Key management method and electronic device for each server generating key components
A technology for generating keys and servers, which is applied in the field of data security, can solve problems such as increasing the burden on key servers, no solution is proposed, and low flexibility, so as to achieve the effect of improving security and flexibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example 1
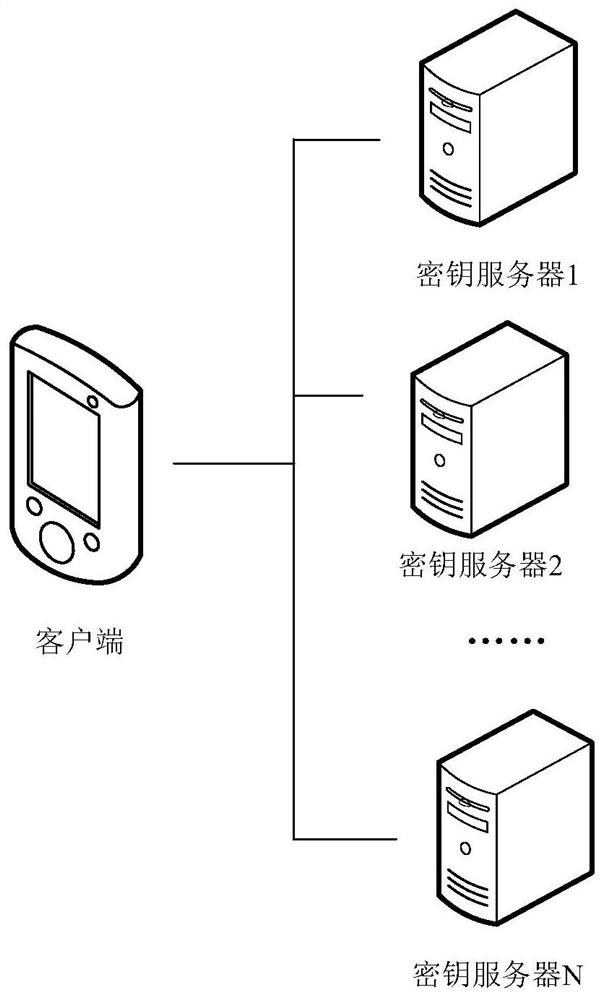
[0129] In this example, a key management method based on secure two-party computing that is generated and stored by multiple servers is provided, a key management scheme based on secure multi-party computing is applied to key generation, Use, store, backup, restore, refresh and other operations.
[0130] Specifically, different servers independently generate key components, and finally use the two-party MPC to generate the public key; through the two-party MPC, use the server to calculate the signature. Operations such as key generation, use, storage, backup, recovery, and refresh in this situation are explained as follows:
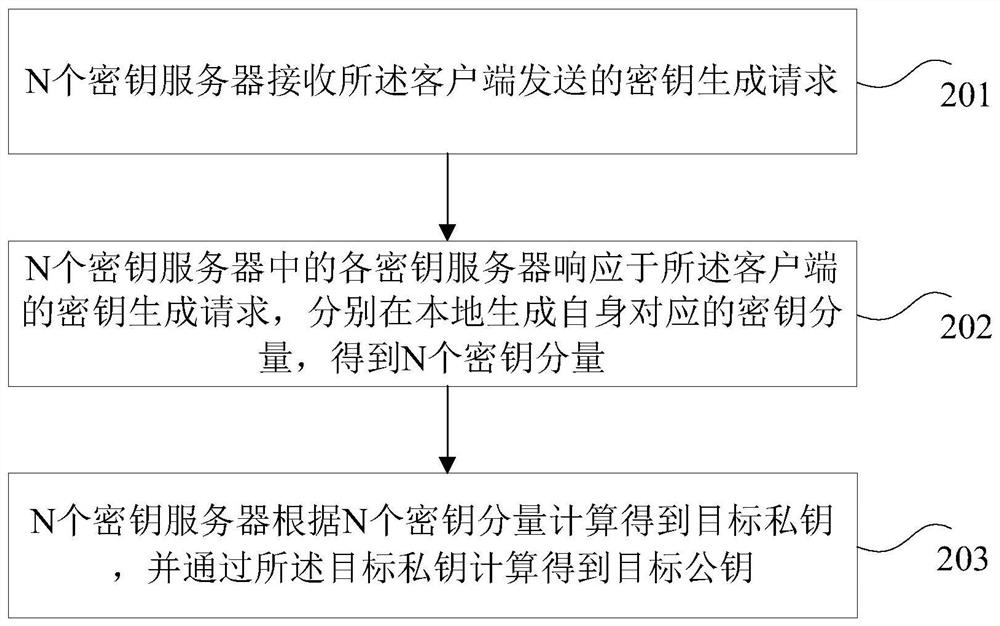
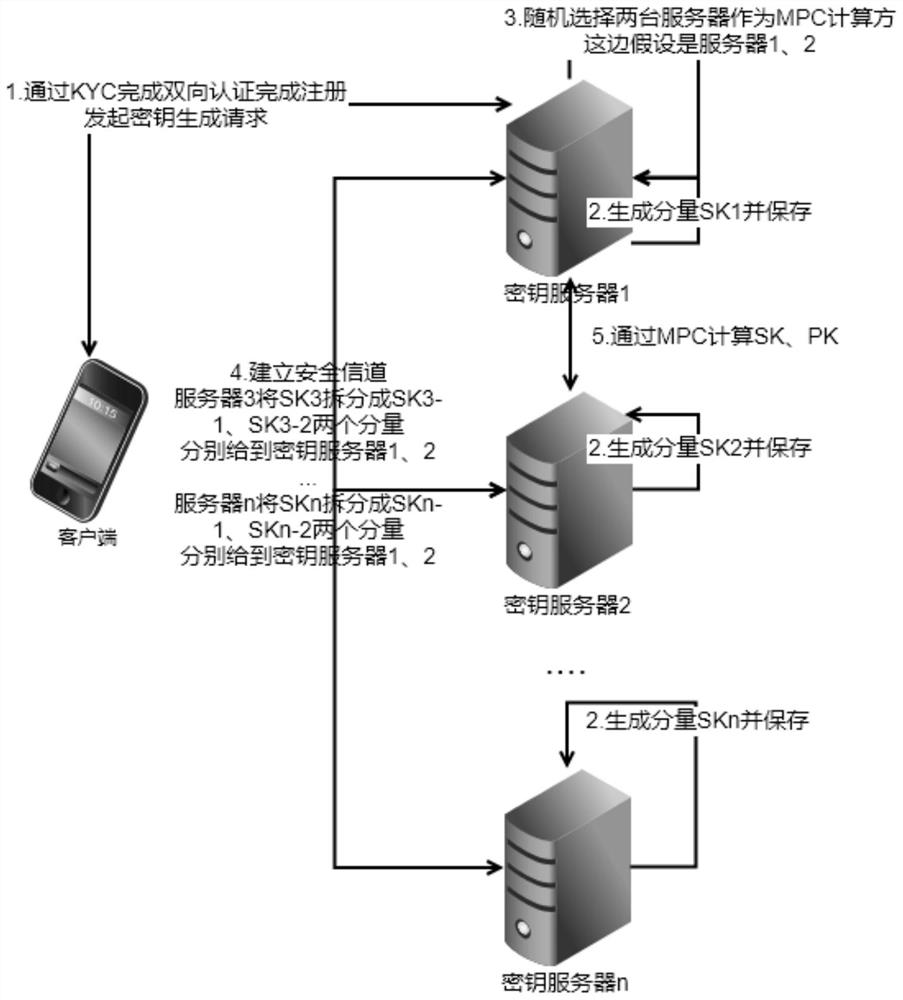
[0131] 1) generate:
[0132] Such as image 3 As shown, the following steps may be included:
[0133] S1: The client and the key server complete two-way authentication through KYC, and issue authentication materials to complete the registration process;
[0134] S2: Key servers 1~n generate key components SK1~n locally respectively;
[0135] S3: The ...
example 2
[0174] In this example, a key management method based on secure multi-party computing that is generated and stored by multiple servers is provided, a key management scheme based on secure multi-party computing is applied to the key generation and use of the key management system , storage, backup, restore, refresh and other operations.
[0175] Specifically, without client participation, multiple servers respectively generate private key components to obtain public keys through MPC, through MPC, multiple servers calculate signatures, and perform MPC calculations through private key components to refresh multiple server components. Operations such as key generation, use, storage, backup, recovery, and refresh in this situation are explained as follows:
[0176] 1) generate
[0177] Such as Figure 8 As shown, the following steps may be included:
[0178] S1: The client and the key server complete two-way authentication through KYC, and issue authentication materials to compl...
example 3
[0211] In this example, a key management method based on secure multi-party computing is provided that is generated and kept by multiple servers and one client, a key management scheme based on secure multi-party computing, and the key used in the key management system Create, use, store, backup, restore, refresh, etc.
[0212] Specifically, one client and multiple servers respectively generate private key components to obtain the public key through MPC, use the client and multiple servers to calculate signatures through MPC, and perform MPC calculations to refresh the client and multiple services through the private key components end weight. Operations such as key generation, use, storage, backup, recovery, and refresh in this situation are explained as follows:
[0213] 1) generate:
[0214] Such as Figure 13 As shown, the following steps may be included:
[0215] S1: The client and the key server complete two-way authentication through KYC, and issue authentication ma...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com