Three-dimensional mapping fast image encryption method
An encryption method and image technology, applied in the field of information security, can solve the problems of inability to resist plaintext attacks and weak security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
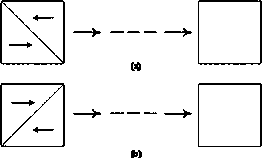
[0088] Two-dimensional mapping principles and examples such as figure 1 , figure 2 shown. The image is regarded as an array, and the principle of mapping is to divide the square image into two upper and lower isosceles triangles in a diagonal direction. Utilizing the difference between the number of pixels in adjacent columns of each triangle, the pixels of each column are sequentially inserted between two adjacent pixels in adjacent columns. Repeating this process, the original image is stretched into a long N 2 straight line. .
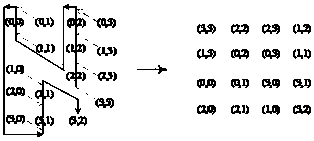
[0089] figure 2 Take a 4*4 graph as an example. First divide the image into upper and lower isosceles triangles. In the upper triangle, pixel (3,3) is inserted before pixel (2,2), pixel (2,3) is inserted between pixel (2,2) and pixel (1,2), and pixel (1,3) ) pixel (1,2) pixel (0,2), repeat the above operations to form pixel rows: (3,3), (2,2), (2,3), (1,2), (1,3 ),(0,2)....In the lower triangle, pixel (3,0) is inserted before pixel (3,1)...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More