Memory isolation device, memory isolation method and related equipment
A memory isolation and memory technology, applied in the computer field, can solve problems such as high security risks, and achieve the effect of memory isolation and security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
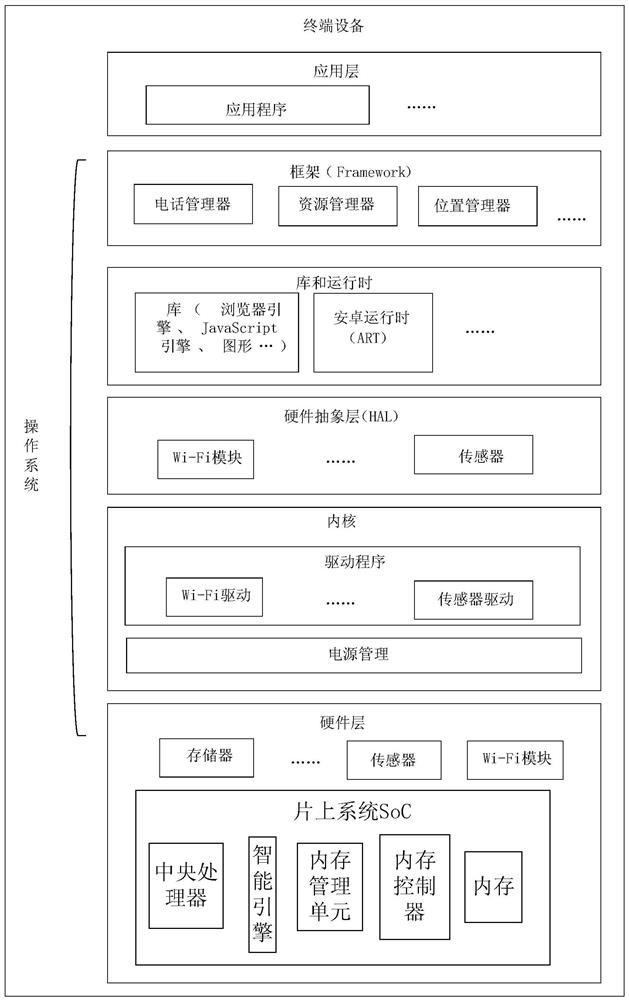
[0049] The embodiment of the present application provides a memory isolation device, a memory isolation method, and related equipment. By adding a memory scrambling unit, the memory scrambling unit and the trusted processor are independent of each other. The process identifier to scramble the data. To ensure the security of the written data. Hardware-level memory security isolation can be achieved. Since each application program corresponds to one or more processes, and each process corresponds to a unique process identifier, memory isolation between processes is realized.
[0050] Embodiments of the present application are described below in conjunction with the accompanying drawings. Those of ordinary skill in the art know that, with the development of technology and the emergence of new scenarios, the technical solutions provided in the embodiments of the present application are also applicable to similar technical problems.
[0051] The terms "first", "second" and the l...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More