Business access control method and system, electronic equipment and storage medium
A technology of business access and control methods, applied in the computer field
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
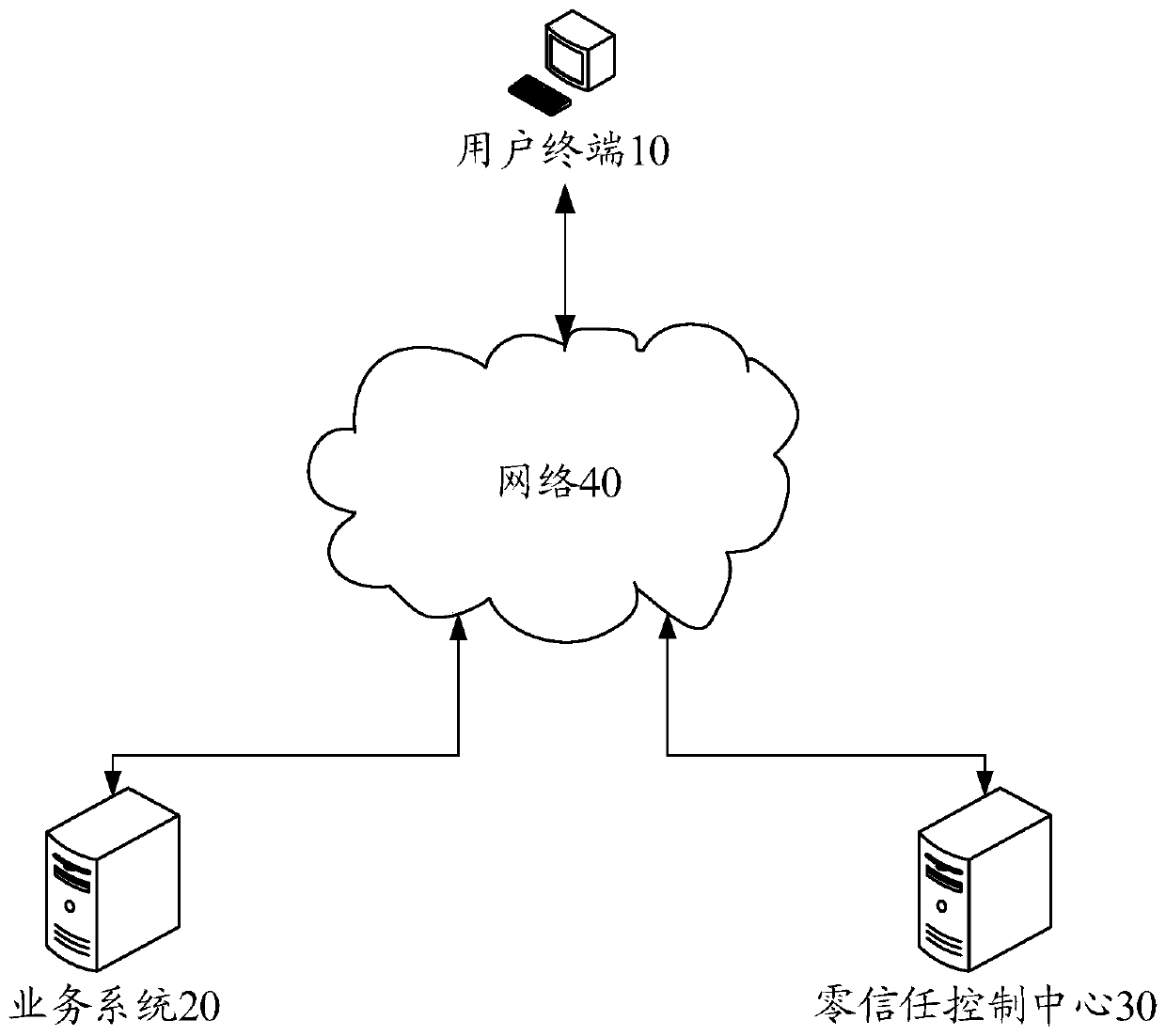
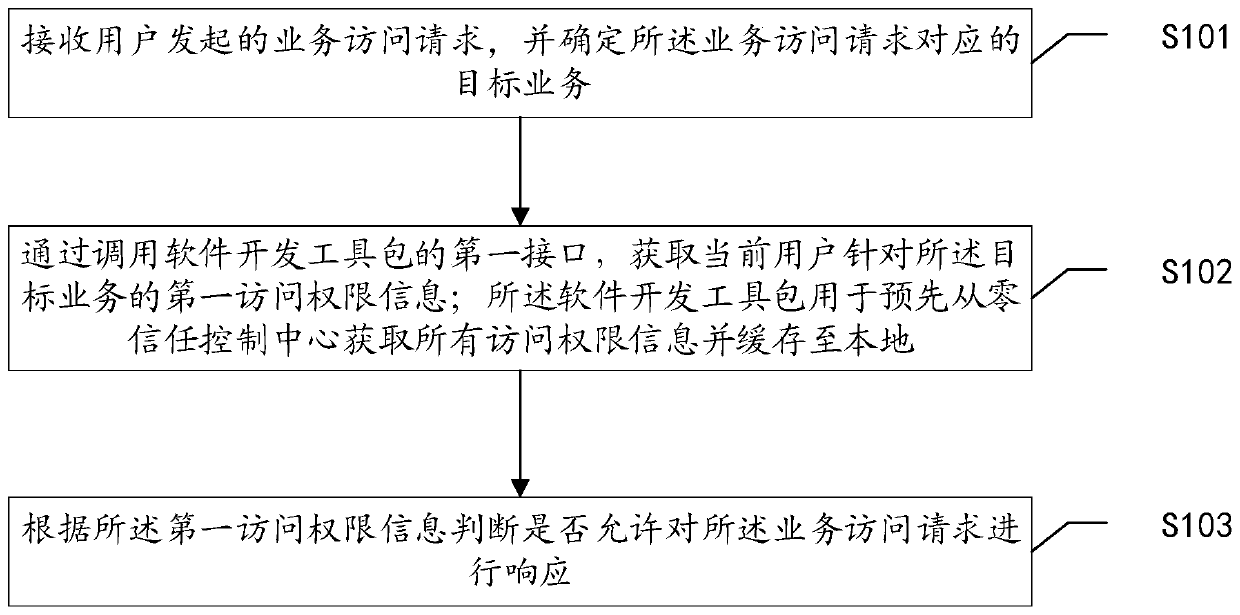
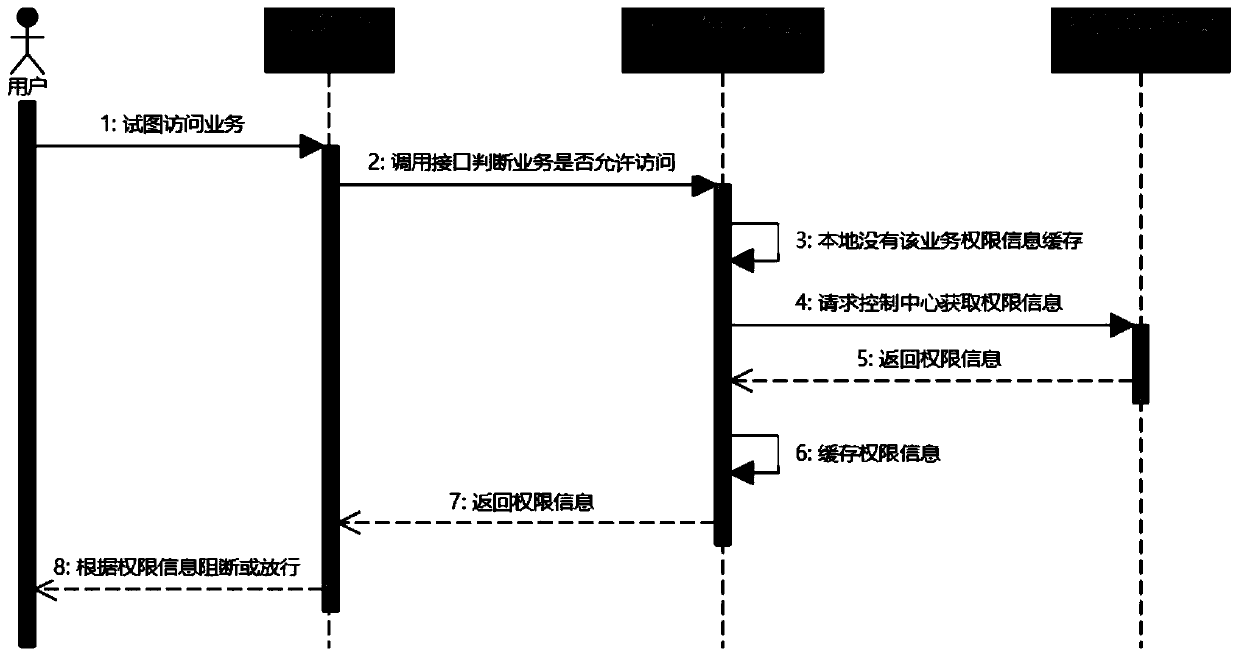
[0050] The following will clearly and completely describe the technical solutions in the embodiments of the application with reference to the drawings in the embodiments of the application. Apparently, the described embodiments are only some of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0051] In the existing technology, access control is usually based on the application, that is, according to the characteristics of the business system, such as web applications or tunnel applications, different applications are added to the zero trust system control center, and the control center evaluates the user's trust level and communicates with the network The proxy server interacts to block or allow specified application access requests. However, in this way, it is difficult...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More