Identity authentication login method in cloud environment
An identity authentication and login method technology, applied in the field of identity authentication and login, can solve the problems of easy identity fraud, difficult dynamic security boundary protection, easy to suffer from man-in-the-middle attacks, etc., and achieve the effect of improving security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
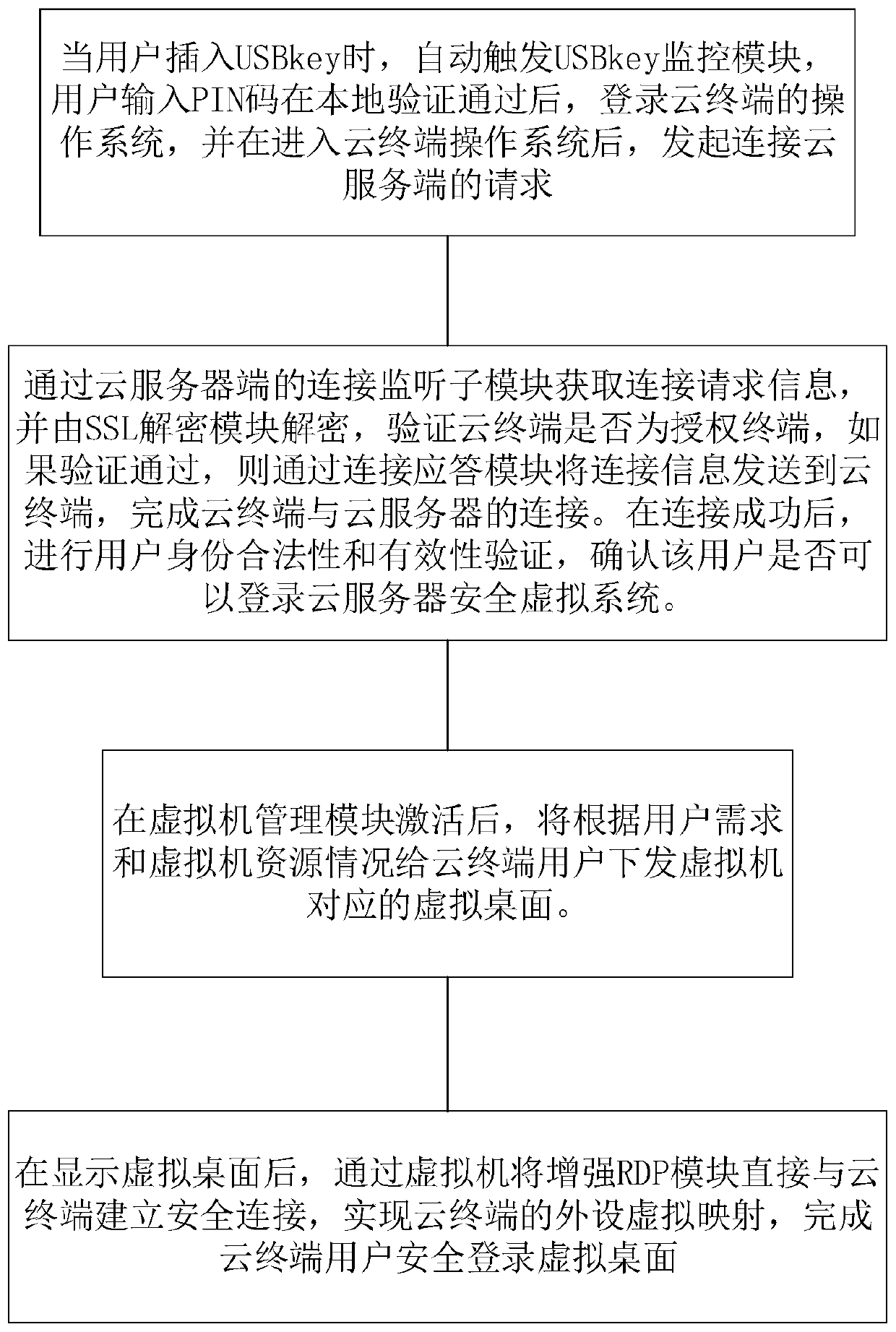
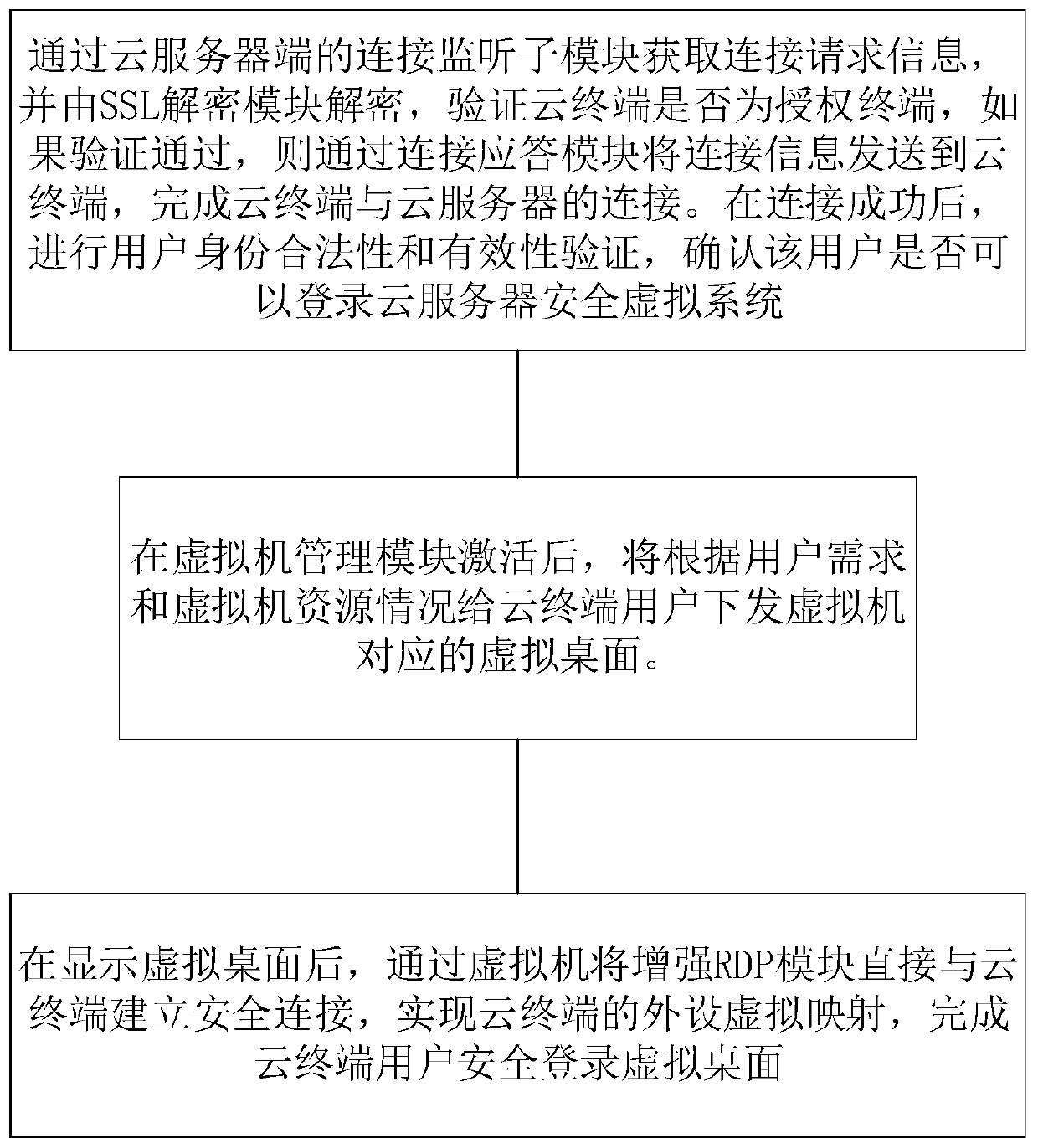
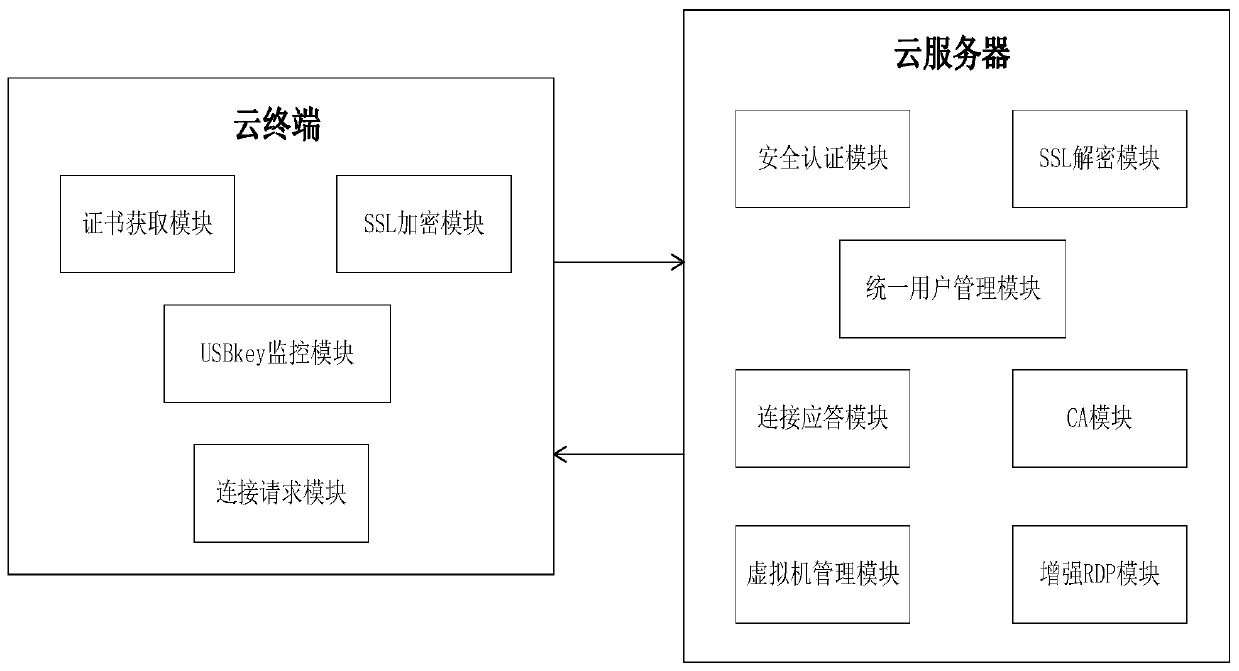
Method used
Image
Examples
Embodiment Construction
[0043] Examples of the present disclosure will now be described more fully with reference to the accompanying drawings. The following description is merely exemplary in nature and is not intended to limit the disclosure, application or uses.
[0044] Example embodiments are provided so that this disclosure will be thorough, and will fully convey the scope to those who are skilled in the art. Numerous specific details are set forth such as examples of specific components, devices and methods, to provide a thorough understanding of embodiments of the present disclosure. To those skilled in the art, specific details need not be employed, example embodiments may be embodied in many different forms, and neither should be construed to limit the scope of the disclosure. In some example embodiments, well-known processes, well-known structures, and well-known technologies are not described in detail.
[0045] The technical problems raised by the present disclosure will be described i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More