Out-of-authority vulnerability detection method, apparatus and device, and storage medium
A detection method and vulnerability technology, applied in the computer field, can solve problems such as the inability to accurately judge unauthorized loopholes, and achieve the effect of reducing human resource investment and improving accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] In order to make the purpose, technical solution and advantages of the present application clearer, the implementation manners of the present application will be further described in detail below in conjunction with the accompanying drawings.
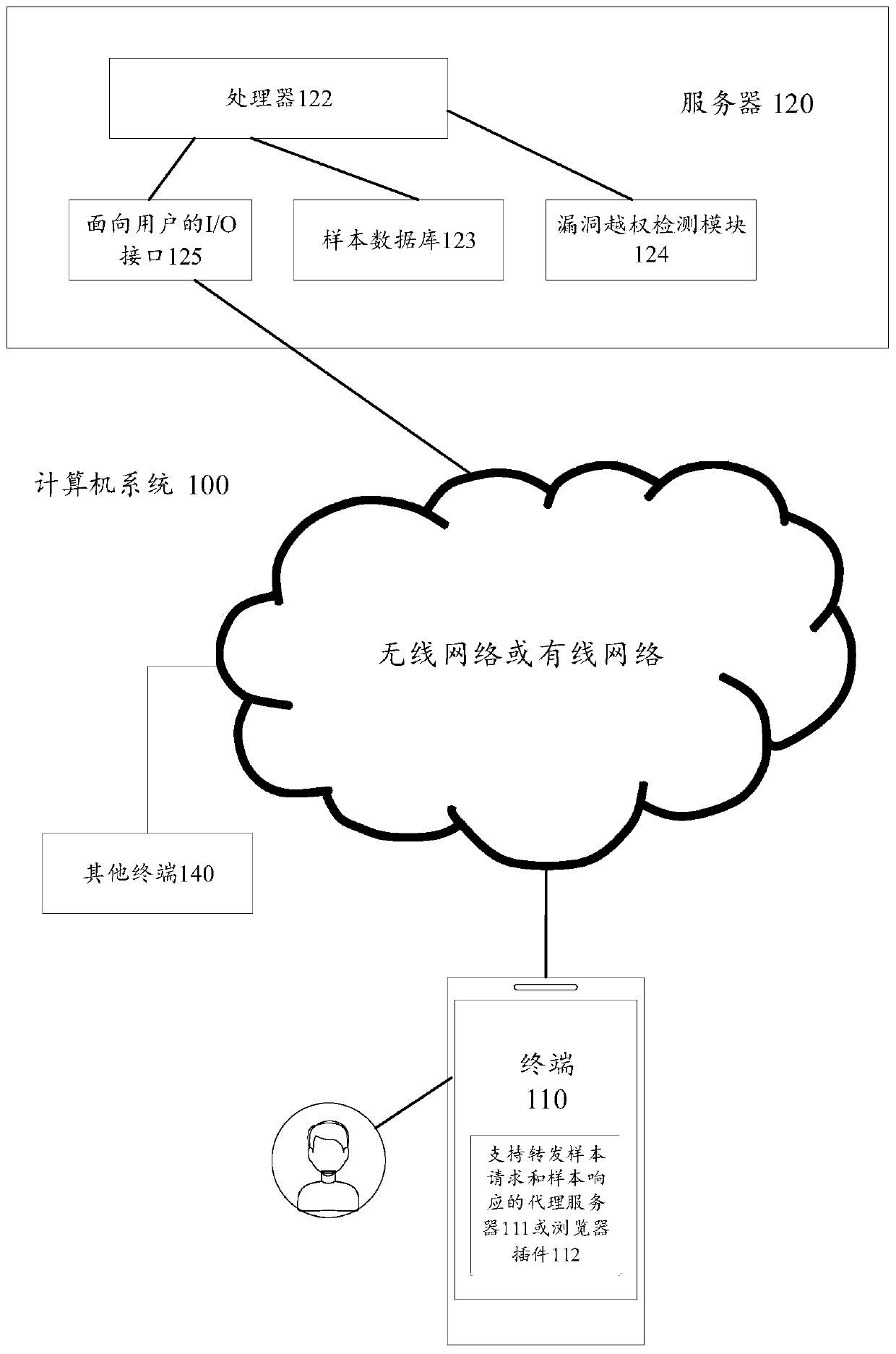
[0033] figure 1 A structural block diagram of a computer system provided by an exemplary embodiment of the present application is shown. The computer system 100 includes: a terminal 110 and a server 120 .
[0034] The terminal 110 installs and runs a proxy server 111 or a browser plug-in 112 that supports forwarding sample requests and sample responses. The proxy server 111 or browser plug-in 112 has the function of collecting requests and responses between the terminal and the server. The device type of the terminal includes: at least one of a smart phone, a tablet computer, an e-book reader, an MP3 player, an MP4 player, a laptop computer, and a desktop computer. figure 1 Only one terminal is shown in , but there are multiple...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com