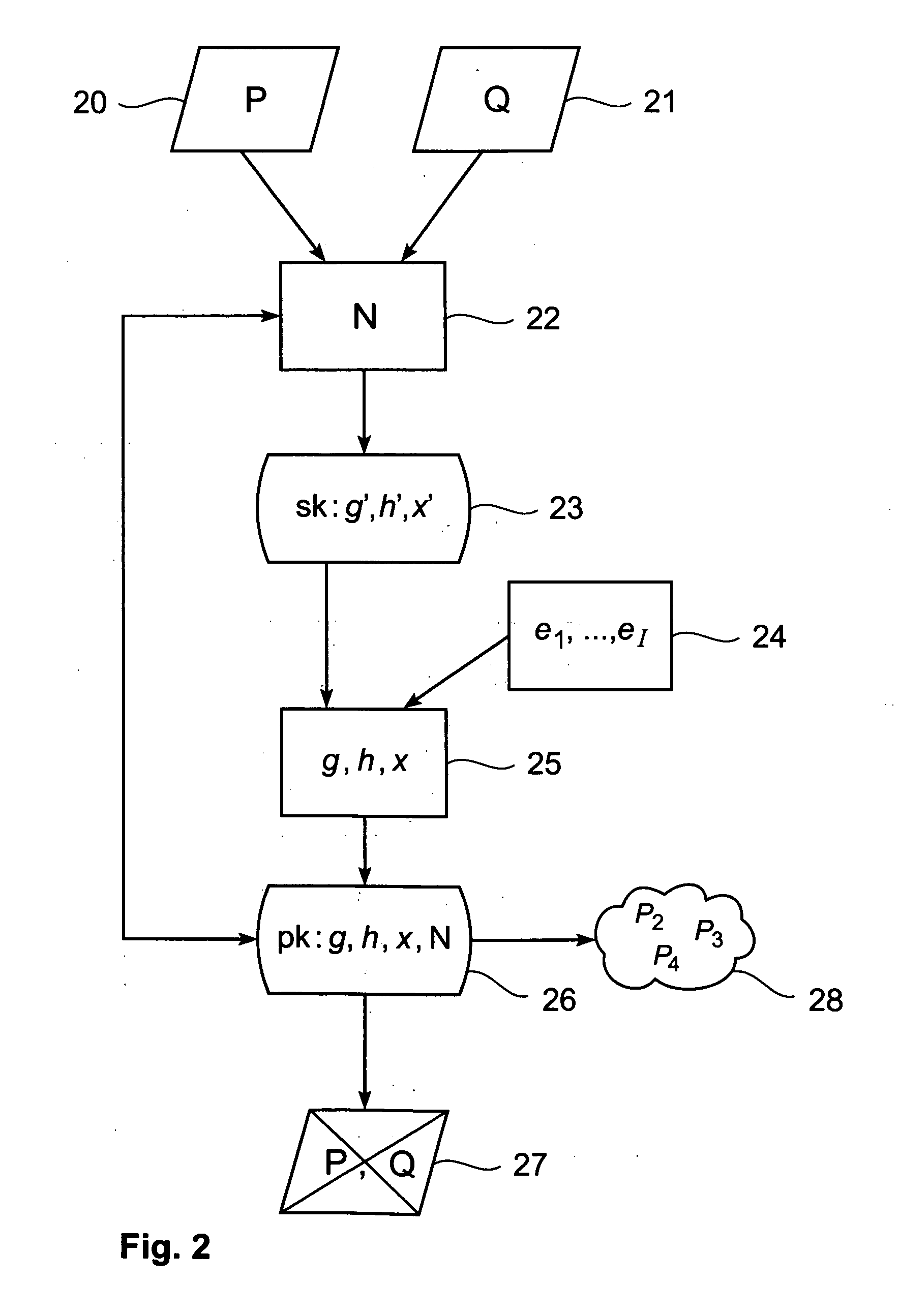
[0008] In accordance with a first aspect of the present invention, there is given a method for providing a secret cryptographic key sk and a public cryptographic key pk applicable in a network of connected computer nodes using a signature scheme. The method is executable by a first computer node and comprises the steps of generating the secret cryptographic key sk by selecting two random factor values P, Q, multiplying the two selected random factor values P, Q to obtain a modulus value (N), and selecting a secret base value g′, h′, x′ in dependence on the modulus value N, wherein the secret base value g′, h′, x′ forms part of the secret cryptographic key g′, h′, x′. The method further comprises generating the public cryptographic key pk by selecting a number I of exponent values e1, . . . , eI, and deriving a public base value g, h, x from the exponent values e1, . . . , eI and the secret base value g′, h′, x′ wherein the public base value g, h, x and the modulus value N form part of the public cryptographic key g, h, x, N. The method further comprises the steps of deleting the two random factor values P, Q; and providing the public cryptographic key g, h, x, N within the network; such that the public cryptographic key g, h, x, N and at least one of the selected exponent values e1, . . . , eI is usable for verifying a signature value i, y, a on a message m to be sent within the network to a second computer node for verification.
[0009] In a second aspect of the present invention, there is given a method for providing a signature value i, y, a on a message m in a network of connected computer nodes, the method being executable by a first computer node and comprising the steps of selecting a first signature element a; selecting a signature exponent value ei from a number I of exponent values e1, . . . , eI; and deriving a second signature element y from a provided secret cryptographic key g′i, h′1, x′i, the message m, and the number I of exponent values e1, . . . , eI such that the first signature element a, the second signature element y, and the signature exponent value ei satisfy a known relationship with the message m and a provided public cryptographic key g, h, x, N, wherein the signature value i, y, a comprises the first signature element a, the second signature element y, and a signature reference i to the signature exponent value ei, the signature value i, y, a being sendable within the network to a second computer node for verification.
[0010] In a third aspect of the present invention, there is given a method for verifying a signature value i, y, a on a message m in a network of connected computer nodes, the method being executable by a second computer node and comprising the steps of receiving the signature value i, y, a from a first computer node; deriving a signature exponent value ei from the signature value i, y, a; and verifying wh
 Login to View More
Login to View More  Login to View More
Login to View More