Data synchronization method and system based on XXL-JOB and FlinkSQL
A data synchronization and data source technology, applied in the fields of digital data protection, electronic digital data processing, structured data retrieval, etc., can solve the problems of inefficiency, single data synchronization scheme, etc. inefficient effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
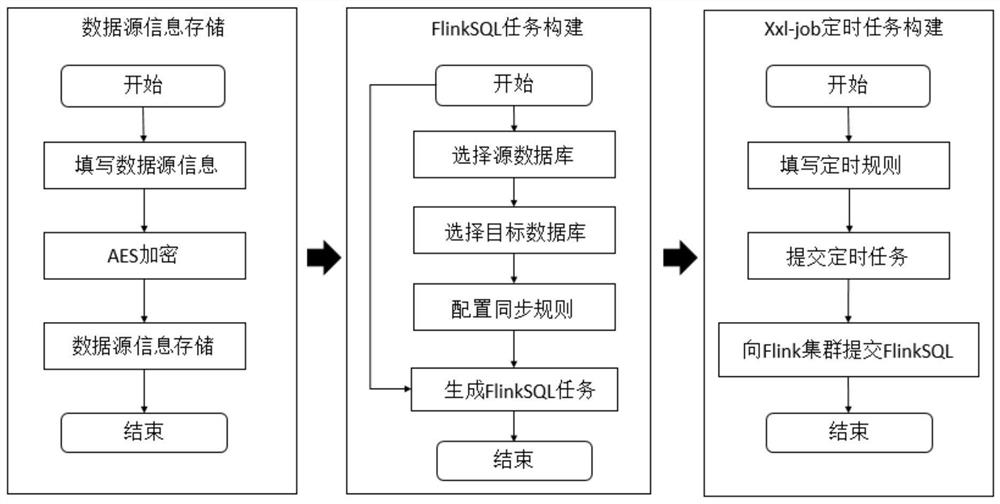
[0044] combined with Figure 1-4 , this embodiment proposes a data synchronization method based on XXL-JOB and FlinkSQL, including the following steps:
[0045] (1) Based on the AES encryption algorithm, the accessed data source information is encrypted, transmitted and stored.
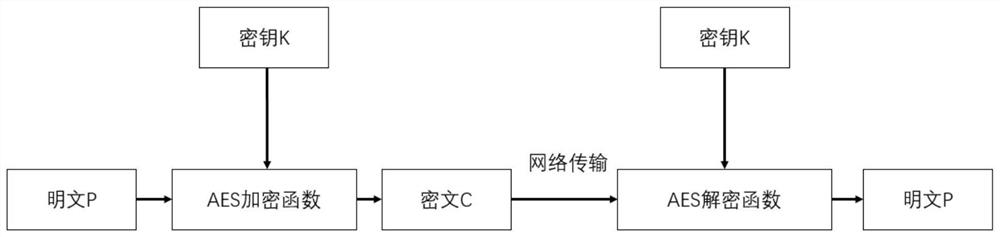
[0046] The AES encryption algorithm is a symmetric encryption algorithm. The specific process of encrypting and transmitting the accessed data source information based on the AES encryption algorithm is as follows:
[0047] The AES encryption function uses the key K to encrypt the plaintext P to obtain the ciphertext C;
[0048] Transfer the ciphertext C to the specified location;
[0049] The AES decryption function uses the key K to decrypt the ciphertext C to obtain the plaintext P.
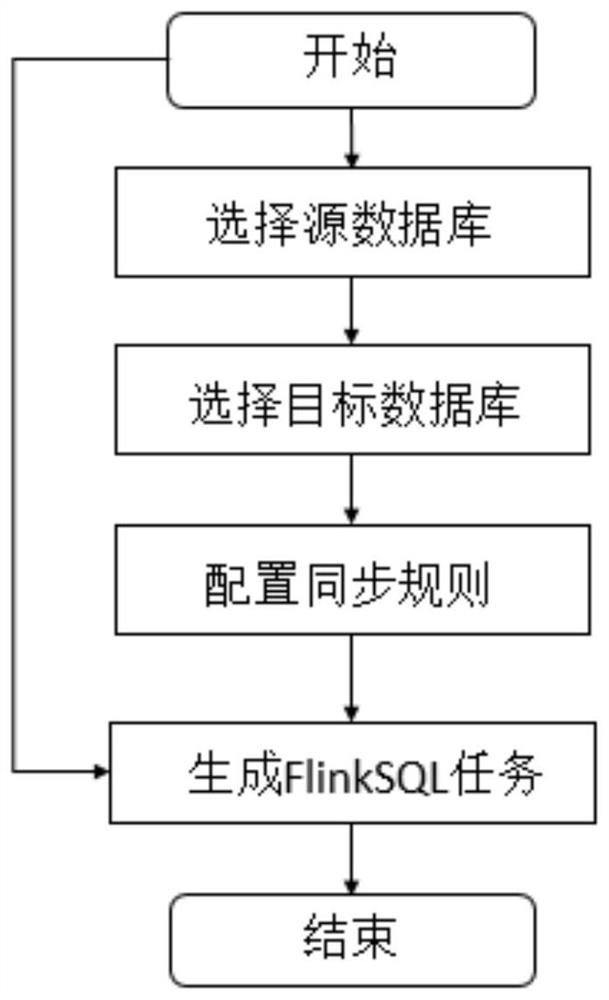
[0050] (2) Build FlinkSQL tasks by selecting source database, target database, and configuring synchronization rules.
[0051] Flink SQL is a simplified computing model for Flink's real-time computing. The SQL con...
Embodiment 2
[0057] combined with Figure 2-5 , this embodiment proposes a data synchronization system based on XXL-JOB and FlinkSQL, its structure includes: AES encryption module 1, synchronization task construction module 2, timing task configuration module 3, timing task execution module 4.
[0058] AES encryption module 1 is used to encrypt, transmit and store the accessed data source information. The specific encryption process is as follows:
[0059] The AES encryption function uses the key K to encrypt the plaintext P to obtain the ciphertext C;
[0060] Transfer the ciphertext C to the specified location;
[0061]The AES decryption function uses the key K to decrypt the ciphertext C to obtain the plaintext P.
[0062] Synchronization task construction module 2 is used to construct FlinkSQL tasks by selecting source database, selecting target database, and configuring synchronization rules.
[0063] Timing task configuration module 3 is used to configure different timing rules fo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More