A Method for Constructing Quantum Hash Functions Based on Controlled Alternating Quantum Walks on a Two-dimensional Plane
A two-dimensional plane, hash function technology, applied in the field of quantum hash function, can solve problems such as difficulties
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] Below in conjunction with accompanying drawing and specific embodiment, further illustrate the present invention, should be understood that these examples are only for illustrating the present invention and are not intended to limit the scope of the present invention, after having read the present invention, those skilled in the art will understand various aspects of the present invention All modifications of the valence form fall within the scope defined by the appended claims of the present application.
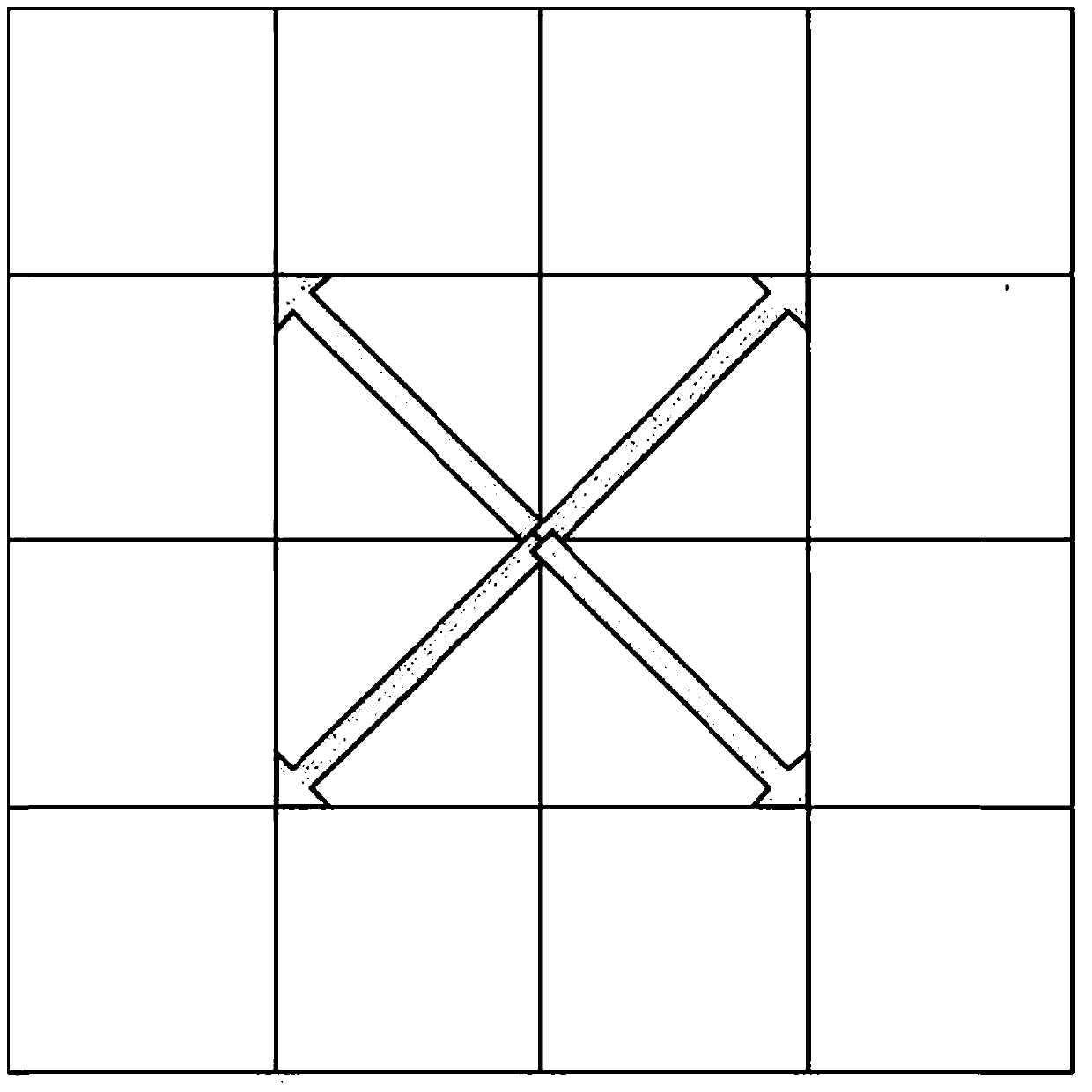
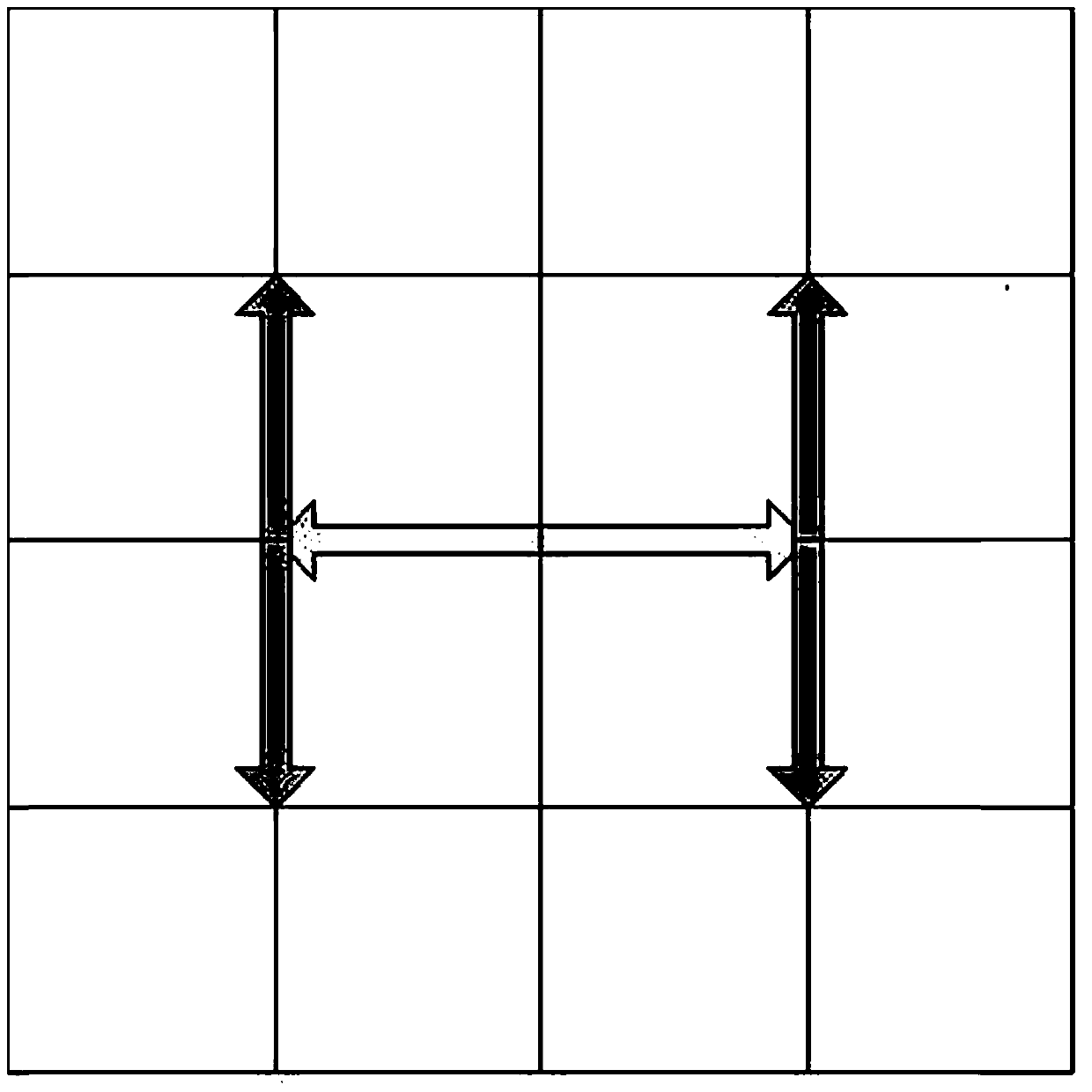
[0026] A method for constructing quantum hash functions based on controlled alternating quantum walks on a two-dimensional plane, such as figure 2 shown, including the following steps:
[0027] Step 1, if you want to generate a 200-bit hash value, select N 1 =N 2 =5, k=8, making N 1 N 2 k=200. Then randomly select two parameters θ in the range of (-π / 2, π / 2) 0 = π / 3 and θ 1 = π / 5, generate two coin toss operations C 0 and C 1 :
[0028] and
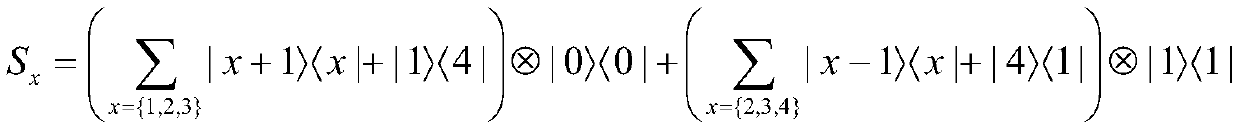
[0029] S...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More