Executive scheduling method for mimicry structure Web server
A scheduling method and executive technology, applied in reasoning methods, instruments, probabilistic networks, etc., can solve problems such as vulnerability attack security and adverse effects, improve defense capabilities and service quality, increase attack costs, and delay the attack. The effect of attack time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] The present invention will be further described in detail below in conjunction with the accompanying drawings, so that those skilled in the art can implement it with reference to the description.
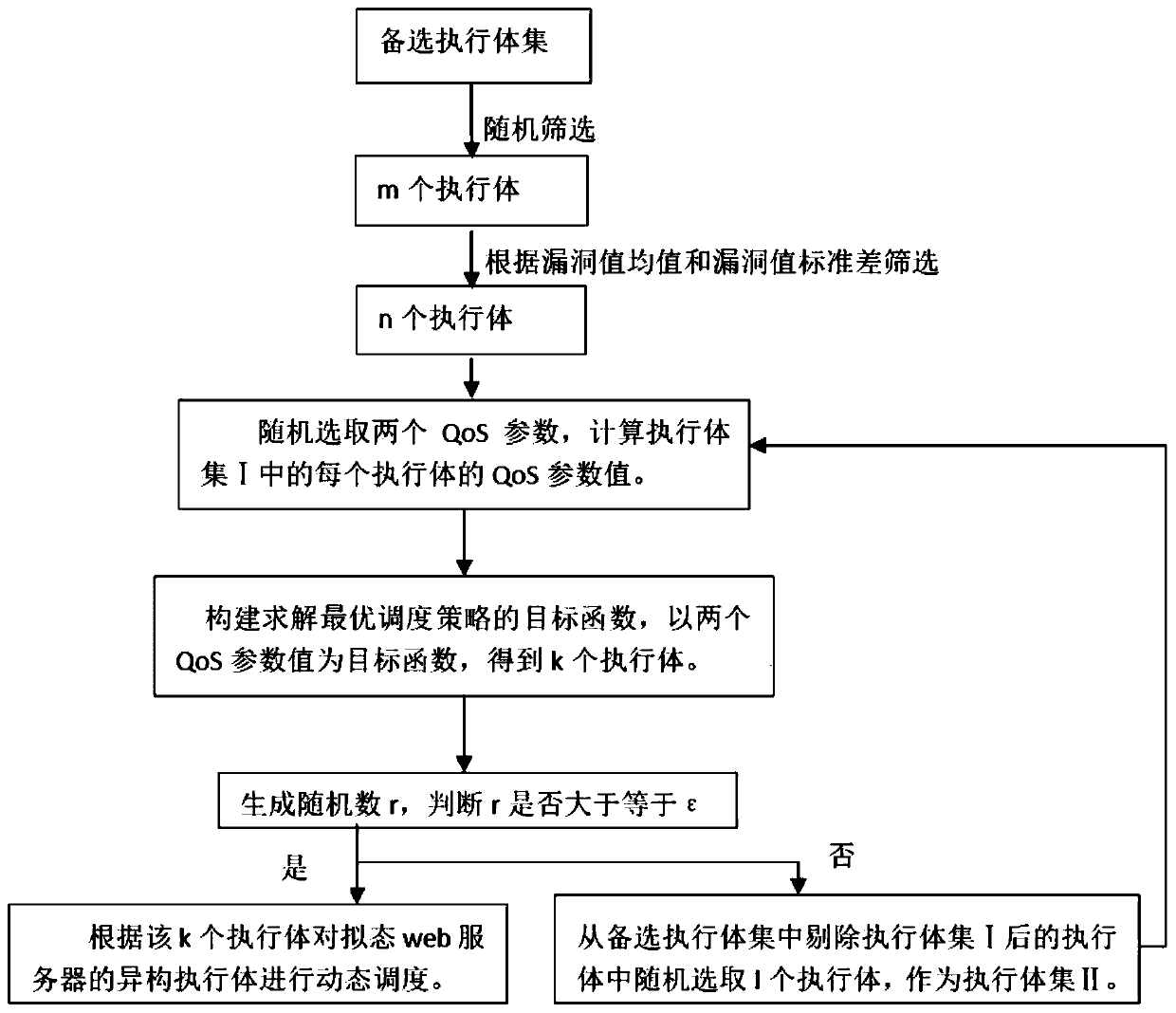
[0029] Such as figure 1 As shown, the present invention provides a kind of execution body dispatching method oriented to mimetic structure Web server, comprising:
[0030] Step 1: Generate a set of candidate executables, randomly select m executables from the set of candidate executables, calculate the mean value of the vulnerability value and the standard deviation of the vulnerability value of each layer of the software stack of each of the m executables, from Among the m execution bodies, select n execution bodies with the average value of the vulnerability value and the standard deviation of the vulnerability value within the range of the threshold value of the vulnerability value, as the execution body set I, where m and n are both integers greater than 0; alternative ex...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More