Device authentication method, device access method and device
A device authentication and device technology, applied in the field of communications, can solve the problem of inability to add user identity authentication information
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
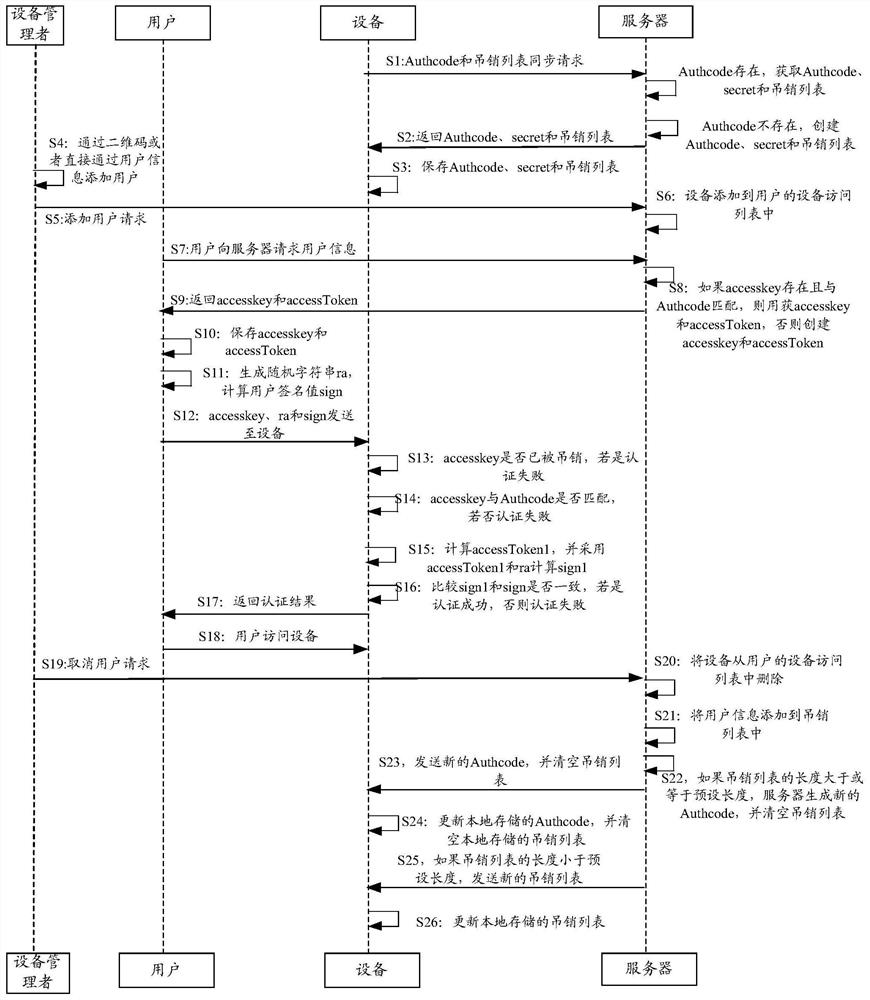
[0142] In order to make the above objects, features and advantages of the present application more obvious and comprehensible, the present application will be further described in detail below in conjunction with the accompanying drawings and specific implementation methods.
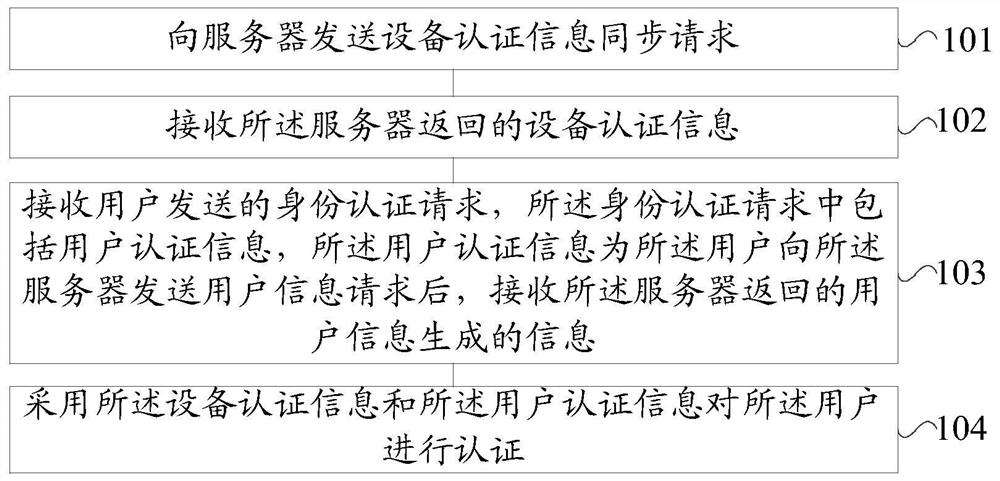
[0143] refer to figure 1 , shows a flow chart of the steps of Embodiment 1 of a device authentication method of the present application. The device authentication method of the embodiment of the present application can be applied to the device end, and may specifically include the following steps:
[0144] Step 101, sending a device authentication information synchronization request to a server.
[0145] In this embodiment of the application, the device may be an Internet of Things device, and the Internet of Things device may include a sensor device, such as a radio frequency identification device, an infrared sensor, an environmental sensor, a global positioning system, a PDA handheld terminal, an RFID...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More