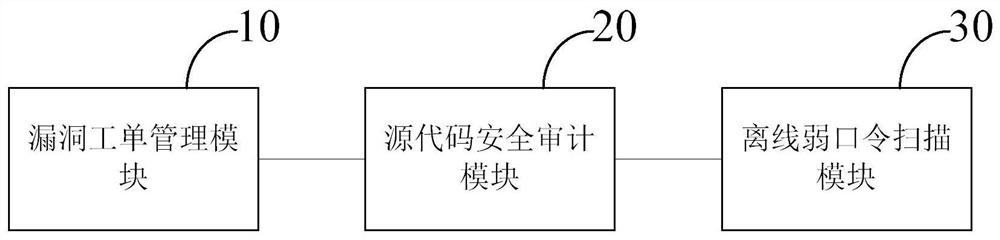
Vulnerability management system integrating vulnerability scanning engine and vulnerability work order management
A vulnerability scanning and vulnerability management technology, which is applied in the field of data processing and can solve problems such as identification and security specifications do not meet
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
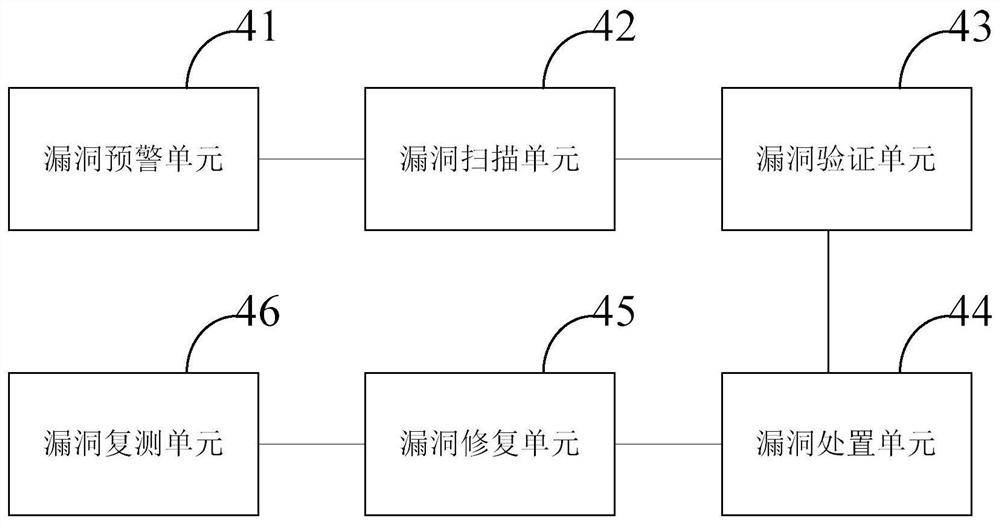
[0048] In order to make the purposes, technical solutions and advantages of the embodiments of the present application more clear, the technical solutions in the embodiments of the present application will be clearly and completely described below with reference to the drawings in the embodiments of the present application. Obviously, the described embodiments It is a part of the embodiments of the present application, but not all of the embodiments. Based on the embodiments in this application, all other embodiments obtained by those of ordinary skill in the art without creative work fall within the protection scope of this application.
[0049]Considering that security configuration errors are generally caused by personnel operating errors. Although there are configuration checklists, industry norms, and programmatic requirements for graded protection that provide operation and maintenance personnel with a basis for checking security configurations, how to quickly and effect...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More