Intelligent card safety authentication method and intelligent card safety authentication system on basis of data and short message technologies
A security authentication, smart card technology, applied in the field of information and communication, can solve the problems of inconsistent user name and password rules, great impact on user experience, forgetting passwords, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0059] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
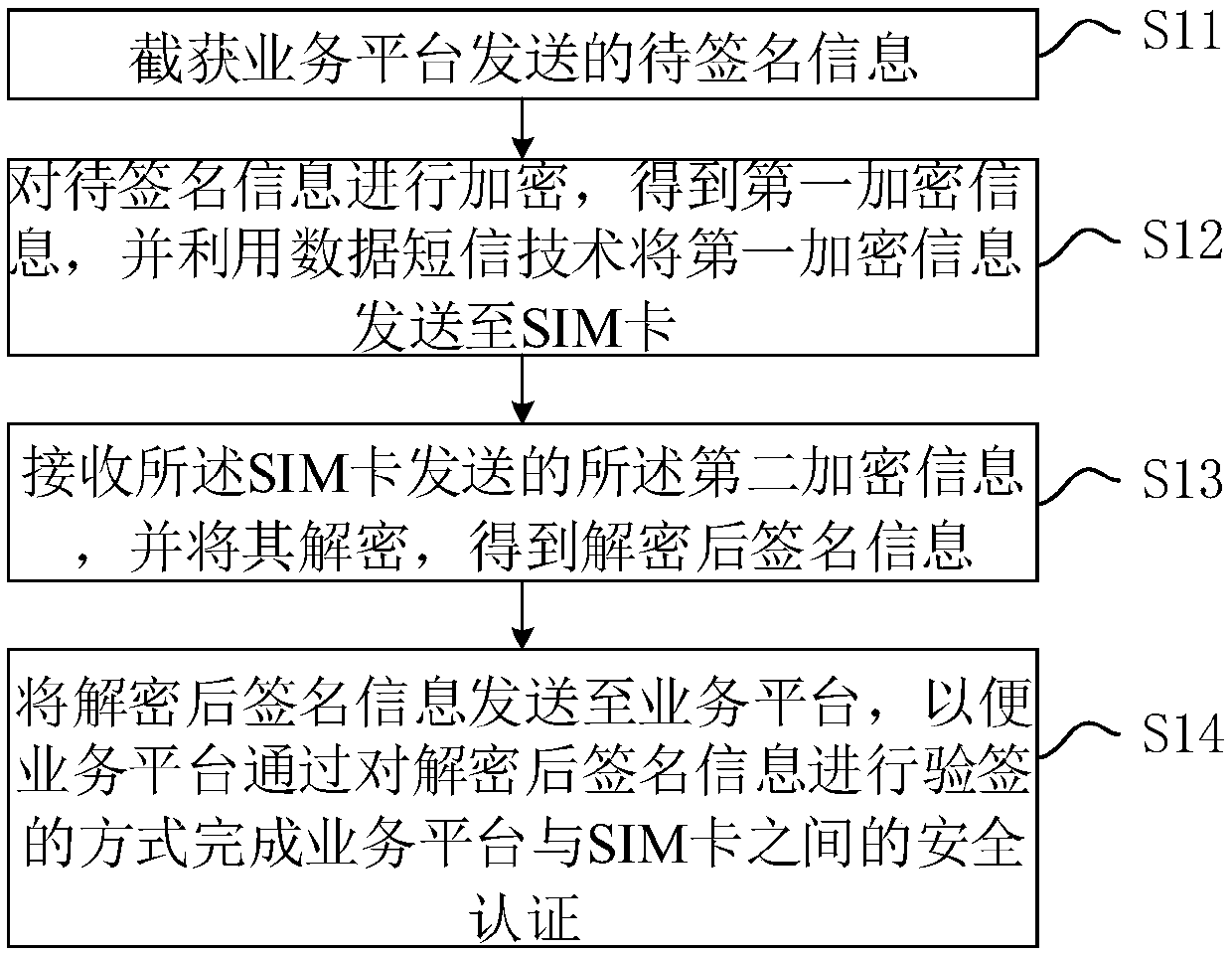
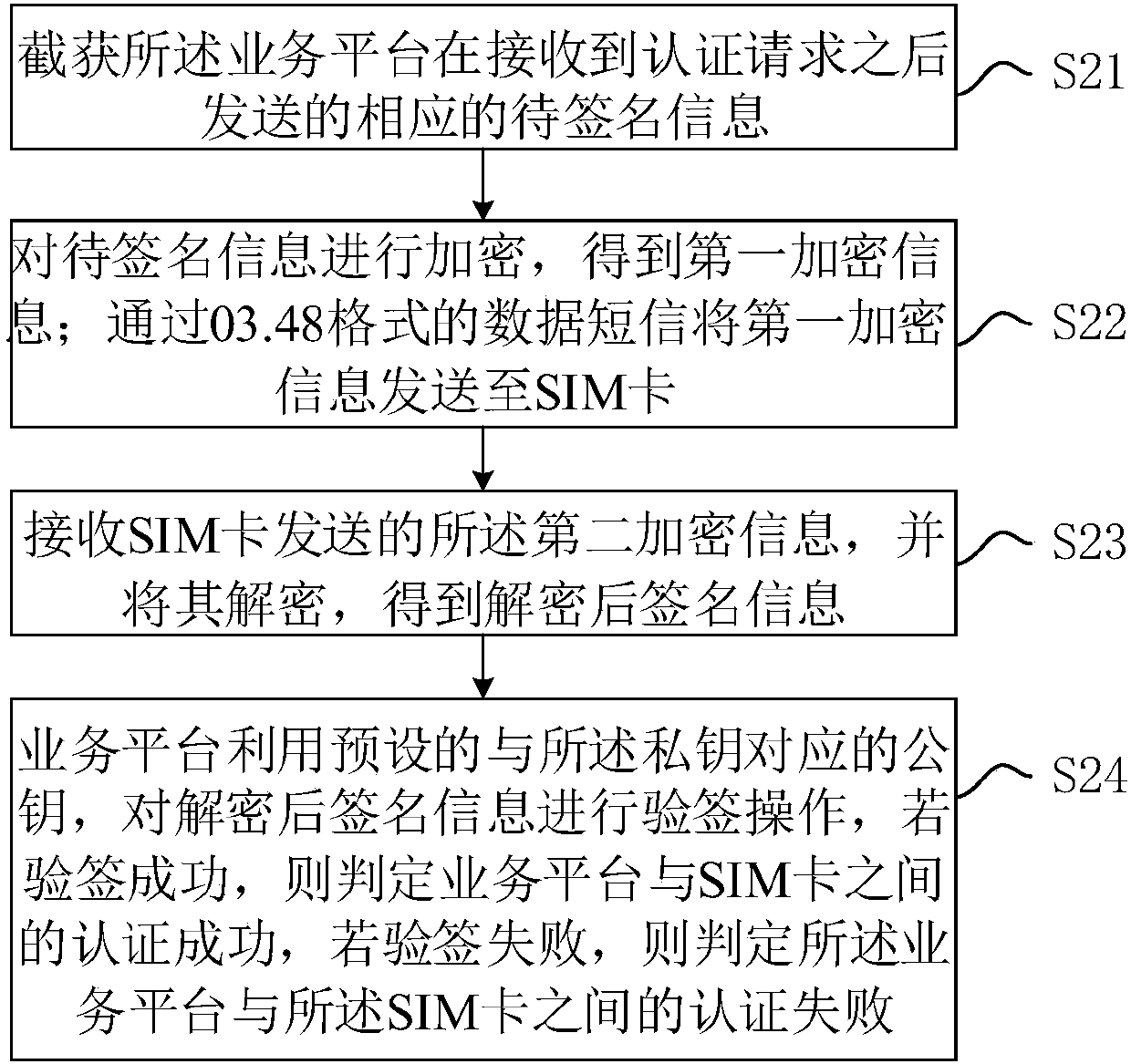
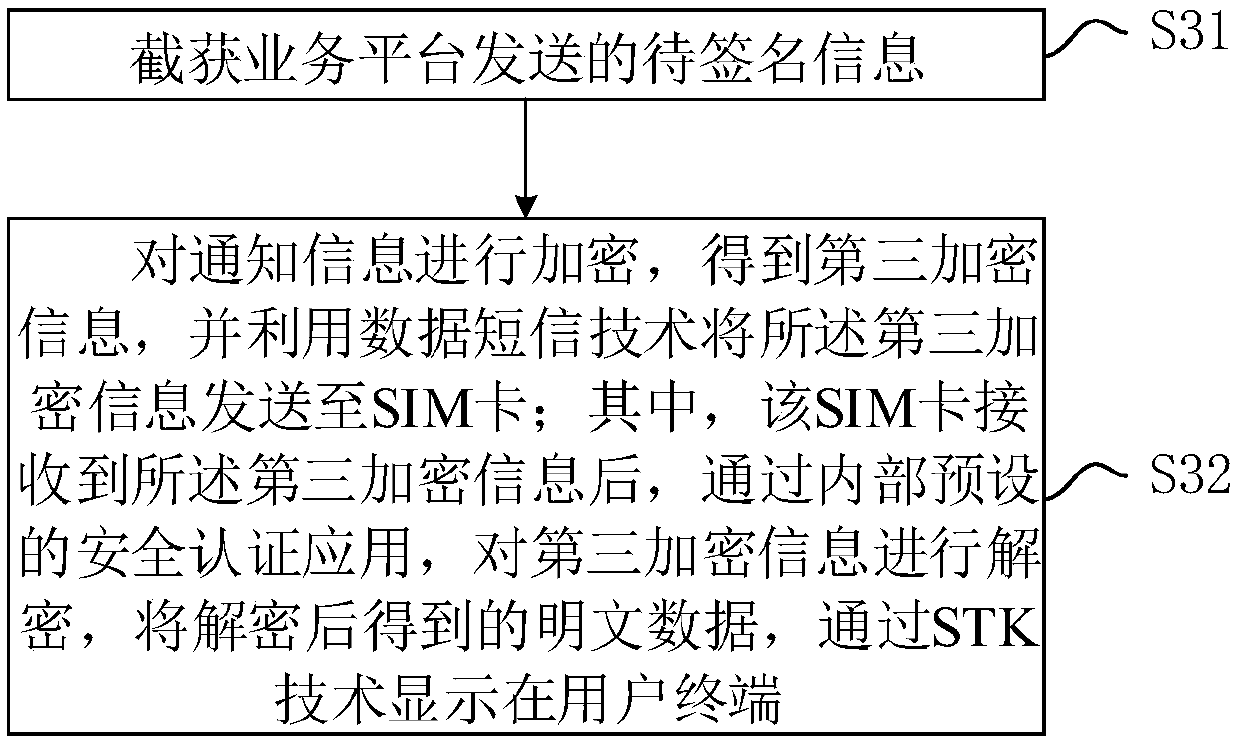
[0060] The embodiment of the present invention discloses a smart card security authentication method based on data message technology, see figure 1 As shown, the method is applied to the security service platform, including:
[0061] Step S11: Intercept the information to be signed sent by the service platform.
[0062] Among them, the above-mentioned business platforms include but are not limited to platforms such as websites and APPs.
[0063] In this embo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More