Security threat detection method and device, computer equipment and storage medium
A detection method and computer program technology, applied in the field of data processing, can solve problems such as high false positive rate, missing security threats, affecting user experience, etc., and achieve the effect of improving security performance and detection ability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
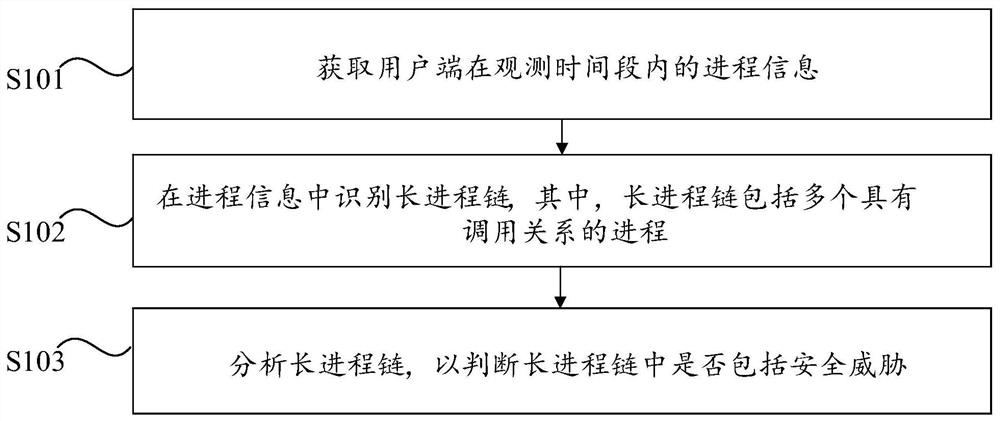
[0029] An embodiment of the present invention provides a security threat detection method, through which the security threat detection capability can be improved, specifically, figure 1 It is a flow chart of the security threat detection method provided in Embodiment 1 of the present invention, such as figure 1 As shown, the security threat detection method provided by this embodiment includes the following steps S101 to S103.
[0030] Step S101: Obtain process information of the client within the observation time period.
[0031] Wherein, the process information includes the processes running on the client terminal during the observation time period and the calling relationship between the processes.
[0032] Specifically, the client includes terminals such as personal computers, mobile phones, and handheld computers, as well as servers or intermediate network devices; the observation time period is a detection time window set according to actual needs, for example, the obse...
Embodiment 2
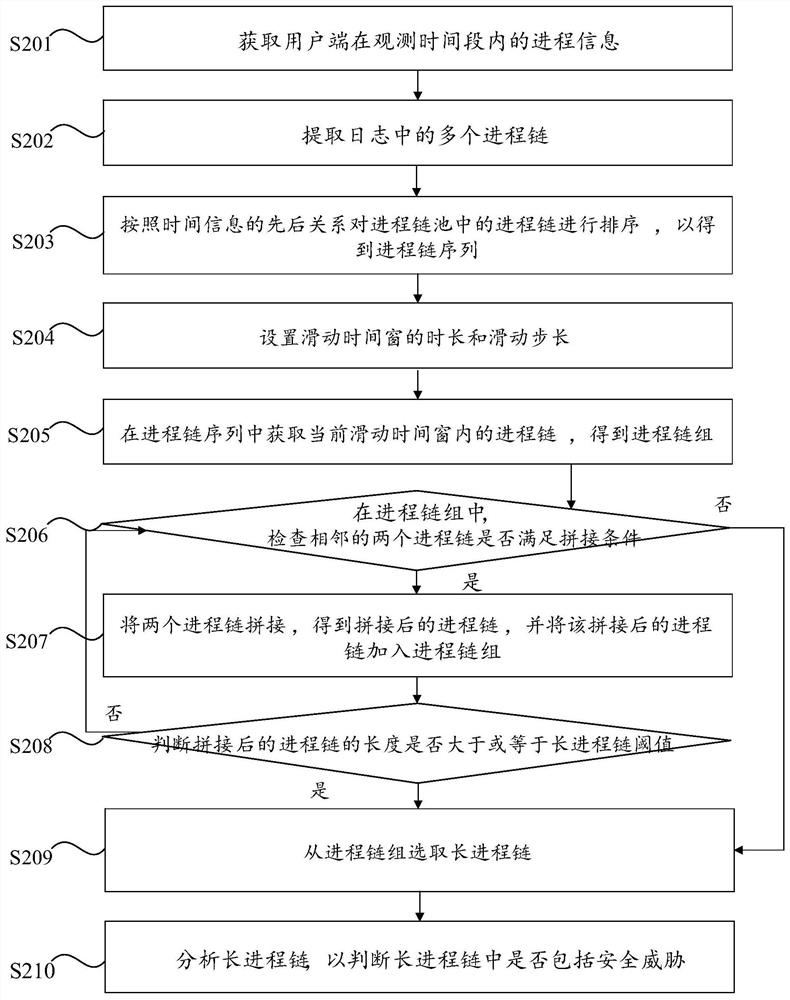
[0054] Embodiment 2 of the present invention provides a method for preferably detecting security threats. For some technical features and corresponding technical effects, reference may be made to the relevant description of Embodiment 1 above, and details will not be repeated in this embodiment. specifically, figure 2 It is a flow chart of the security threat detection method provided by Embodiment 2 of the present invention, such as figure 2 As shown, the security threat detection method provided by the second embodiment includes the following steps S201 to S210.
[0055] Step S201: Obtain process information of the client within the observation time period.
[0056] Wherein, the process information includes the processes running on the client terminal during the observation time period and the calling relationship between the processes.
[0057] Step S202: Extract multiple process chains in the log.
[0058] Wherein, the process chain includes at least two processes hav...
Embodiment 3
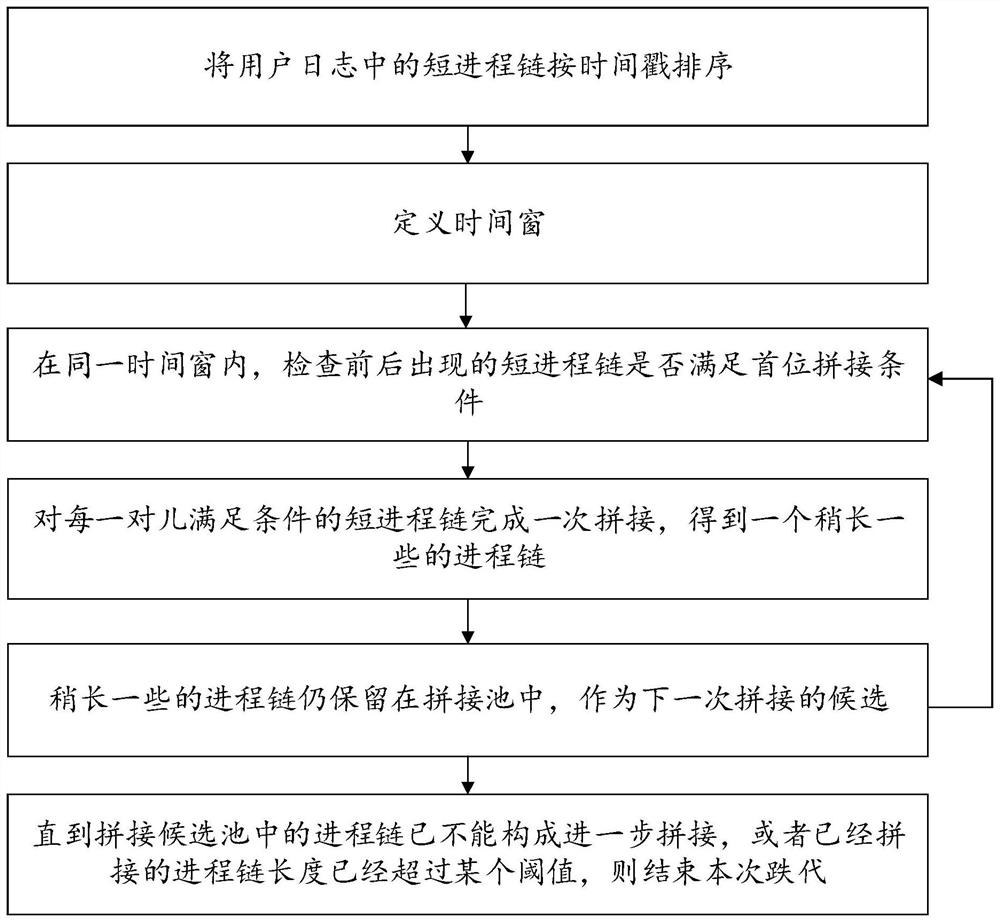
[0079] Embodiment 3 of the present invention provides a method for preferably detecting security threats. For some technical features and corresponding technical effects, reference may be made to the relevant descriptions of Embodiment 1 and Embodiment 2 above, and details will not be repeated in this embodiment. Specifically, in the security threat detection method provided in this embodiment, to restore the long process chain based on the user's cloud killing log, first sort the parent-child process short chains appearing in the user log by timestamp, and then set the sliding The time window (the length of the time window adopted in this embodiment is 5 seconds) processes each user's parent-child process chain log. In the same time window, if the front and rear short process chains meet the splicing conditions, a splicing is completed. The specific splicing conditions include: 1) the last process of the previous process chain is the same as the first process of the latter pr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More