File tamper-proofing method and device in container environment
A file and container technology, applied in the field of network security, can solve problems such as inability to judge, reduce the accuracy of file anti-tampering detection, and cannot determine whether a process has an access request, so as to achieve the effect of improving accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
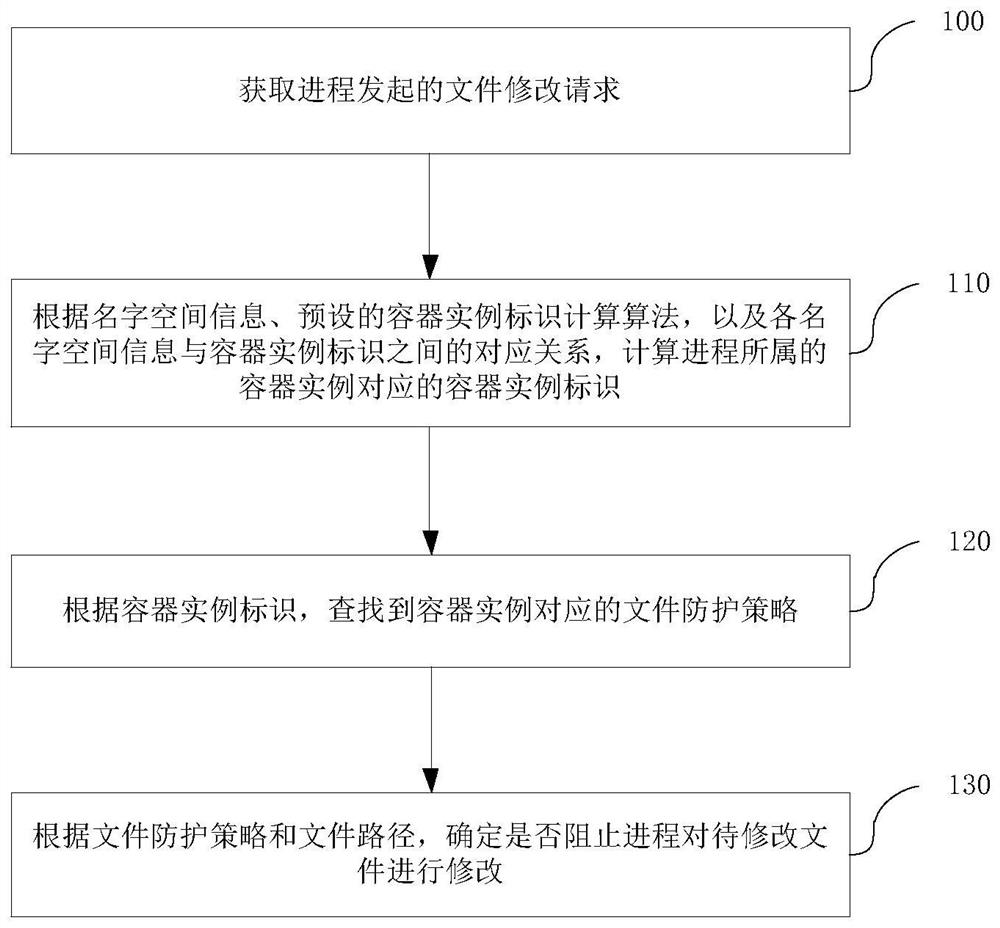
Method used
Image
Examples
Embodiment Construction
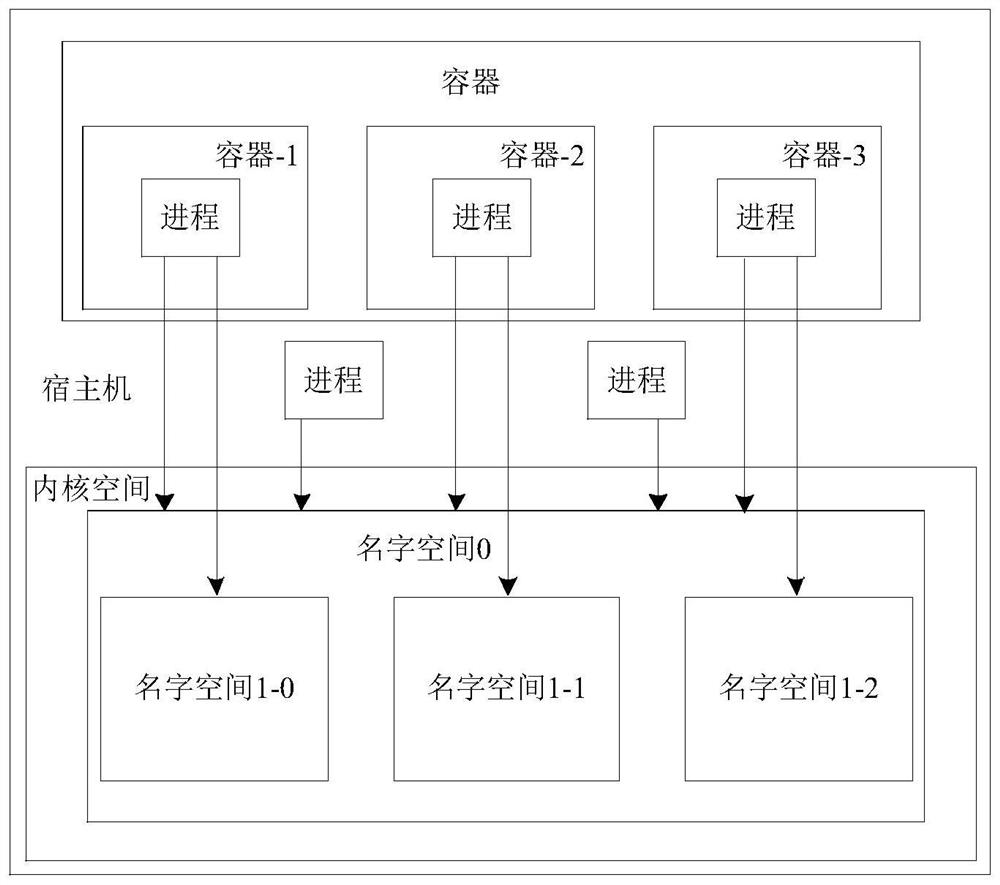
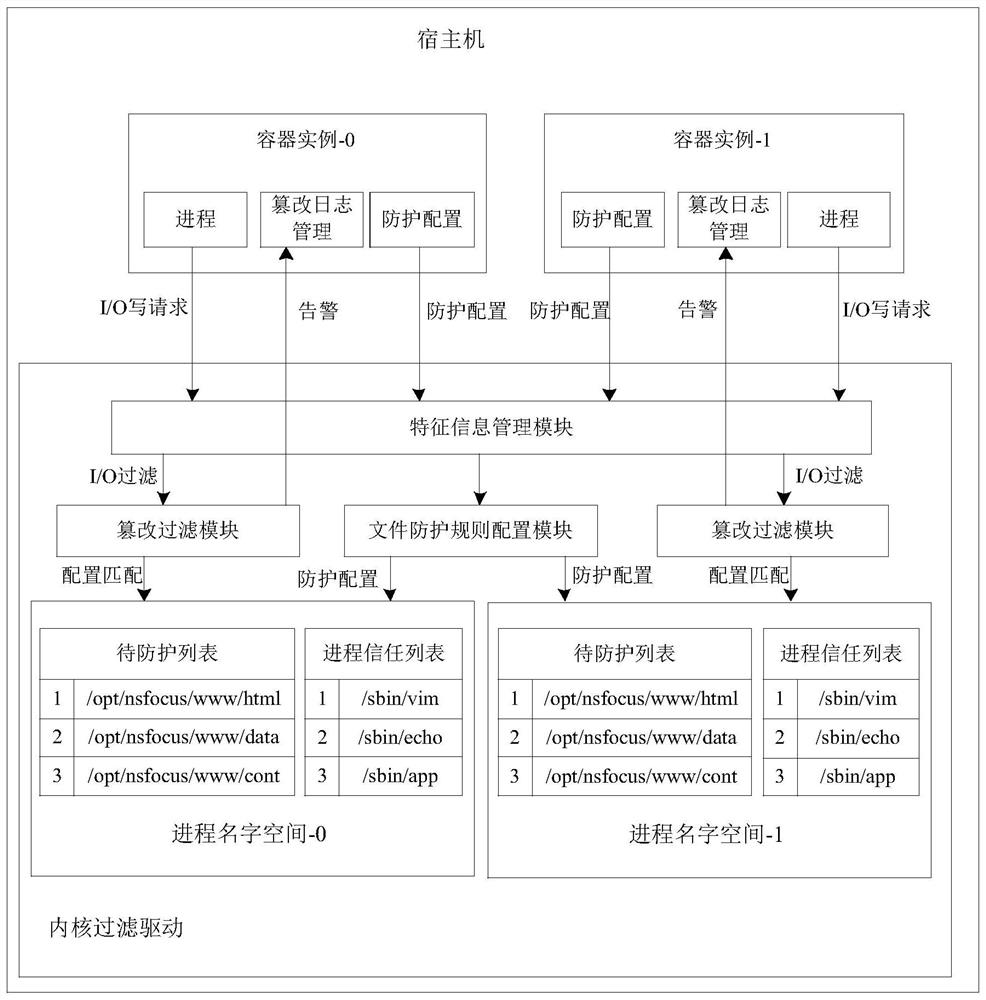
[0060] The technical solutions in the embodiments of the present application will be clearly and completely described below with reference to the drawings in the embodiments of the present application. Obviously, the described embodiments are only a part of the embodiments of the present application, not all of the embodiments. Based on the embodiments in the present application, all other embodiments obtained by those of ordinary skill in the art without creative efforts shall fall within the protection scope of the present application.
[0061] At present, service containerization technology can be applied to various application scenarios, for example, can be applied to public cloud, private cloud, etc. With the development of business containerization technology, the security of container files is particularly important. In order to ensure the security of container files, it is necessary to prevent container files from being tampered with. Therefore, how to realize the tamp...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap