A virtual machine abnormal behavior detection method and system based on io sequence
A detection method and virtual machine technology, applied in the field of virtualization security, can solve the problems of performance loss, complex security threats, frequent IO read and write operations, etc., and achieve the effect of reducing performance loss and protecting security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
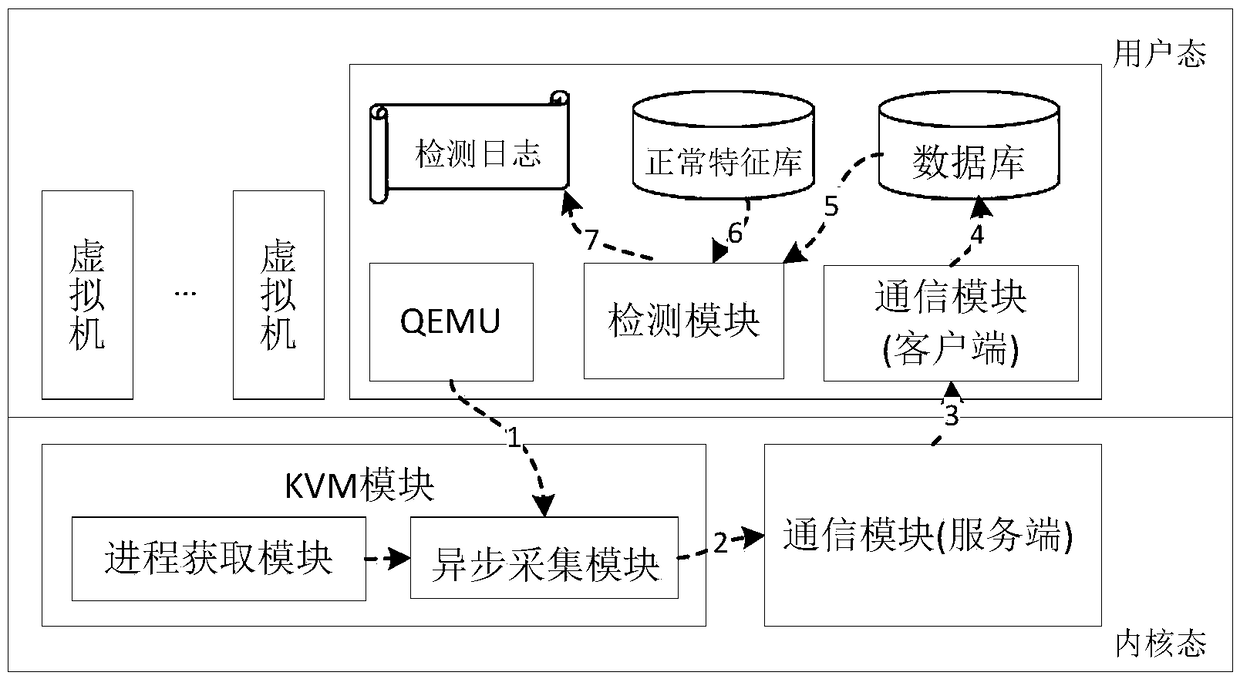
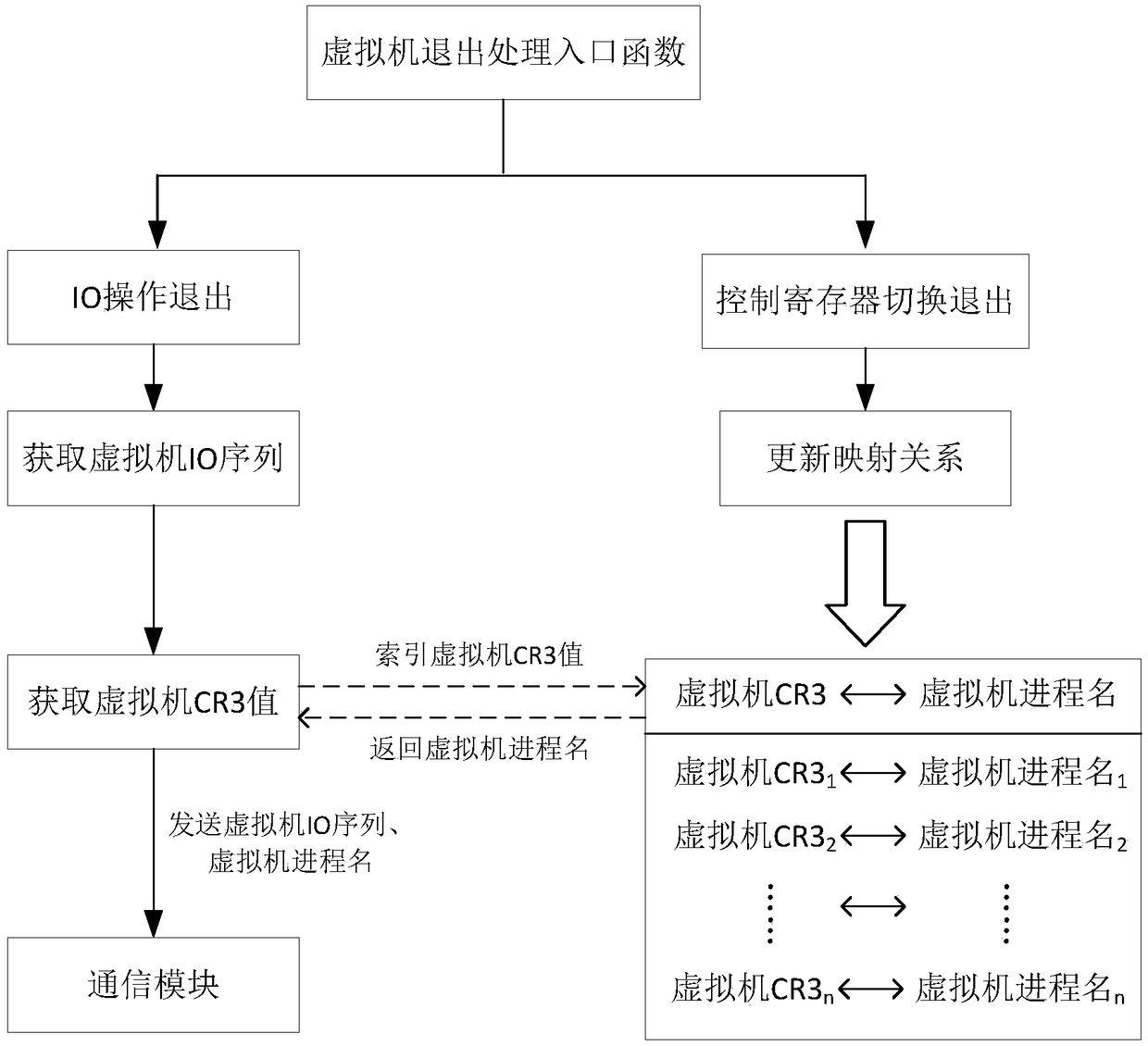
[0030] attached figure 1 The overall architecture diagram of the IO sequence-based KVM (Kernel-based Virtual Machine) virtual machine abnormal behavior detection system in the present invention is given. Such as figure 1 As shown, the system can be used to detect malicious behaviors inside the virtual machine and prevent known virtual machine escape attacks in time, including asynchronous acquisition module, process acquisition module, communication module and detection module.
[0031] The asynchronous acquisition module intercepts the IO simulation operation of the virtual machine, extracts the required virtual machine IO sequence and saves it in the data buffer area, wakes up the custom kernel thread located in the communication module, and restores the normal execution process of the VMM.
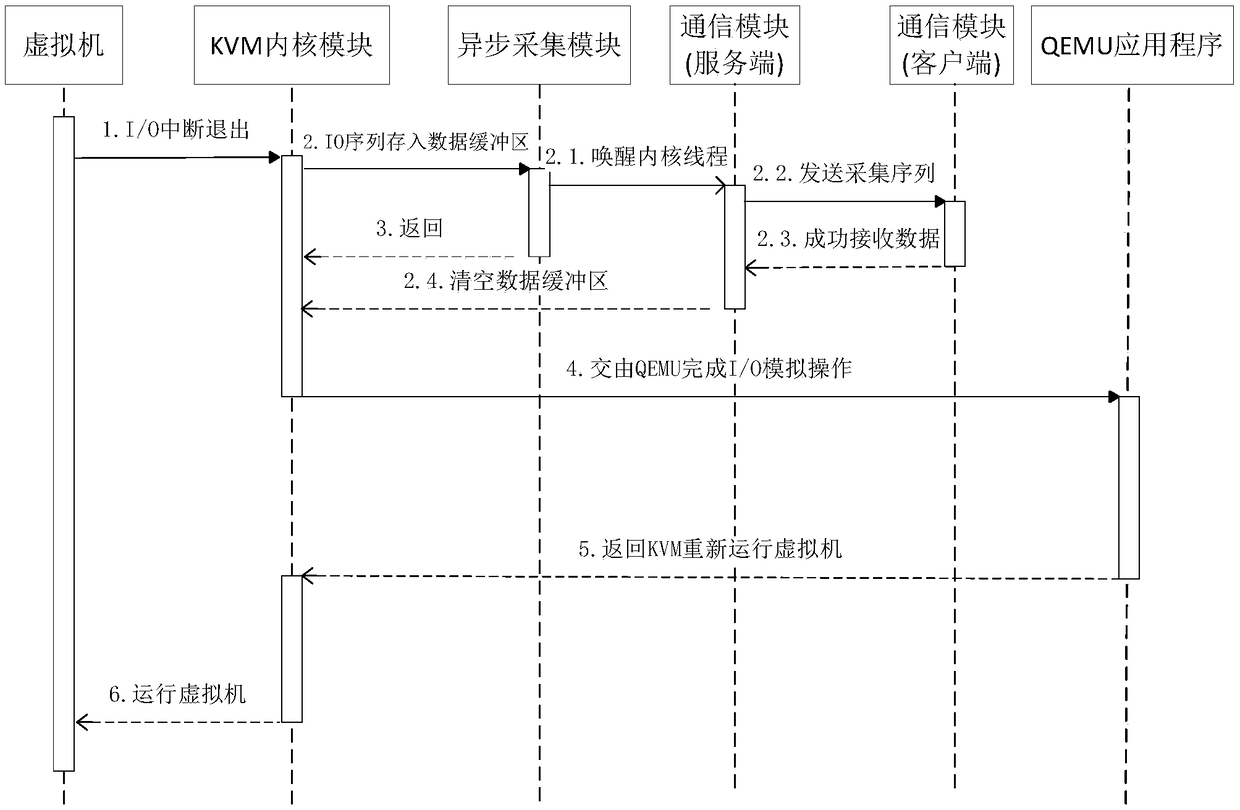
[0032] attached figure 2 The timing ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More