An Efficient Pseudonym Management and Data Integrity Protection Protocol
A data integrity and pseudonym technology, applied in the field of IoT security, to reduce communication time and computing cost, provide location privacy protection, and balance the false recognition rate.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] The invention is further illustrated in conjunction with the accompanying drawings and specific embodiments.
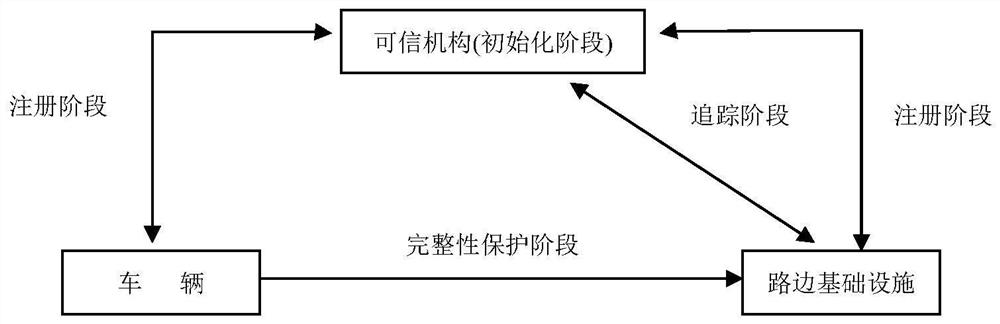
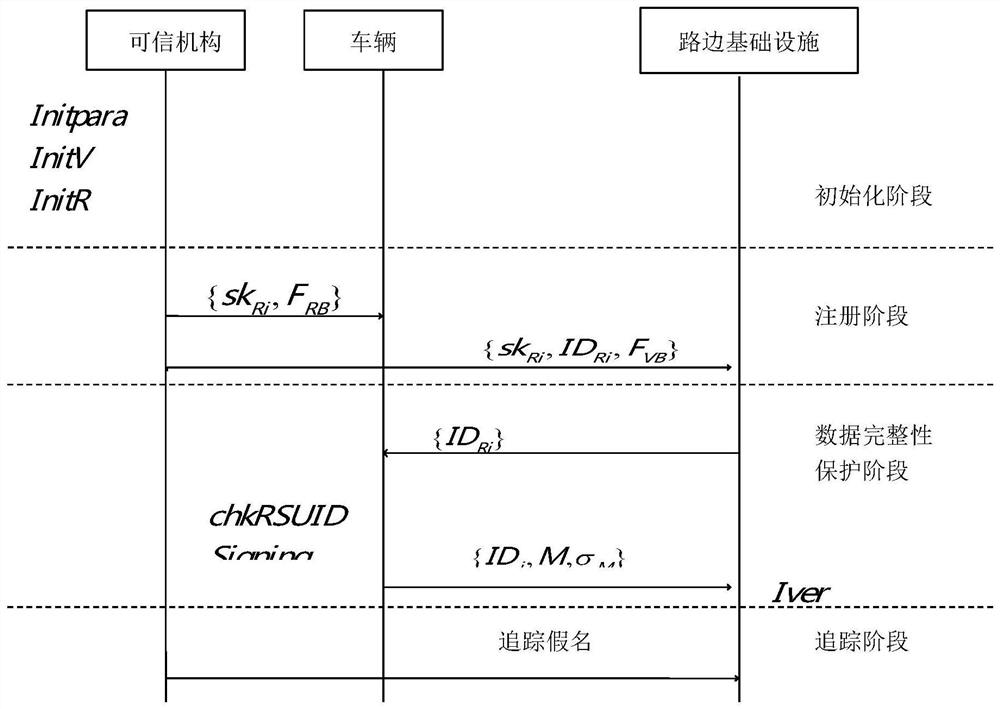
[0048] Such as figure 1 As shown, the present invention relates to three entities, content between these entities, and four stages included in the protocol. The three entities defined by the present invention are: trusted mechanisms (TA), VHICLE and roadside infrastructure (RSU). The trusted mechanism generates a key material and transmits the corresponding key material to the vehicle and the roadside infrastructure. After the vehicle gets the key and public parameters distributed by the trusted mechanism, the message to be sent is sent to the roadside infrastructure after using the signature algorithm to generate a signature. After receiving the message, the roadside infrastructure needs to verify the message using the signature algorithm. The final trusted mechanism can track the vehicle by monitoring the pseudonym transport path, and finally obtain real identity...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More