Unauthorized verification method and device, equipment and storage medium
A verification method and equipment technology, applied in the field of unauthorized verification, can solve the problems of strong code intrusion and poor scalability, and achieve the effect of strong scalability and avoiding pollution
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
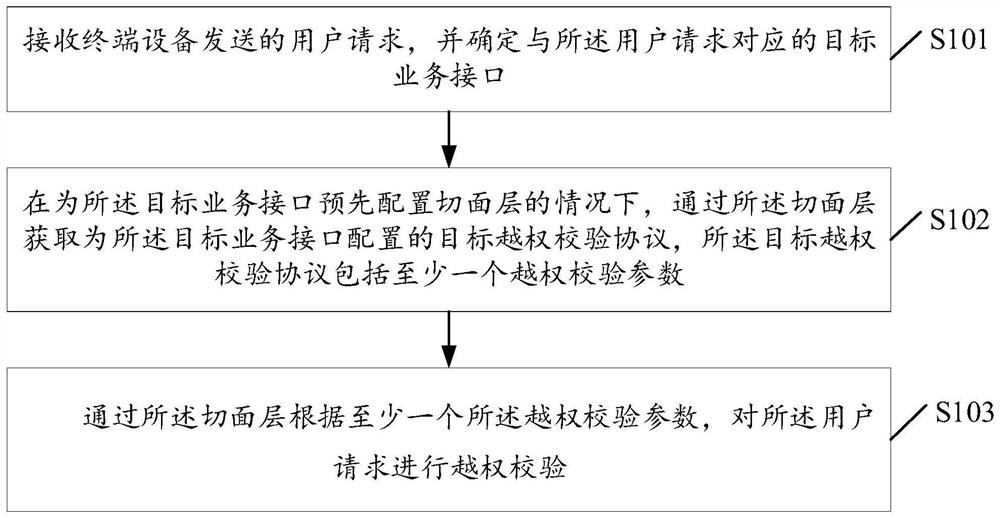
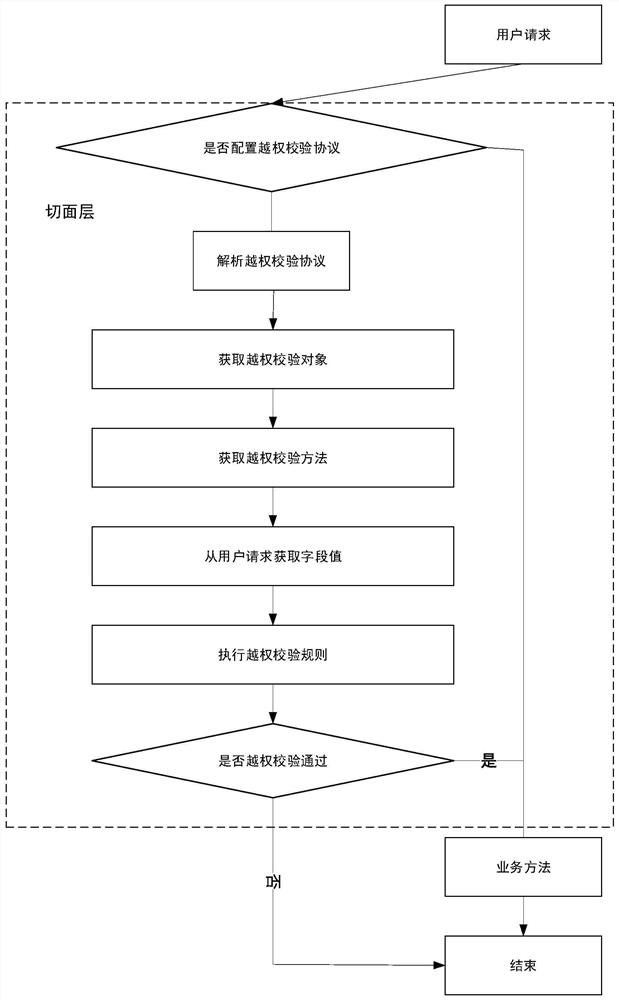
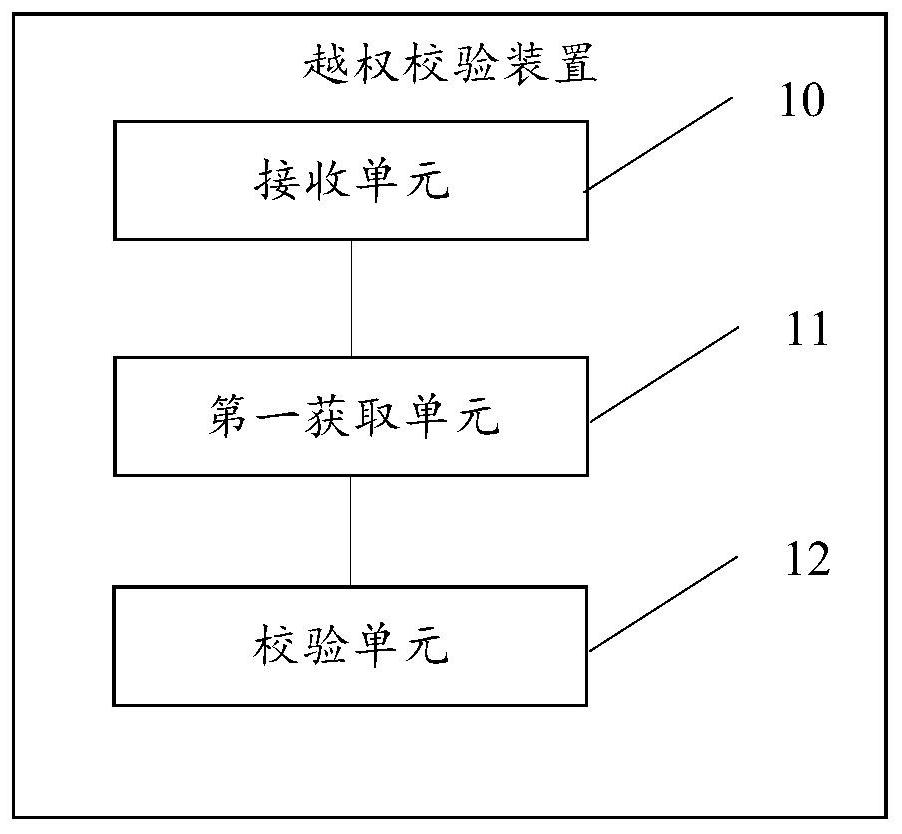
[0062] The present invention will be described in further detail below in conjunction with the accompanying drawings.
[0063] The terms used in the following embodiments of the present application are only for the purpose of describing specific embodiments, and are not intended to limit the present application. As used in the specification and appended claims of this application, the singular expressions "a", "an", "said", "above", "the" and "this" are intended to also Plural expressions are included unless the context clearly indicates otherwise.
[0064] In this application, "at least one (item)" means one or more, "multiple" means two or more, "at least two (items)" means two or three and three Above, "and / or" is used to describe the association relationship of associated objects, which means that there can be three kinds of relationships, for example, "A and / or B" can mean: only A exists, only B exists, and A and B exist at the same time A case where A and B can be sing...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More