Encryption and decryption method and device based on Ubifs system and medium
An encryption method and system-oriented technology, applied in the fields of encryption, equipment and media, and decryption methods based on Ubifs system, can solve problems such as damage to user interests, damage to user experience, and impact on the interests of system package manufacturers, and achieve a balance between encryption and performance , to protect the security of the machine, without affecting the effect of reading and writing performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
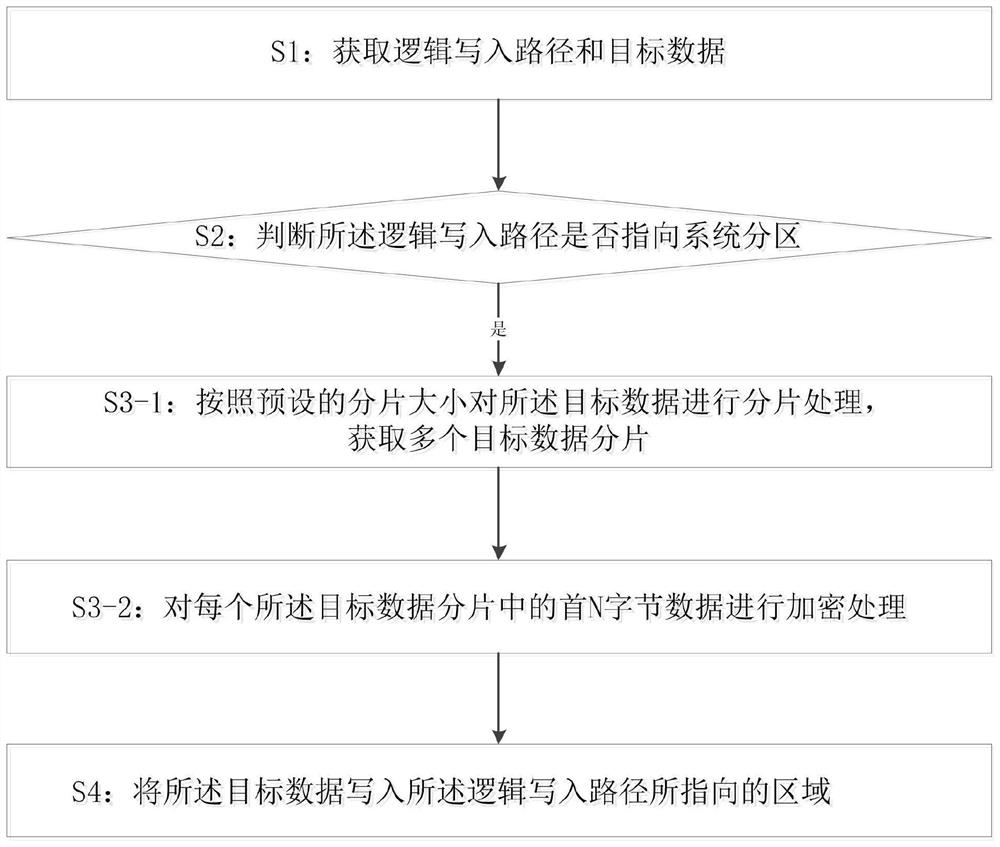
[0066]Such asfigure 1 ,5As shown, this embodiment provides an encryption method based on the Ubifs system, including:
[0067]S1: Obtain the logical write path and pre-written data;
[0068]S2: Determine whether the logical write path points to the system partition, if so, enter S3-1;
[0069]S3-1: Fragment processing is performed on the pre-written data according to the preset fragment size to obtain multiple written data fragments;
[0070]S3-2: Encrypt the specified N bytes of data in each written data segment;
[0071]S4: Write pre-written data into the area pointed to by the logical write path.
[0072]In this embodiment, when applied to the Ubifs system, the logical write path and pre-written data are first obtained, and then it is judged whether the area pointed to by the logical write path is a system partition. If it is not a system partition, no operation is performed. Just write, but if it is a system partition, you need to slice the target data first and divide it into slices. The size of...
Embodiment 2
[0075]Such asfigure 2 ,5As shown, this embodiment provides an encryption method based on the Ubifs system, including:
[0076]S1: Obtain the logical write path and pre-written data;
[0077]S2: Determine whether the logical write path points to the system partition, if so, enter S3;
[0078]S3-1: Perform fragment processing on the pre-written data according to the preset fragment size to obtain multiple written data fragments; specify N bytes of data as the first N bytes of data in each write data fragment; The fragment size is 4KB; relatively speaking, the size of 4KB can achieve good security effects without affecting performance.
[0079]S3-2: Encrypt the specified N bytes of data in each write data segment; N is one of 16, 32, and 64;
[0080]S4-1: The disordered block mirroring management system layer initiates a data write request to the disordered block mirroring layer according to the logical write path;
[0081]S4-2: The disordered block mirroring layer converts the logical write path into t...
Embodiment 3
[0088]Such asFigure 5As shown, this embodiment provides an encryption method based on the Ubifs system, including:
[0089]S1: Obtain the logical write path and pre-written data; the logical write path points to the logical erase block;
[0090]S2: Determine whether the logical write path points to the system partition, if so, enter S3;
[0091]S3-1: Fragment processing is performed on the pre-written data according to the preset fragment size to obtain multiple written data fragments; the fragment size is 4KB;
[0092]S3-2: Encrypt the specified N bytes of data in each write data segment; N is one of 16, 32, and 64; specify N bytes of data for each write data segment The first N bytes of data;
[0093]S4-1: The disordered block mirroring management system layer initiates a data write request to the disordered block mirroring layer according to the logical write path;
[0094]S4-2: The disordered block mirror layer converts the logical write path into a physical write path according to the erase bloc...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More