Method and system for executing data access authorization on user
A technology of data access and data authority, applied in the field of communication, can solve problems such as inability to know data, storage, and inability to provide data-oriented authority management mode, so as to improve authorization efficiency and ensure authorization accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
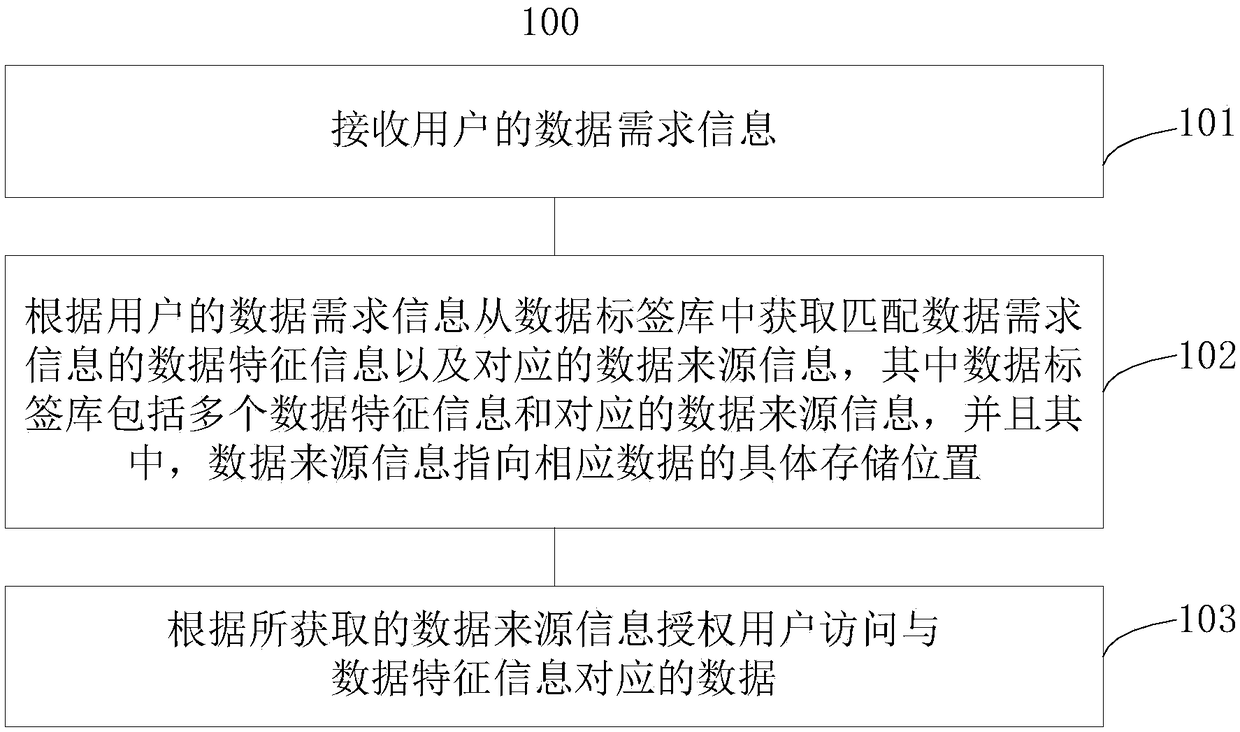
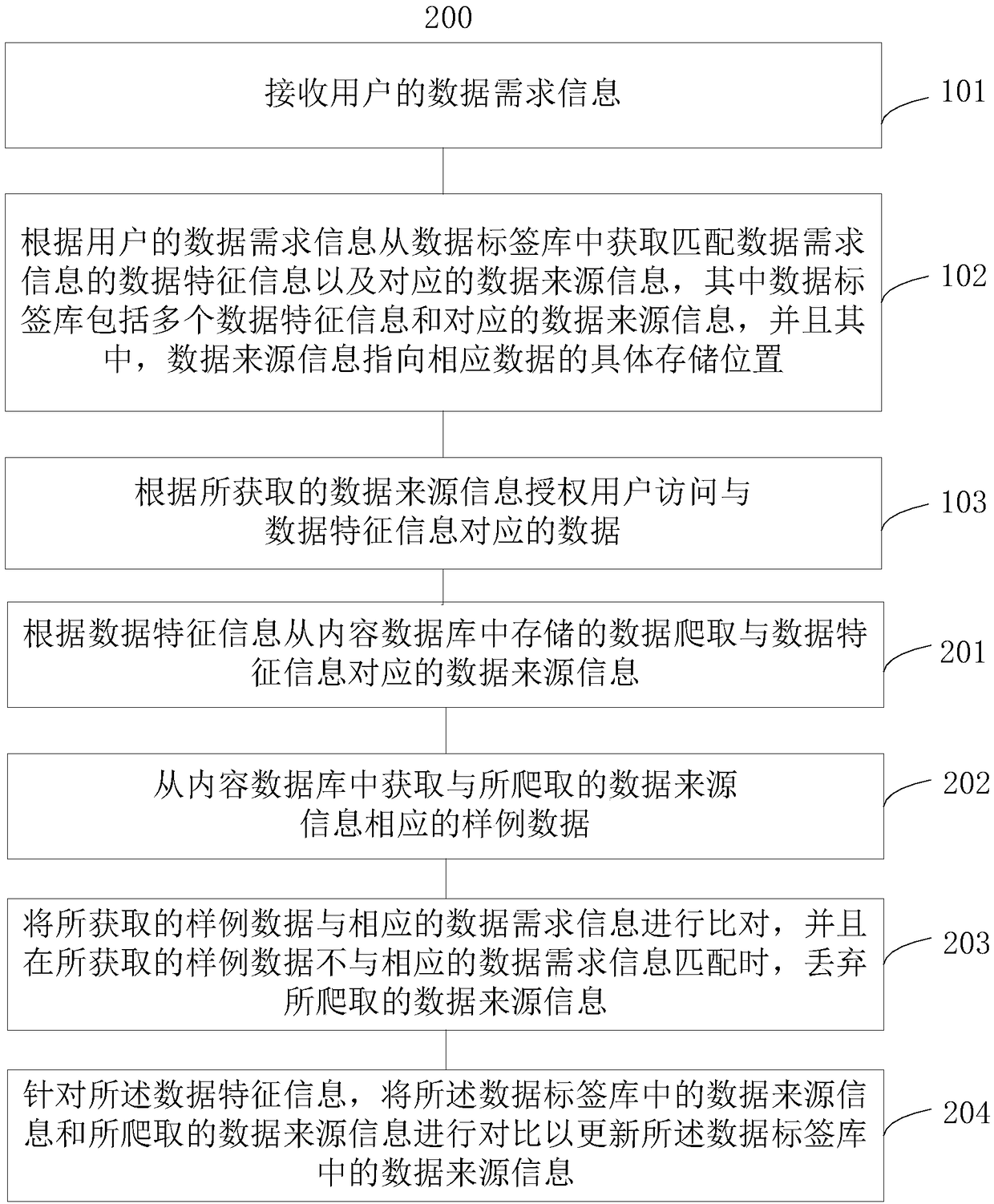
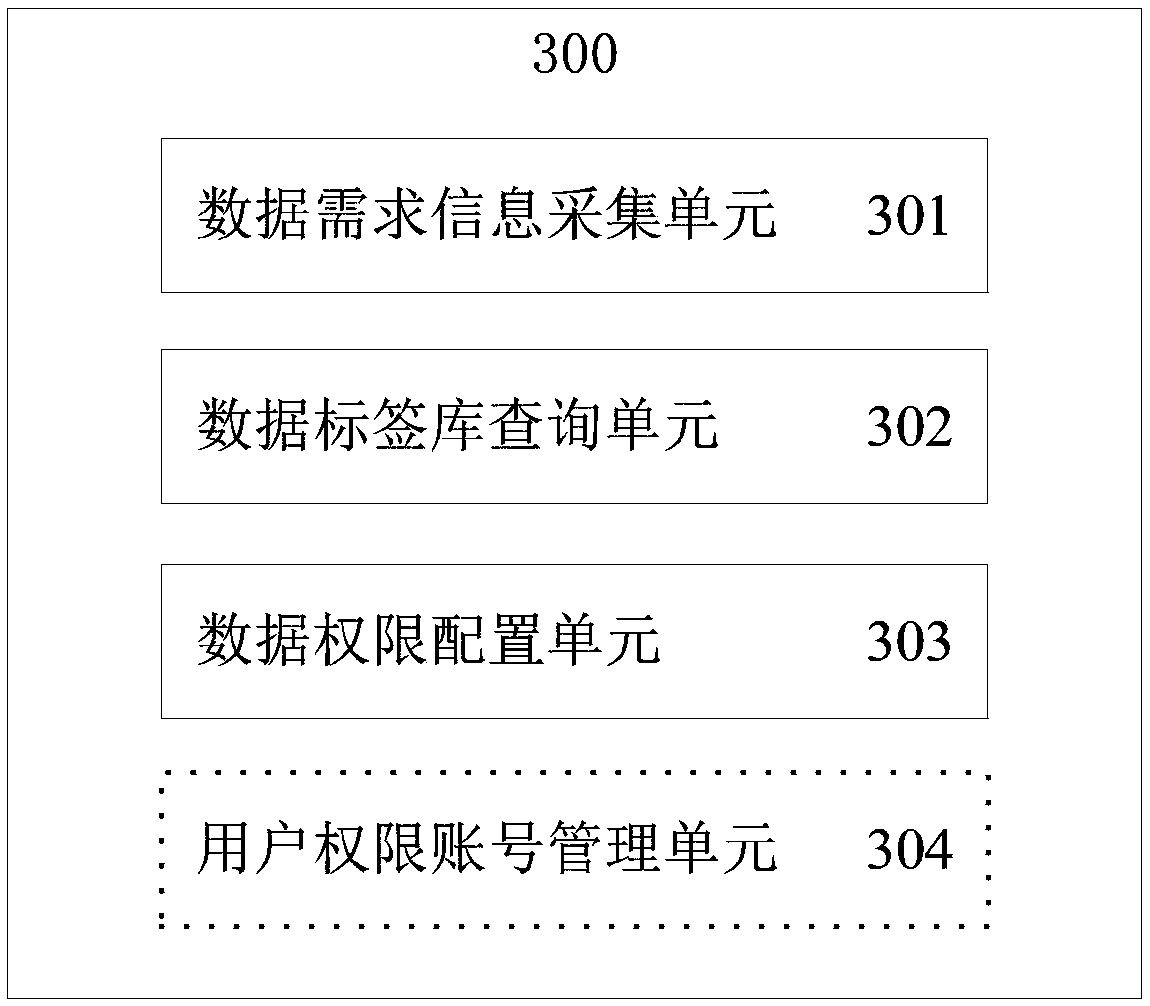
Method used
Image
Examples
Embodiment Construction
[0014] Features and exemplary embodiments of various aspects of the present disclosure will be described in detail below. The following description covers numerous specific details in order to provide a thorough understanding of the present invention. It will be apparent, however, to one skilled in the art that the present invention may be practiced without some of these specific details. The following description of the embodiments is only to provide a clearer understanding of the present invention by showing examples of the present invention. The present invention is by no means limited to any specific configuration set forth below, but covers any modification, substitution and improvement of related elements or components without departing from the spirit of the invention.
[0015] At present, there are two ways to manage Hadoop permissions. One is to assign the read and write permissions of HDFS files to users through complex command line operations, so that users have co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More