Enterprise identity verification method and system, electronic equipment and storage medium
An identity verification method and storage medium technology, applied in the field of electronic equipment and storage media, systems, and enterprise identity verification methods, can solve low work efficiency, high cost, increase illegal use of data, hacker attacks, phishing and DDoS attack human errors And other issues
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
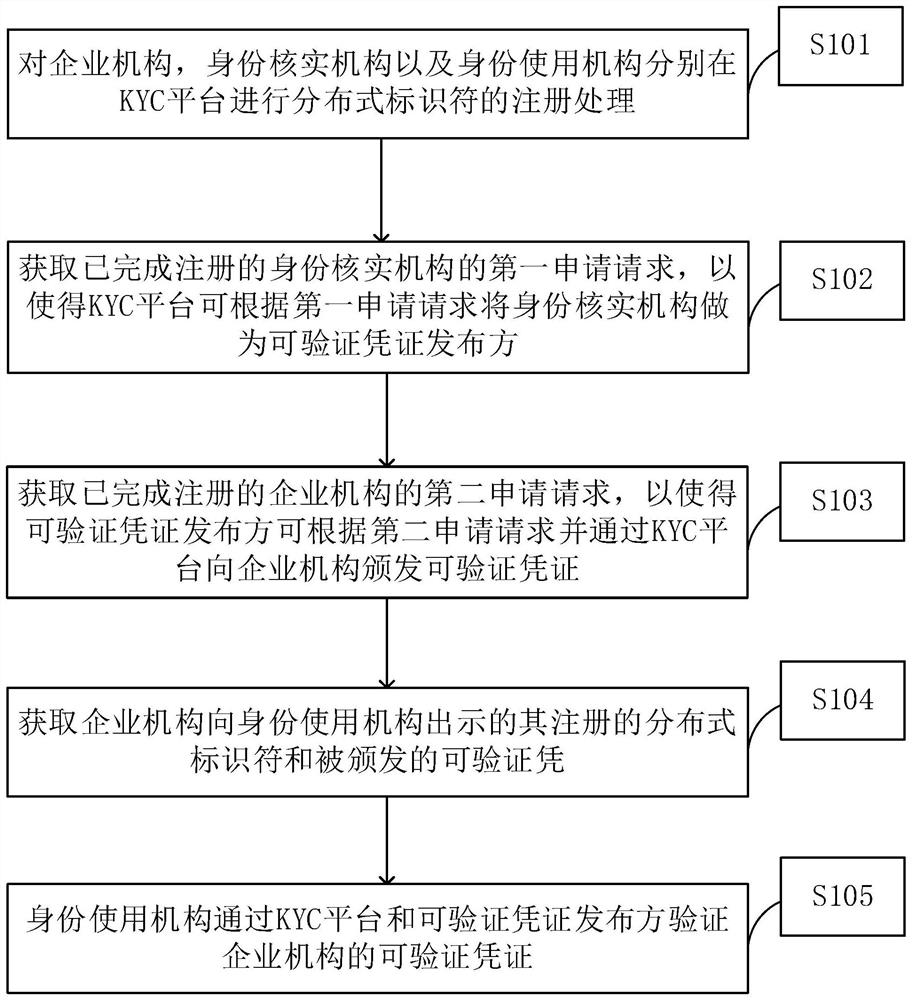
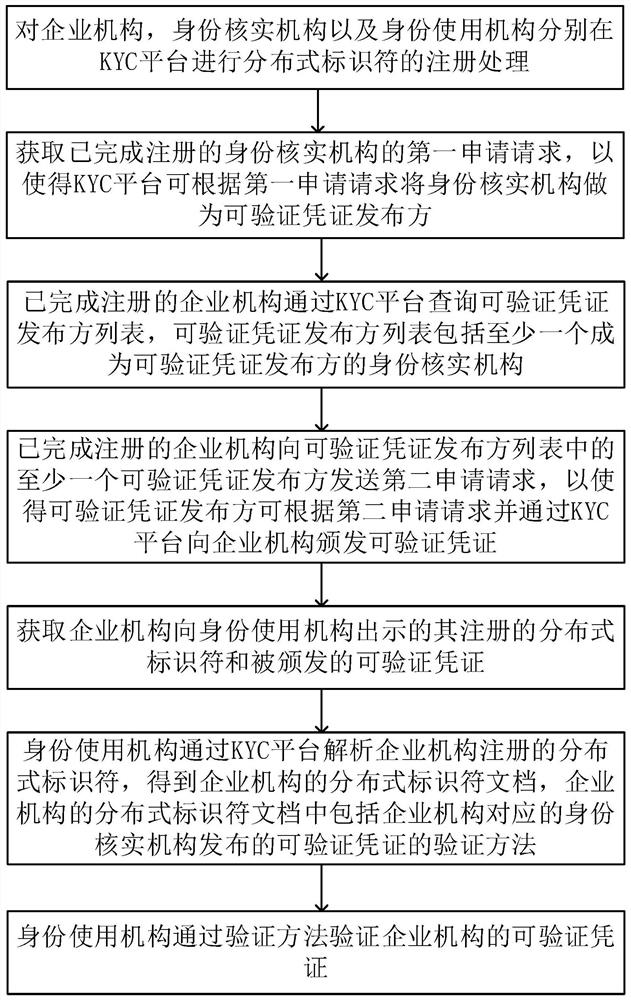
[0070] see figure 1 , the embodiment of this application provides an enterprise identity verification method, including:
[0071] S101: Register the distributed identifiers on the KYC platform for the enterprise organization, the identity verification organization and the identity use organization respectively;
[0072] Specifically, KYC (Know Your Customer) is mainly used in the financial field to verify the identity and suitability of customers in financial services, and to assess the risks of maintaining a business relationship with the customer. Businesses often go through KYC to ensure that their potential clients, agents, consultants, and publishers are compliant with anti-bribery regulations and that the information submitted is true to reality.
[0073] Enterprise organizations include companies that need to perform KYC in financial activities. Identity verification agencies are organizations that can issue KYC certificates, that is, organizations that issue verifiabl...
Embodiment 2
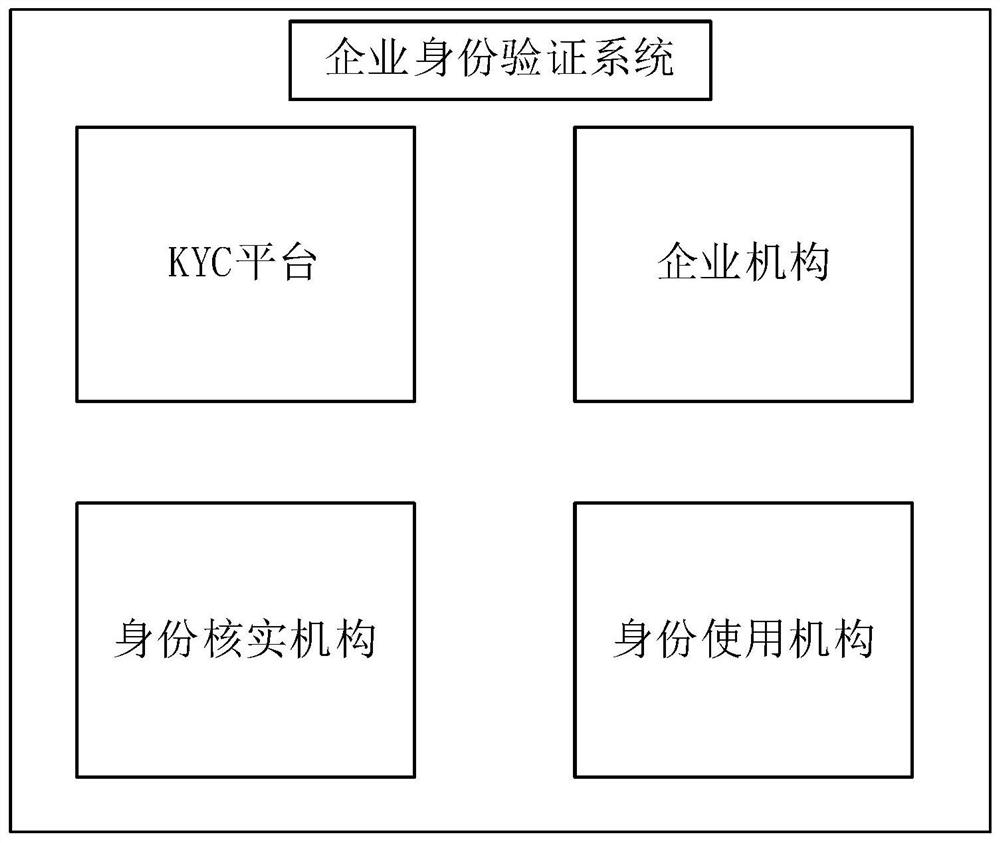
[0108] see image 3 , the embodiment of the present application provides an identity verification system, including: the KYC platform of any one of the first aspect, an enterprise institution, an identity verification institution and an identity use institution;
[0109] The KYC platform is used to register and process distributed identifiers on the KYC platform for corporate institutions, identity verification institutions and identity use institutions;
[0110] Specifically, KYC (Know Your Customer) is mainly used in the financial field to verify the identity and suitability of customers in financial services, and to assess the risks of maintaining a business relationship with the customer. Businesses often go through KYC to ensure that their potential clients, agents, consultants, and publishers are compliant with anti-bribery regulations and that the information submitted is true to reality.
[0111] Enterprise organizations include companies that need to perform KYC in f...
Embodiment 3
[0145] see Figure 4 , the embodiment of the present application provides an electronic device 30, including a memory 301 and a processor 302, an executable program is stored in the memory, and the processor performs the following steps when running the executable program:
[0146] Register and process distributed identifiers on the KYC platform for corporate institutions, identity verification institutions, and identity use institutions;
[0147] Specifically, KYC (Know Your Customer) is mainly used in the financial field to verify the identity and suitability of customers in financial services, and to assess the risks of maintaining a business relationship with the customer. Businesses often go through KYC to ensure that their potential clients, agents, consultants, and publishers are compliant with anti-bribery regulations and that the information submitted is true to reality.
[0148] Enterprise organizations include companies that need to perform KYC in financial activit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More