Key-value pair model safety training and reasoning method based on safety multi-party calculation
A technology of secure multi-party computing and reasoning methods, which is applied in the field of security training and reasoning of key-value pair models based on secure multi-party computing, and can solve problems such as internal data not being open to the outside world and data value not being fully reflected
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0055] The present invention will be described in detail below in conjunction with the accompanying drawings.
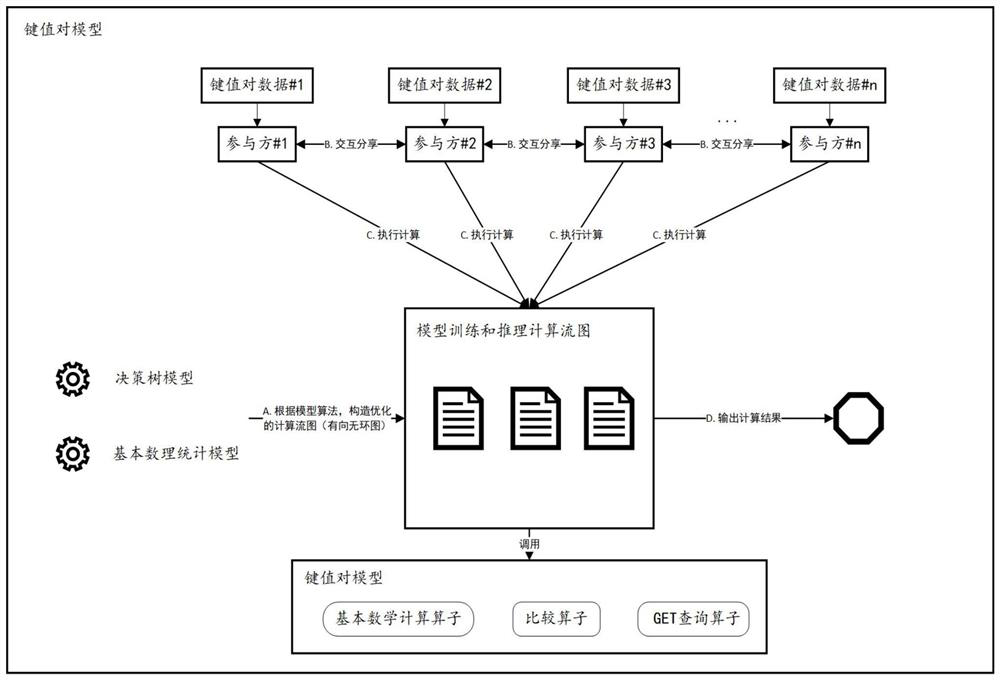
[0056] exist figure 1 Above, participants 1~n want to jointly train or predict a key-value pair model, but they do not want other participants to know the data they own;
[0057] (1) According to the required model algorithm, construct an optimized calculation flow graph, and hand over the model parameters to all participants in the form of secret sharing;
[0058] (2) The participant performs secret sharing of its own local key-value pair data and transmits it to other participants. So far, the entire model and input data are held among all participants in the form of secret sharing;
[0059] (3) All participants cooperate to perform calculations according to the calculation flow graph model, in which basic mathematical calculation operators, comparison operators, and GET query operators are called. The specific operation process of the three models of calculatio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More