Encryption method of call handling strategy
A strategy and consistent technology, applied in the information field, can solve problems such as the suspicious fraud list number list on the call control side, so as to prevent leakage and ensure security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0012] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings.
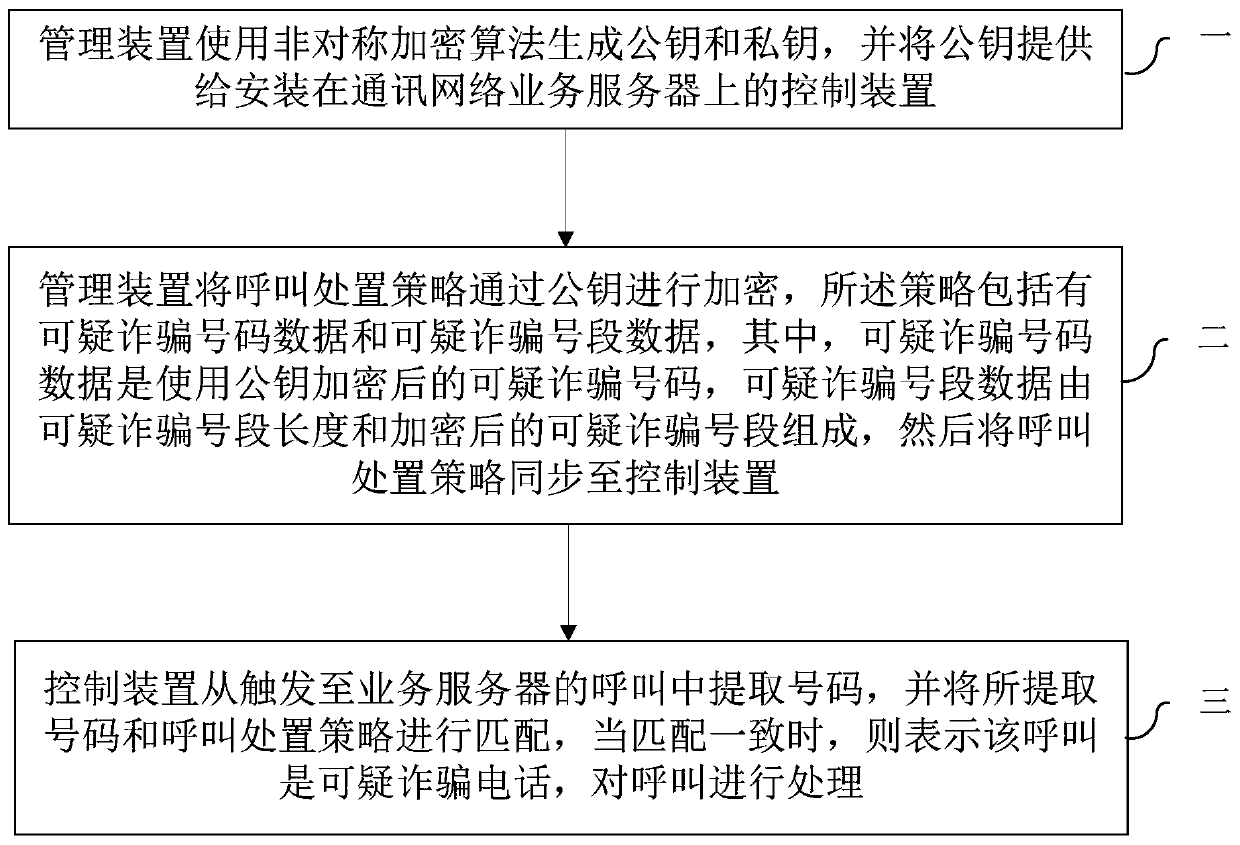
[0013] Such as figure 1 As shown, a method for encrypting call handling policy data of the present invention includes:
[0014] Step 1, the management device uses an asymmetric encryption algorithm to generate a public key and a private key, and provides the public key to the control device installed on the communication network service server;
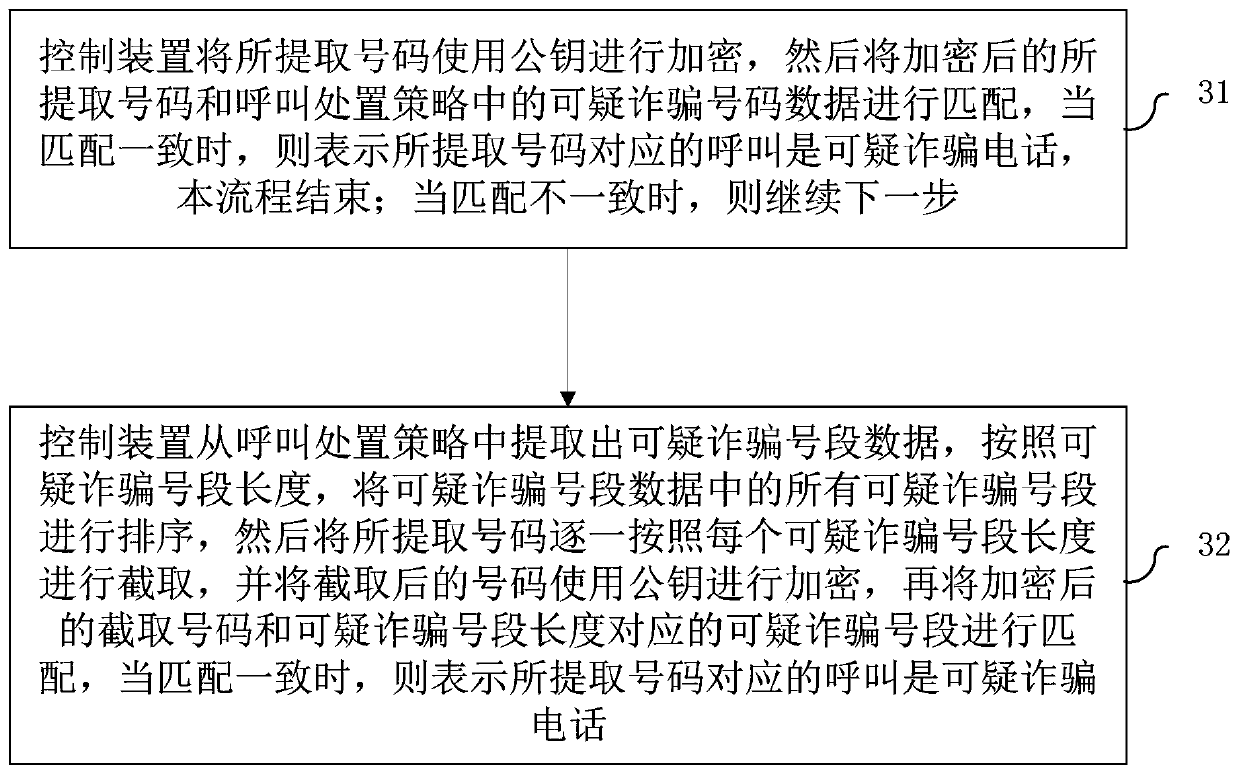
[0015] Step 2: The management device encrypts the call handling strategy with a public key, and the strategy includes suspicious fraudulent number data and suspicious fraudulent number segment data, wherein the suspicious fraudulent number data is a suspicious fraudulent number encrypted with a public key, and the suspicious fraudulent The number segment data is composed of the length of the suspected fraudulent number s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More