Anonymous network tracing method based on controlled node
A controlled node and anonymous network technology, applied in the field of information security, can solve problems such as destruction
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] In order to make the purpose, content, and advantages of the present invention clearer, the specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments.
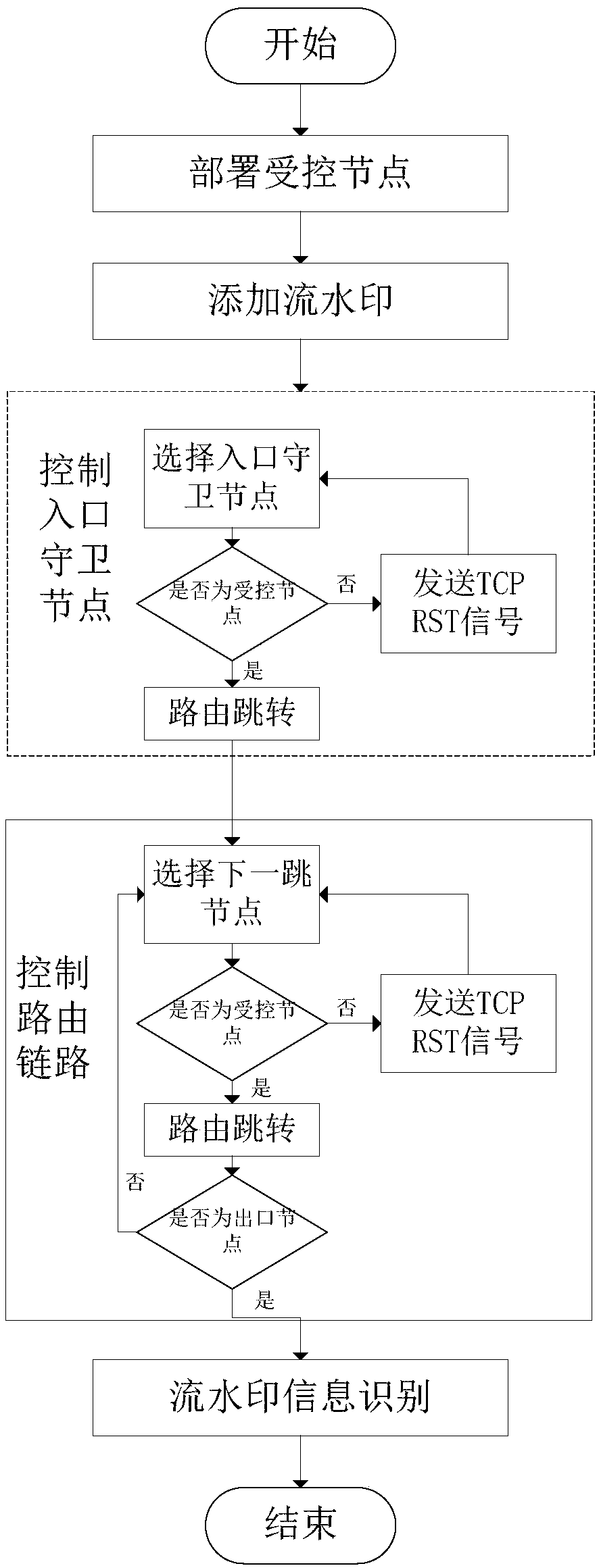
[0028] figure 1 Shown is the flow chart of the anonymous network traceability method based on the controlled node of the present invention, as figure 1 As shown, a controlled node-based anonymous network traceability method of the present invention includes:
[0029] Step 1: The attacker deploys controlled Tor relay nodes, including:
[0030] Step 1.1: Deploy controlled entry guard nodes;
[0031] The entrance guard node is the first node in the entire Tor anonymous network, and its security is related to the security of the entire communication link and the concealment of the client. In order for the client to choose a controlled entry guard node, the node needs to meet two conditions at the same time. First, the n...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More