An authentication method and device
A technology for authentication and authentication request, applied in the field of data communication, which can solve problems such as hidden dangers, inflexible authentication schemes, and changes in authentication schemes.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0045] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the drawings in the embodiments of the present invention.
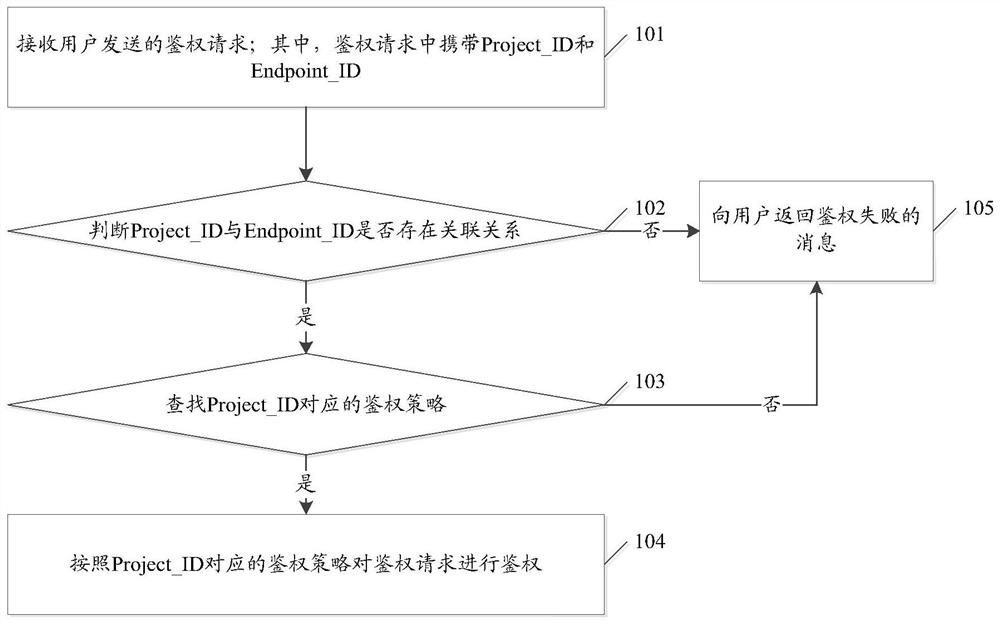
[0046] figure 1It is a schematic diagram of the implementation flow of the authentication method in the embodiment of the present invention. Such as figure 1 As shown, the authentication method may include the following steps:
[0047] Step 101. Receive an authentication request sent by a user; wherein, the authentication request carries Project_ID and Endpoint_ID.
[0048] In a specific embodiment of the present invention, three data tables for authenticating the authentication request may be stored in advance, namely: Policy data table; Policy_Association data table and Policy_Strategy data table. Specifically, the data structure of the Policy data table may be as shown in Table 1 below:
[0049]
[0050] Table 1
[0051] Among them, in the above Table 1: ID is used ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More