ARP spoofing attack prevention method and system
A technology of ARP spoofing and ARP request, which is applied in the field of ARP spoofing attack defense methods and systems, and can solve problems such as threats to industrial infrastructure network construction network security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
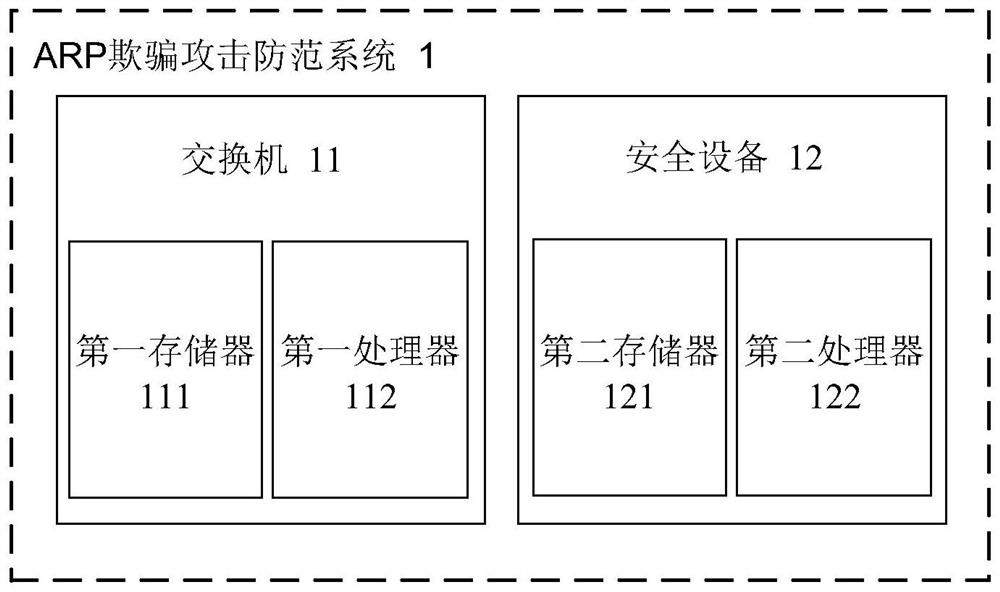
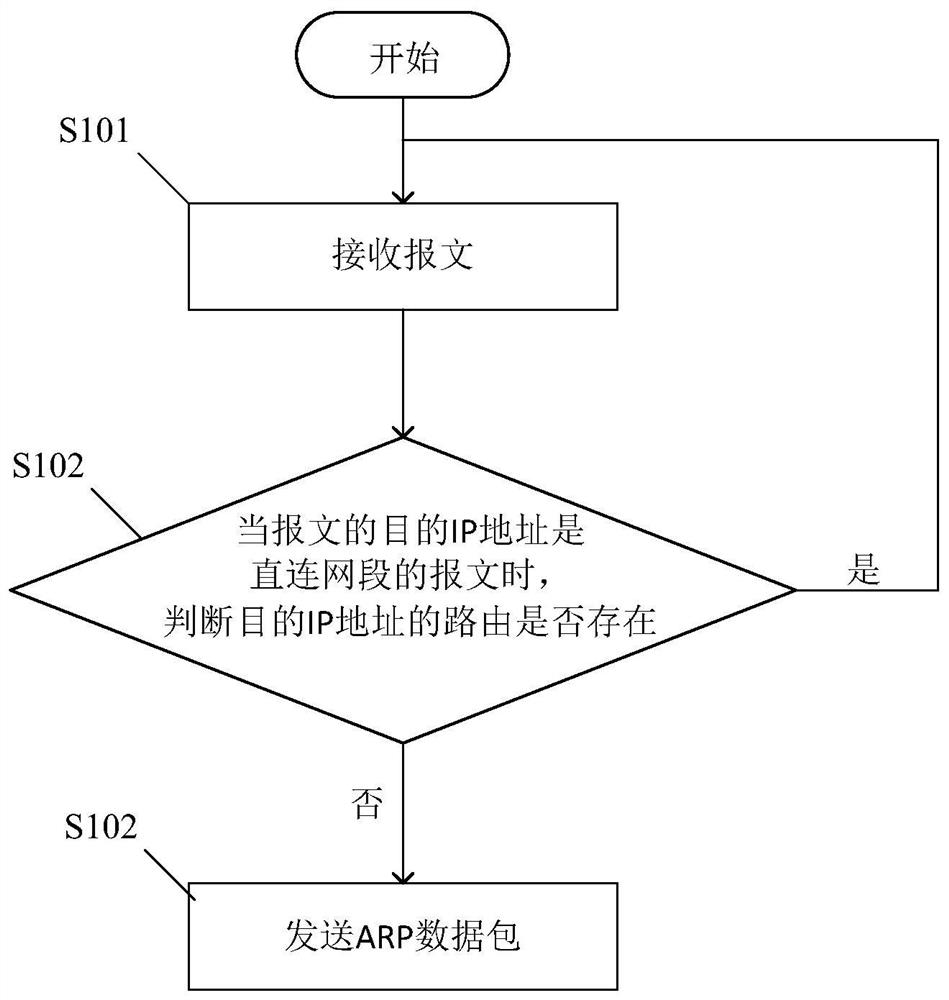
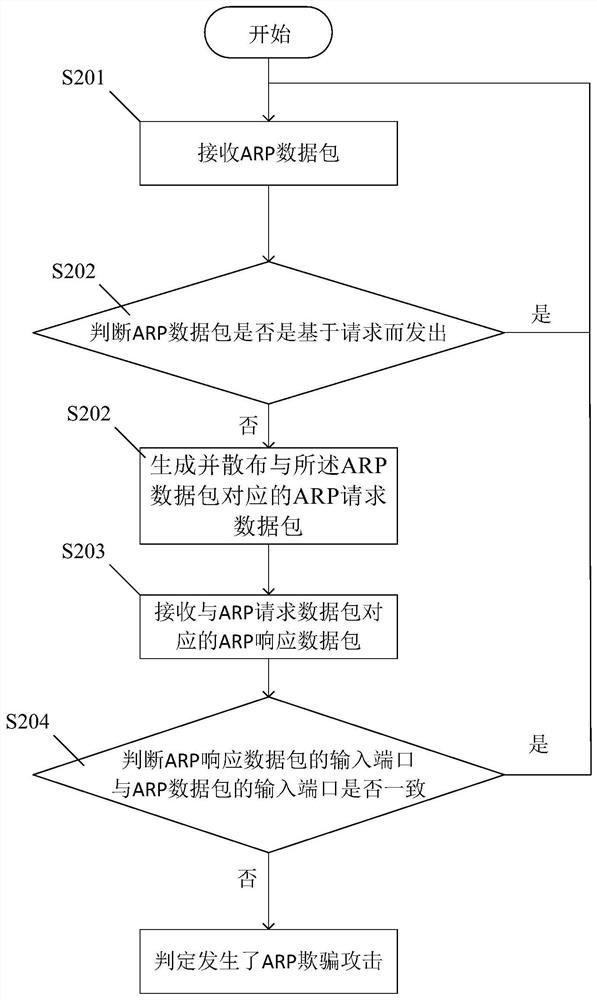
[0019] In order to more clearly illustrate the technical solutions of the embodiments of the present application, the following briefly introduces the drawings that need to be used in the description of the embodiments. Obviously, the accompanying drawings in the following description are only some examples or embodiments of the present application, and those skilled in the art can also apply the present application to other similar scenarios. Unless otherwise apparent from context or otherwise indicated, like reference numerals in the figures represent like structures or operations.
[0020] As indicated in this application and claims, the terms "a", "an", "an" and / or "the" do not refer to the singular and may include the plural unless the context clearly indicates an exception. Generally speaking, the terms "comprising" and "comprising" only suggest the inclusion of clearly identified steps and elements, and these steps and elements do not constitute an exclusive list, and ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More