Threat alarm generation method and device based on systematic attacks
A system and data technology, applied in the field of network security, can solve problems such as unproposed solutions, and achieve the effect of reducing repeated alarms and reducing the amount of alarms
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
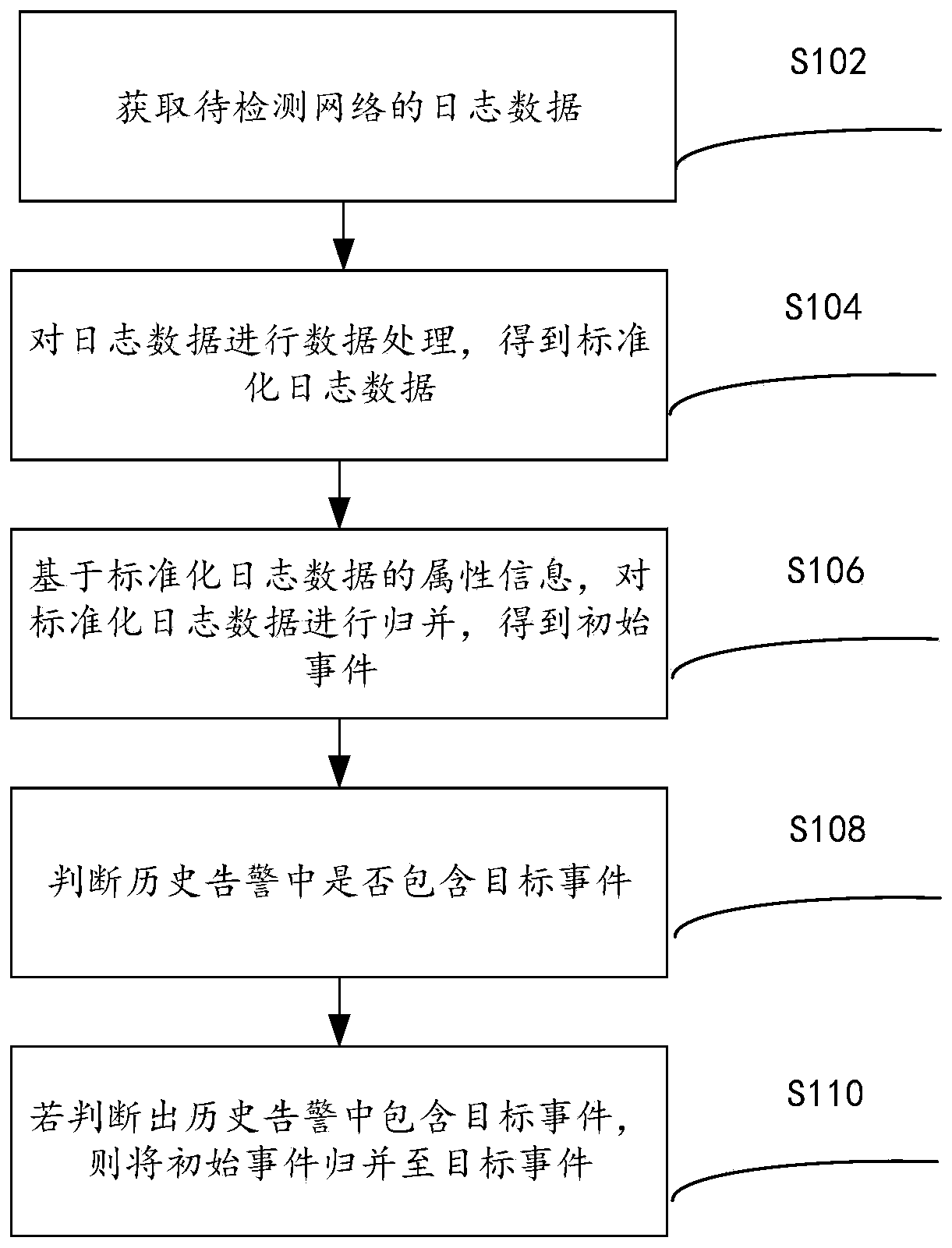
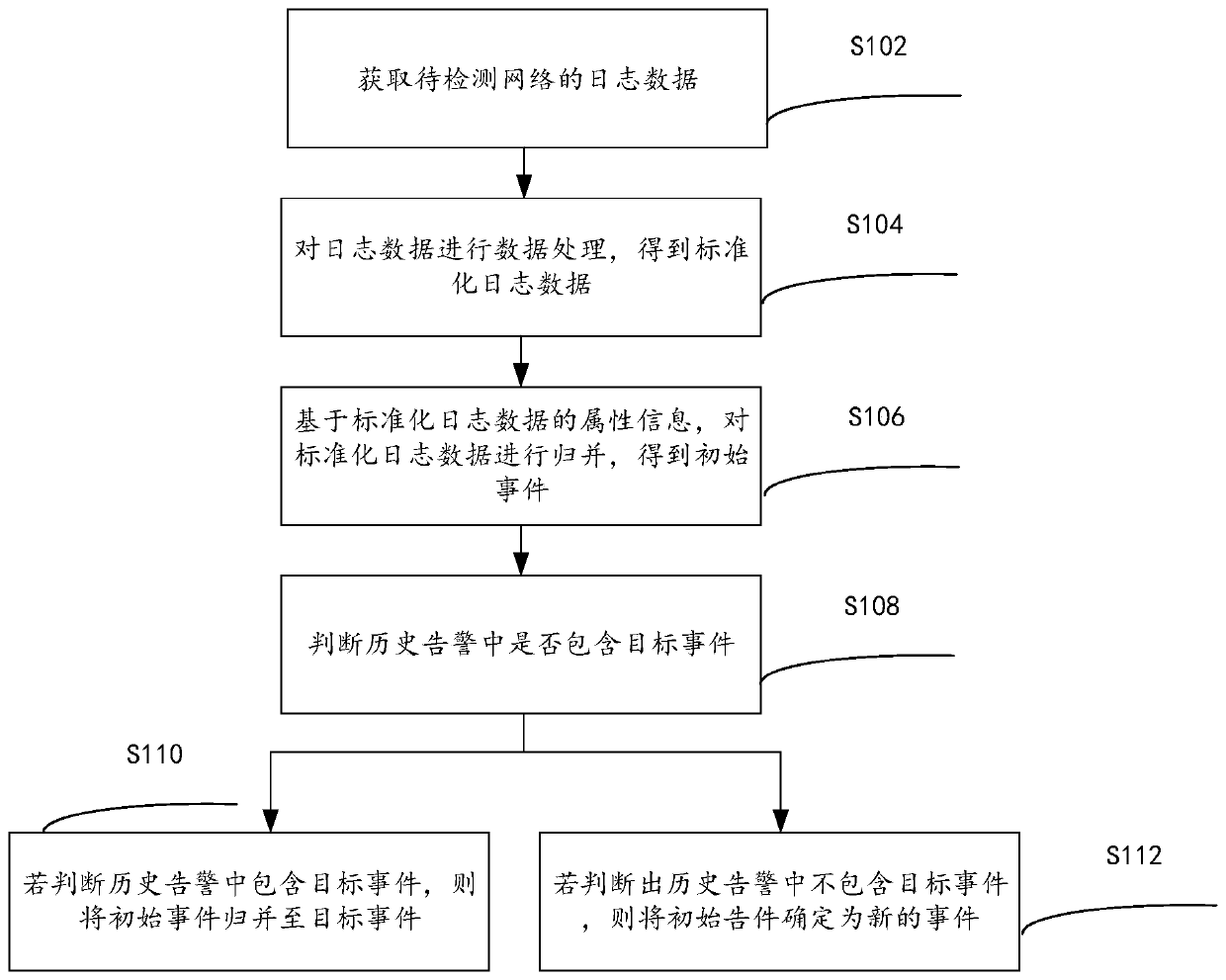
[0036] According to an embodiment of the present invention, an embodiment of a method for generating a threat warning based on a systematic attack is provided. It should be noted that the steps shown in the flow chart of the accompanying drawings can be implemented in a computer system such as a set of computer-executable instructions and, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
[0037] figure 1 is a flow chart of a method for generating a threat warning based on a systematic attack according to an embodiment of the present invention, such as figure 1 As shown, the method includes the following steps:
[0038] Step S102, acquiring log data of the network to be detected, wherein the log data is used to characterize the attack behavior of the network to be detected, and the log data includes at least one of the following: detection log data of secur...
Embodiment 2
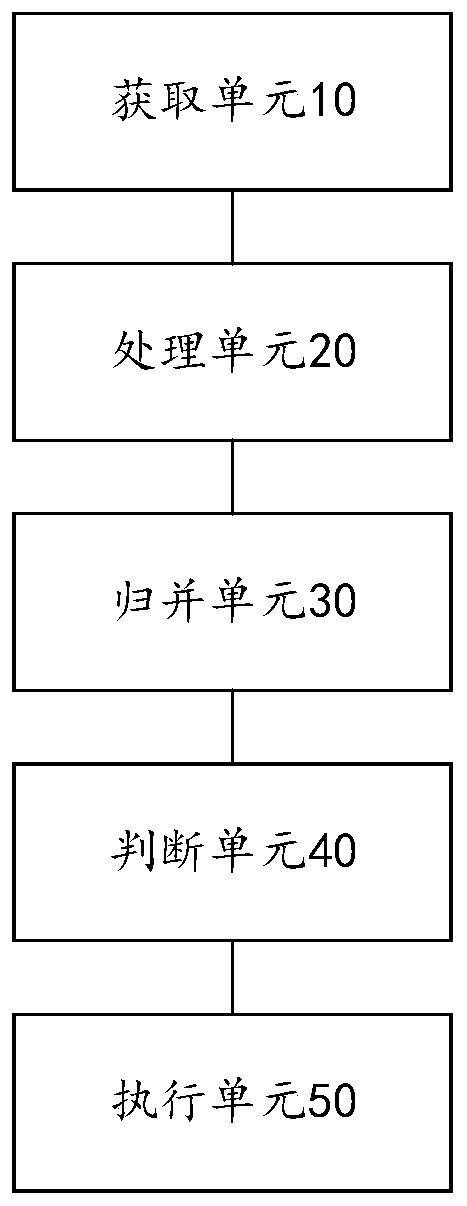
[0067] The present invention also provides a threat warning generation device based on a systematic attack, which is used to execute the method for generating a threat warning based on a systematic attack provided by the above-mentioned content of the embodiment of the present invention. A detailed introduction to the threat alarm generation device for systematic attacks.
[0068] Such as image 3 As shown, the above-mentioned threat warning generation device based on systematic attack includes: an acquisition unit 10 , a processing unit 20 , a merging unit 30 , a judging unit 40 and an execution unit 50 .
[0069] The acquiring unit 10 is configured to acquire log data of the network to be detected, wherein the log data is used to characterize the attack behavior of the network to be detected, and the log data includes at least one of the following: Detection log data, performance log data, fault log data, EDR log data, NDR log data;
[0070] The processing unit 20 is confi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com