Hash function method with single round collision-proof performance
A hash value and equation technology, applied in the field of information security, can solve problems such as analytical operation collision
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
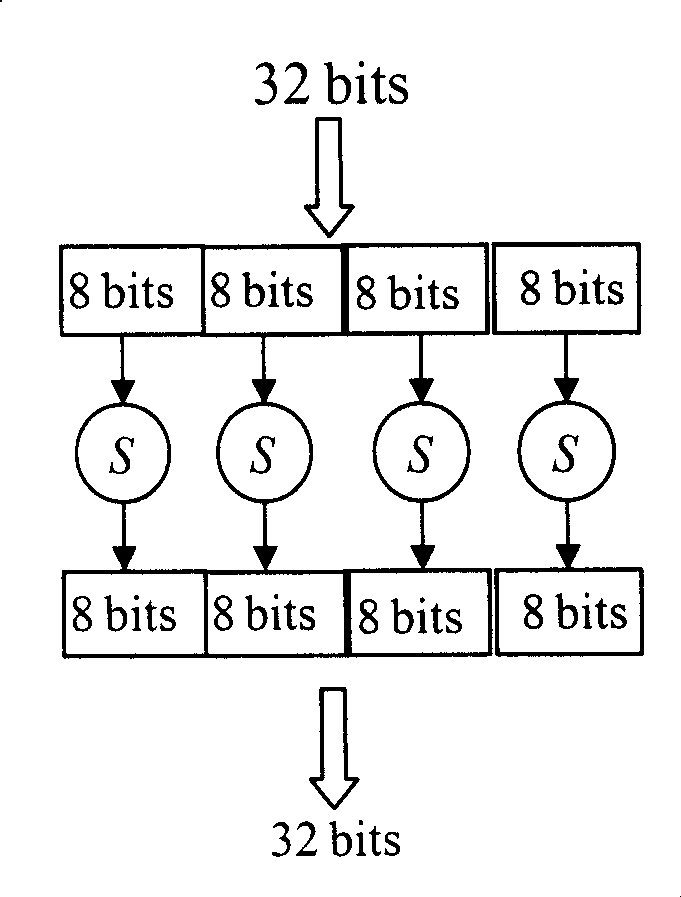
Image
Examples
Embodiment Construction
[0071] B1) The present invention designs five kinds of hash values 128, 192, 256, 384 and 512 bits, and selects the number of coupling grid points according to the requirements of the hash value. The specific implementation parameters are as follows:
[0072] B1.1) The number of coupling grid points is N=4, the iteration round p=2, and a 128-bit hash value is output.
[0073] B1.2) The number of coupling grid points is N=6, the iteration round p=2, and a 192-bit hash value is output.
[0074] B1.3) The number of coupling grid points is N=8, the iteration round p=2, and a 256-bit hash value is output.
[0075] B1.4) The number of coupling grid points is N=12, the iteration round p=2, and a 384-bit hash value is output.
[0076] B1.5) The number of coupling grid points is N=16, the iteration round p=2, and a 512-bit hash value is output.
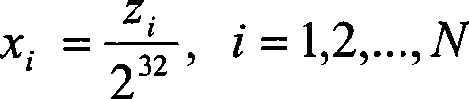
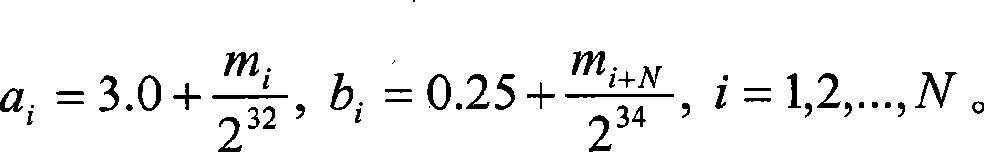
[0077] B2) The present invention needs to have definite initial state value H when realizing 1 , H 2 ,...,H N . Hash value output fo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More