A Method of Constructing Stealth Network
A network and network entropy technology, applied in the Internet field, can solve problems such as inability to resist security threats, achieve high resistance to detection and attack, and improve security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
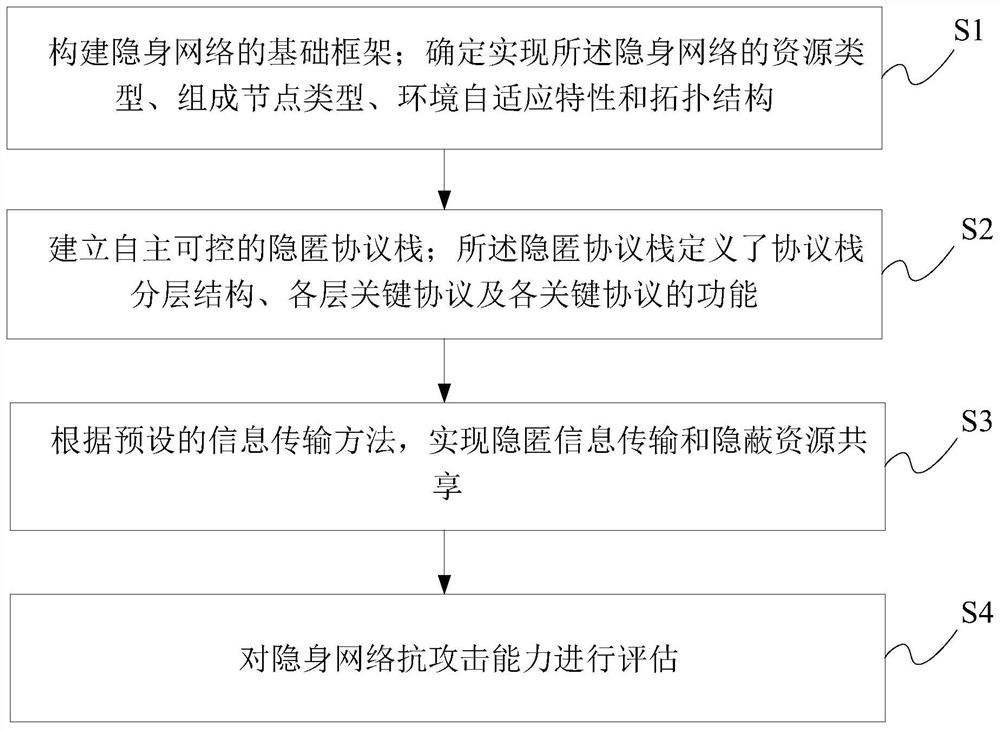
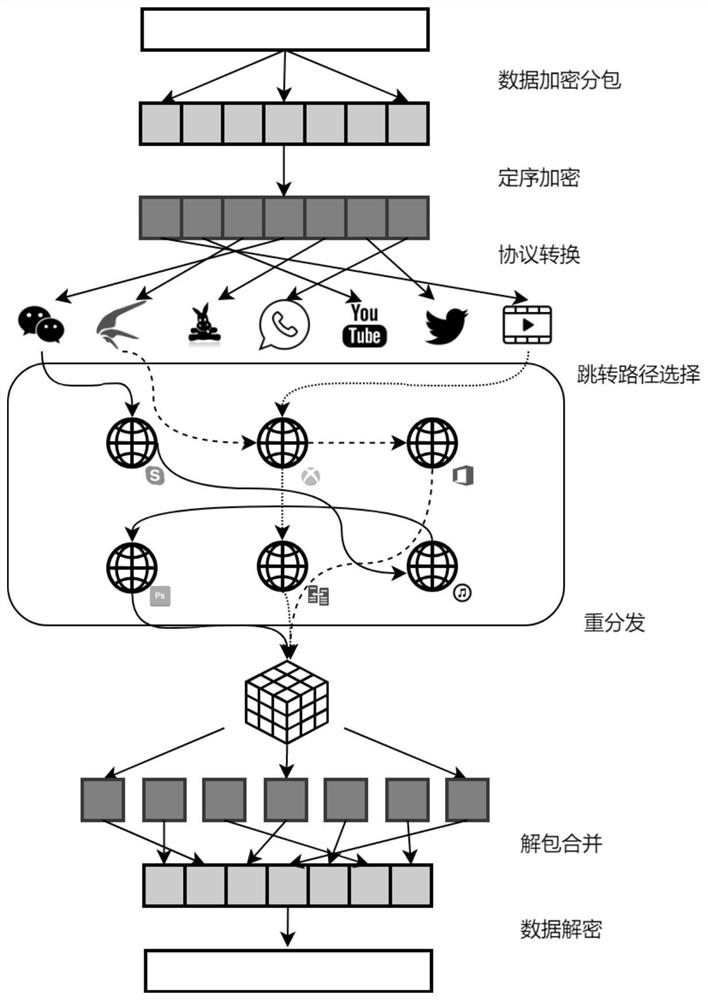
Method used
Image
Examples
Embodiment Construction
[0050] Exemplary embodiments of the present disclosure will be described in more detail below with reference to the accompanying drawings. Although exemplary embodiments of the present disclosure are shown in the drawings, it should be understood that the present disclosure may be embodied in various forms and should not be limited by the embodiments set forth herein. Rather, these embodiments are provided for more thorough understanding of the present disclosure and to fully convey the scope of the present disclosure to those skilled in the art.
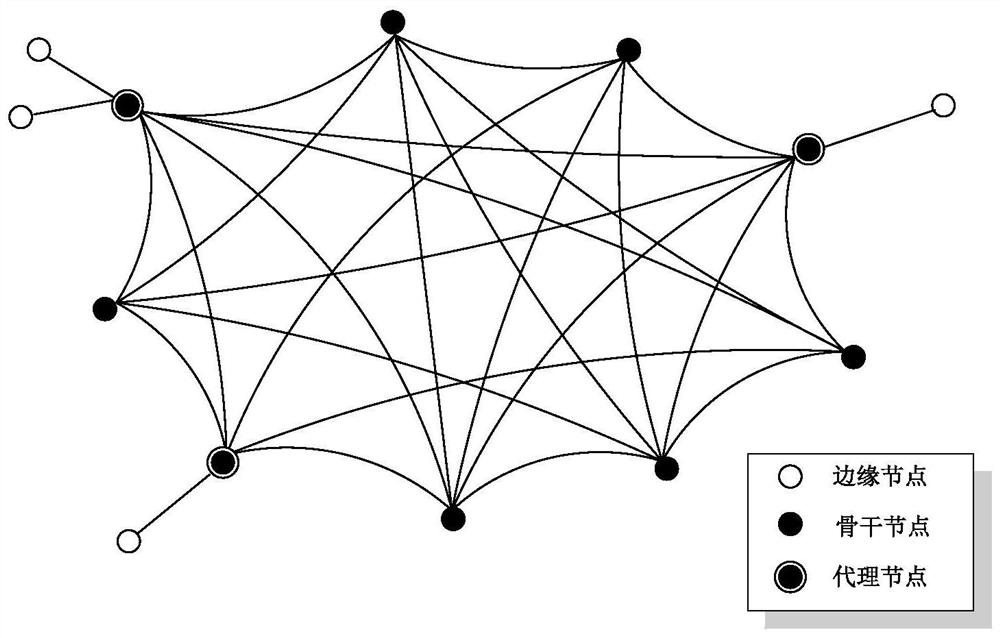
[0051] The network stealth claimed in the present invention refers to the realization of basic network services centered on hidden data communication and hidden resource sharing in the form of hidden channels, hidden information, hidden information sources and hidden information sinks. Hiding means that the exact information (including status, content, orientation, etc.) of an object (such as channel, information, source and destina...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More