Digital cipher lock with secure secondary authorization unlocking function
A technology for unlocking passwords and coded locks, which is applied in building locks, lock applications, electric paired locks, etc., can solve problems such as limited parameters, hidden safety hazards, and inappropriateness, and achieve improved security, high security, and no super The effect of the password
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] Now in conjunction with accompanying drawing, technical solution and embodiment are further described:
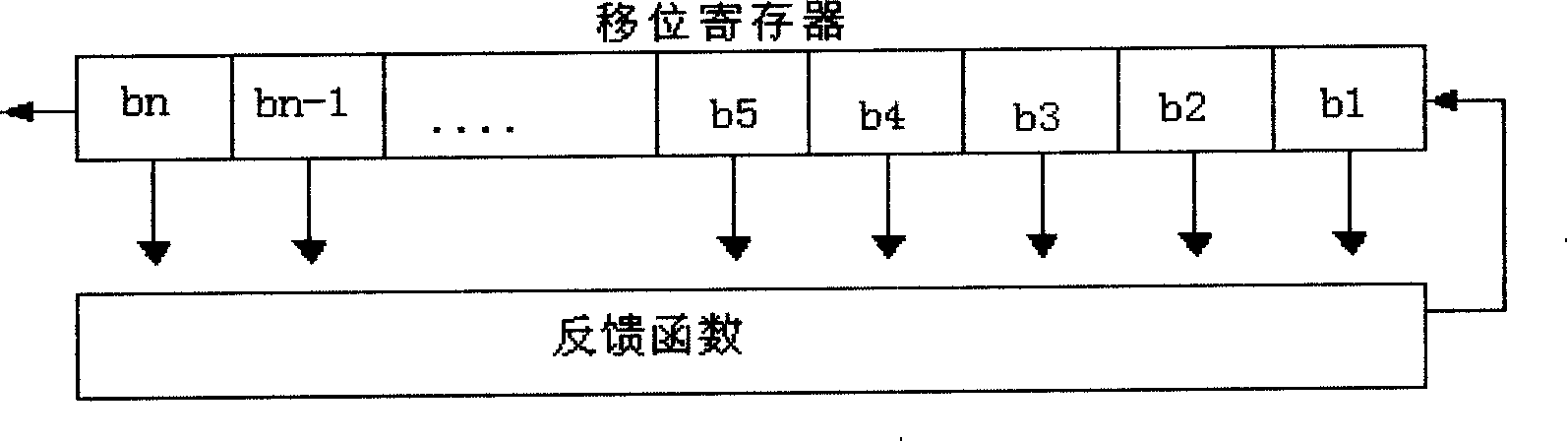
[0025] figure 1 , Schematic diagram of the feedback shift register.
[0026] Shift register sequences are used in cryptography and coding theory. Since the beginning of the electronic age, sequence ciphers based on shift registers have been widely used in encryption operations in military cryptography. A feedback shift register consists of two parts: the shift register and the feedback function. A shift register is a sequence of bits. Each time a bit is needed, all bits in the shift register are shifted to the right (left) by one bit, and the new leftmost (right) bit is calculated based on other bits in the shift register. The feedback function performs logic operations with certain bits in the shift register (these bits are called tap sequences) in a certain way to form the new leftmost (right) bit of the shift cycle.
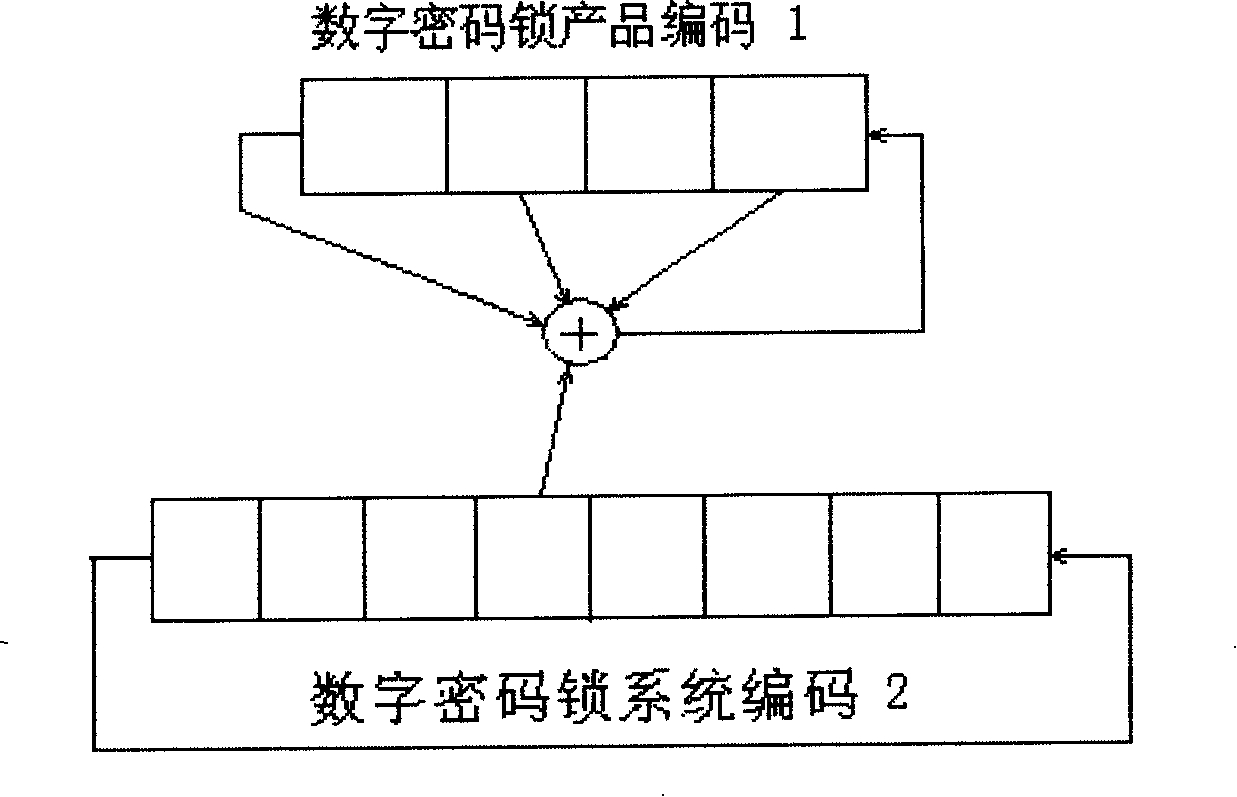
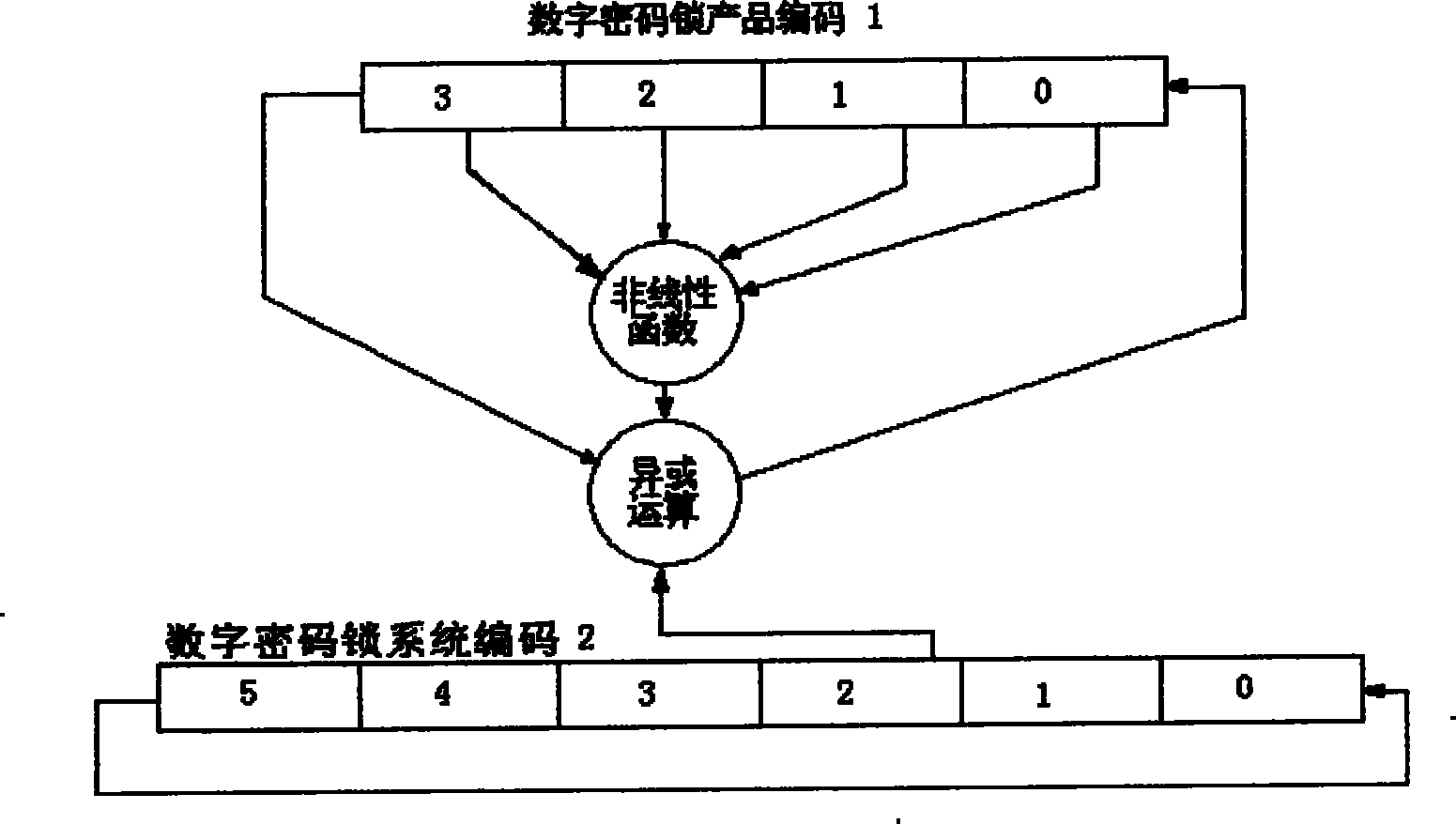
[0027] figure 2 , The schematic diagram of...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More