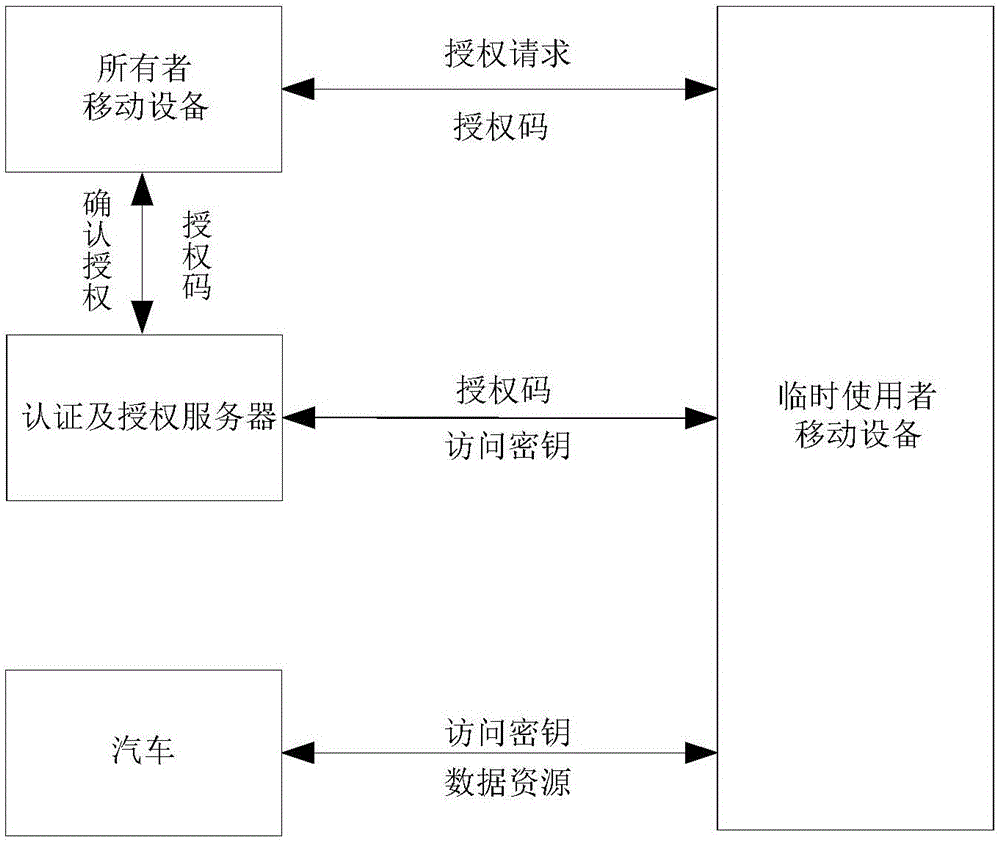
[0041] figure 1is a flow chart of a virtual key authorization method according to an embodiment of the present invention. figure 2 It is a schematic block diagram of a virtual key authorization method according to an embodiment of the present invention.
[0042] Such as figure 1 shown, combined with figure 2 , the authorization method of the virtual key in the embodiment of the present invention comprises the following steps:
[0043] Step S1: The server receives the authorization confirmation instruction sent by the first mobile terminal, wherein the authorization authorization instruction is generated by the first mobile terminal after receiving the authorization request sent by ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More