Data stream encryption method, data stream decryption method
An encryption method and data stream technology, applied in the field of information security, can solve the problems of low security, slow computing speed, and easy to be broken, and achieve the effect of ensuring security, improving encryption level, and reducing the amount of computing data.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0069] In order to make the object, technical solution and advantages of the present invention clearer, the implementation manner of the present invention will be further described in detail below in conjunction with the accompanying drawings.
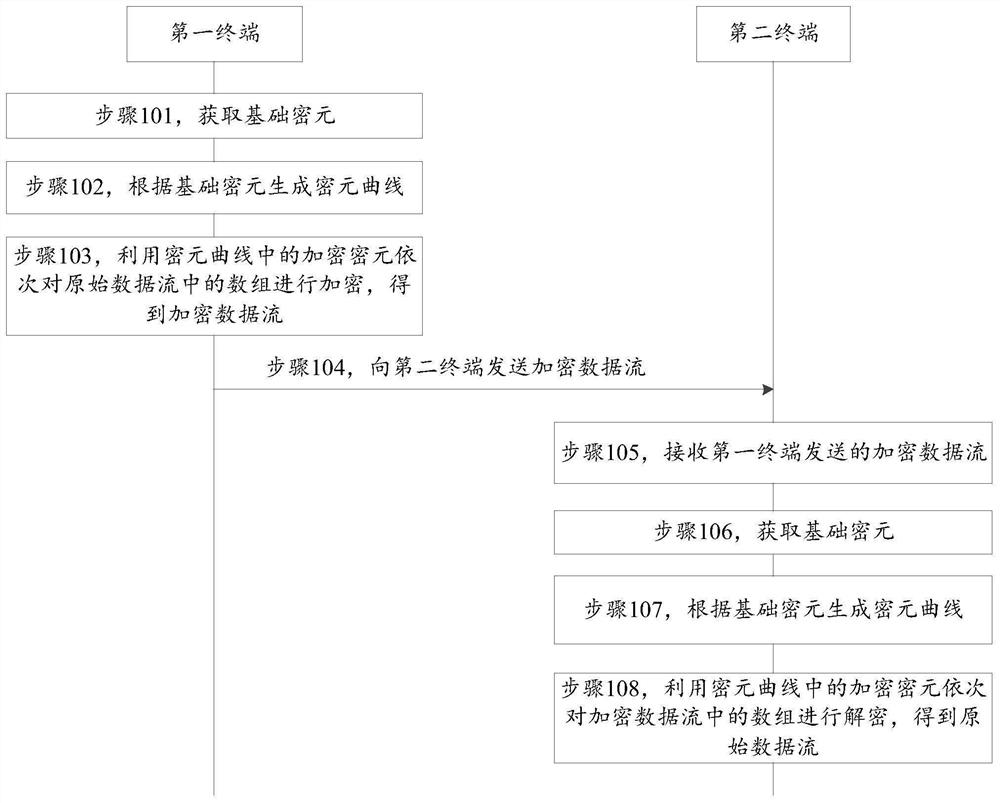
[0070] Please refer to figure 1 , which shows a flowchart of a data stream processing method provided by an embodiment of the present invention. The data stream processing method is suitable for information exchange terminals. Optionally, the terminal is an electronic device such as a mobile phone, a tablet computer, an e-book reader, an MP3 player, an MP4 player, a desktop computer, and a portable computer. The terminal can encrypt and decrypt the data stream.
[0071] Such as figure 1 As shown, the data stream processing method may include the following steps:
[0072]In step 101, the first terminal obtains a basic cipher.
[0073] In step 102, the first terminal generates a cipher curve according to the basic cipher.
[0074] ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More