Method for BMC reliable configuration with access control function
A configuration method and access control technology, applied in computer security devices, instruments, electrical digital data processing, etc., can solve problems such as security risks, low password complexity, improper security configuration, etc., and achieve the effect of ensuring credibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0058] In order to make the purpose, features and advantages of the present invention more obvious and understandable, the technical solutions protected by the present invention will be clearly and completely described below using specific embodiments and accompanying drawings. Obviously, the implementation described below Examples are only some embodiments of the present invention, but not all embodiments. Based on the embodiments in this patent, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of this patent.
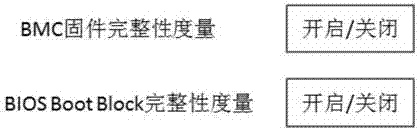
[0059] This embodiment provides a BMC trusted configuration method with an access control function, such as figure 1 As shown, BMC trusted configuration methods include:
[0060] S1: Turn on the BMC trusted function module;
[0061] S2: The configured BMC benchmark value;
[0062] S3: Present the trusted status of BMC firmware;
[0063] S4: Presenting a trusted state of the BIOS.
[0...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More