Identification authentication method between peer-to-peer user nodes in P2P network
A P2P network and peer-to-peer user technology, applied in the field of identity authentication between user nodes, can solve problems such as huge loads, reduce pressure, simplify the process, and achieve simple effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
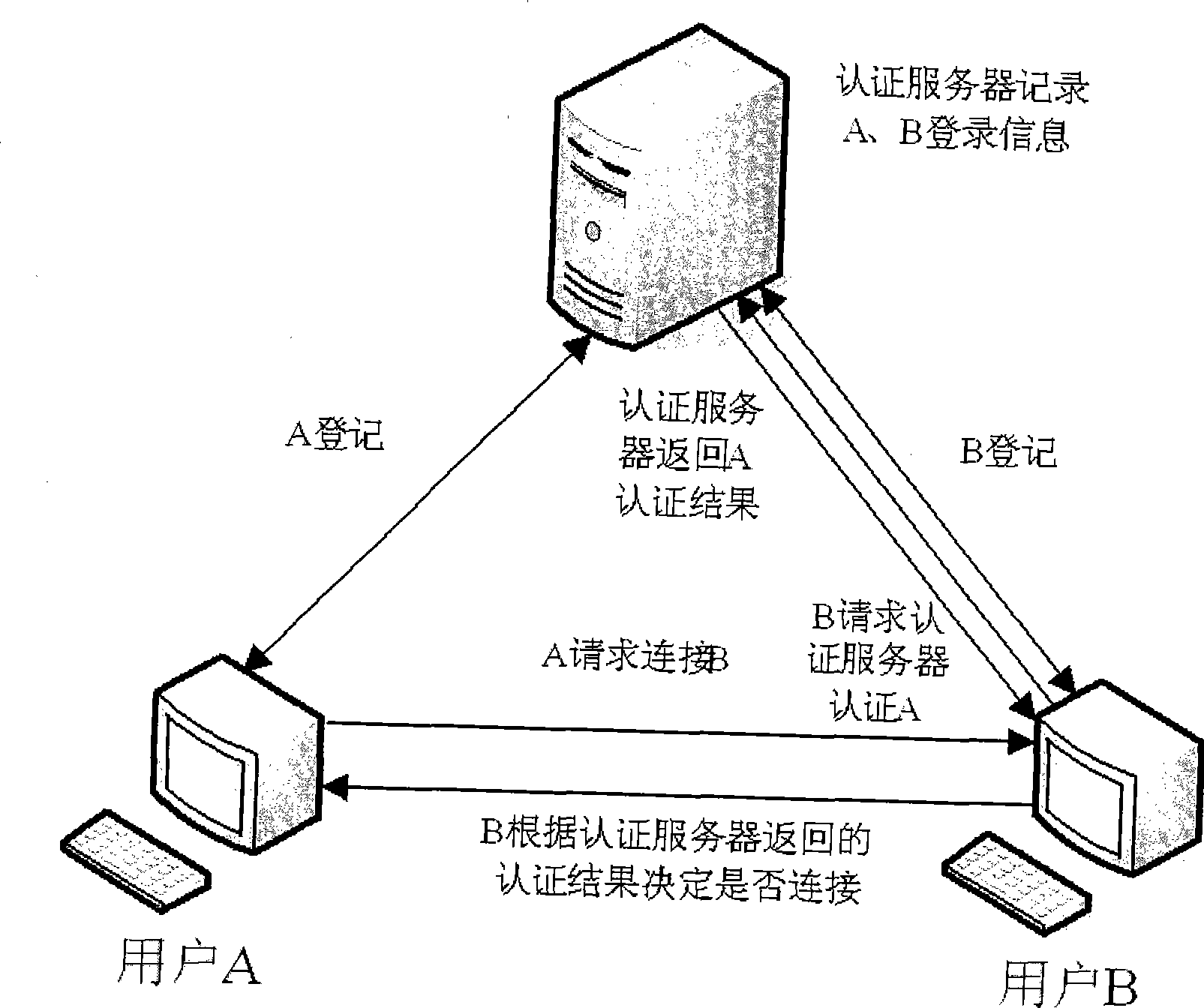
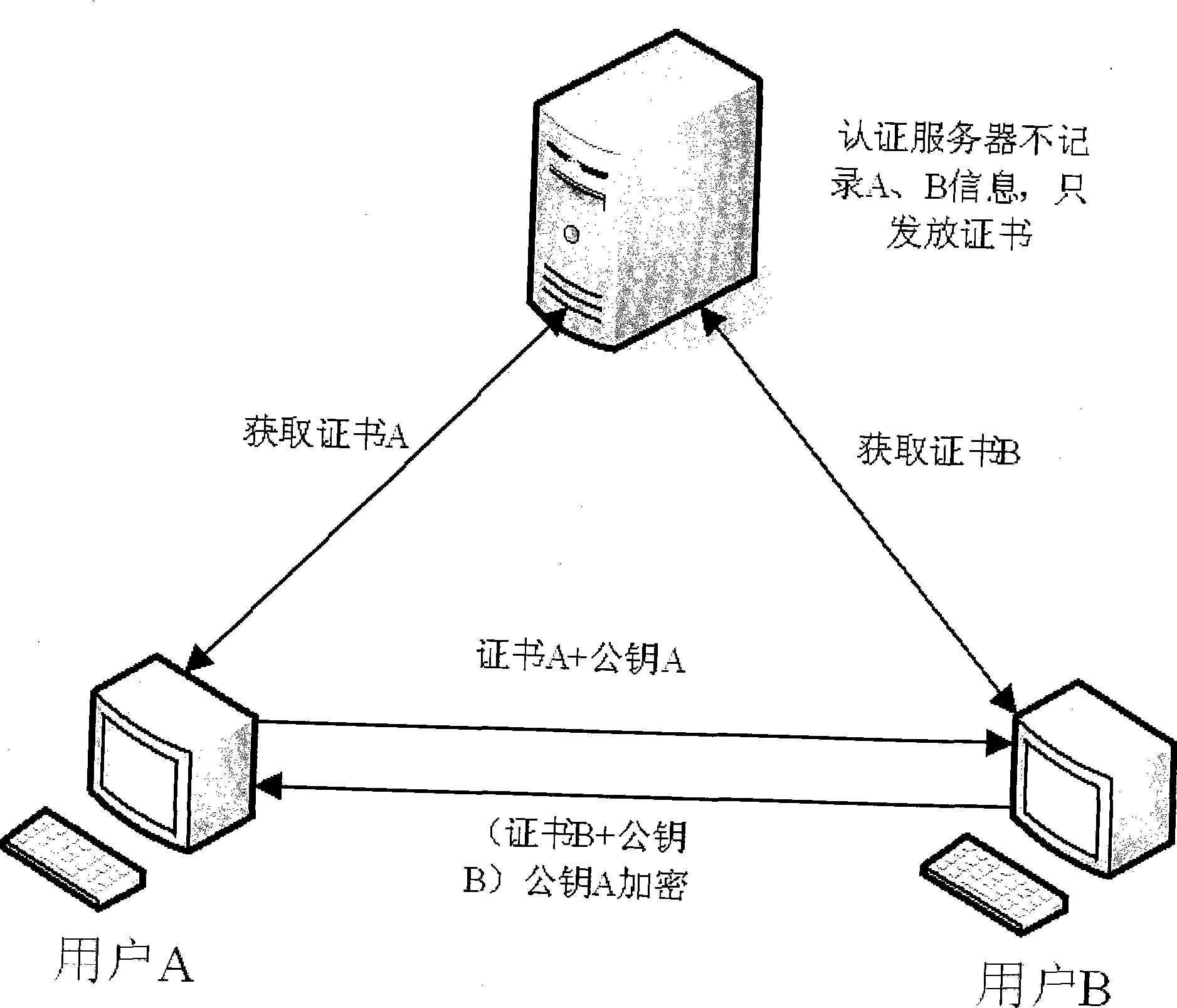
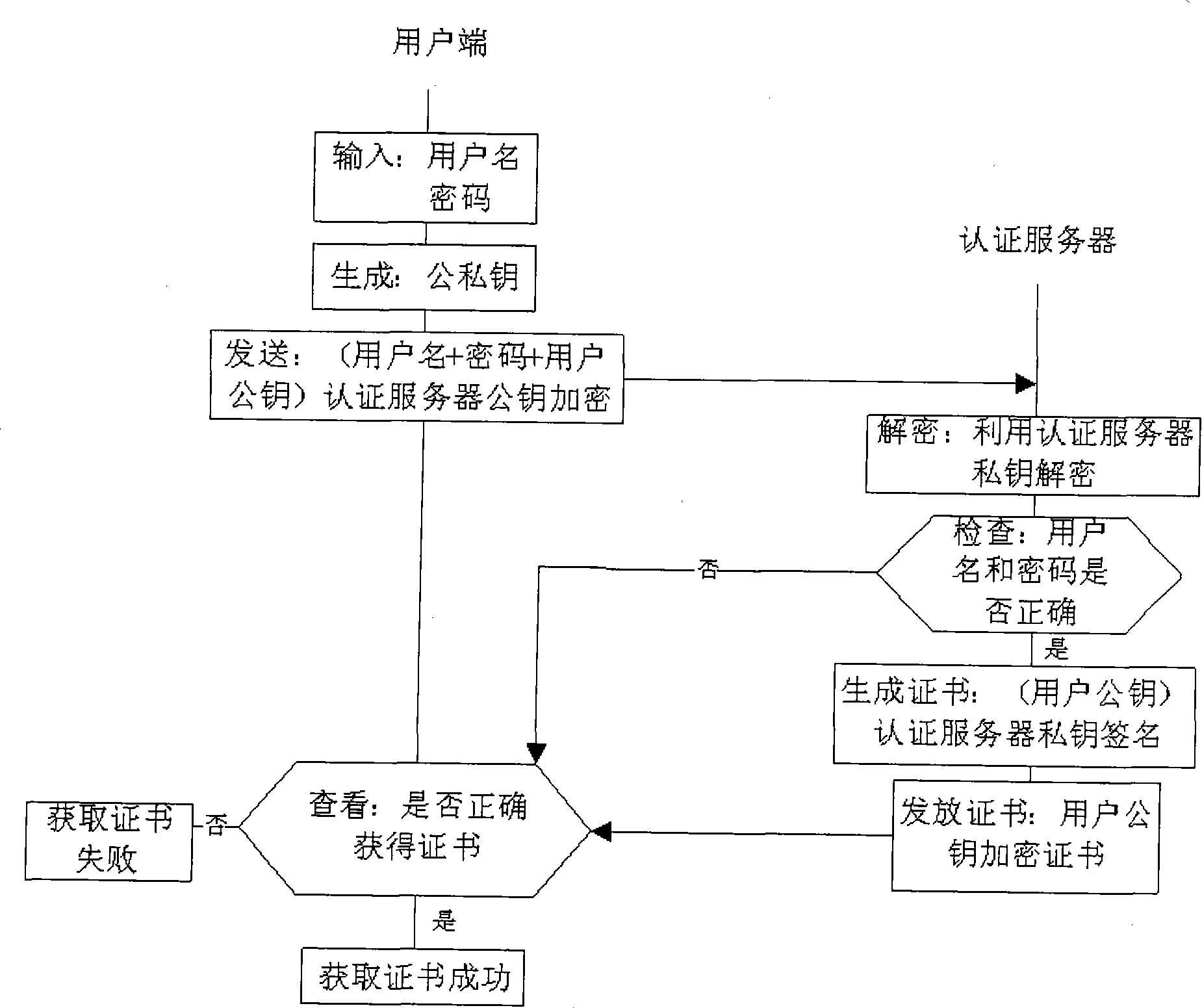
[0036] For the convenience of understanding, in one embodiment of the present invention, a simple P2P network is taken as an example to illustrate how to implement the method of the present invention. Such as figure 2 As shown, in this P2P network, there are two user nodes, user node A and user node B respectively, user node A and user node B are connected through the network, and there is another user node on the network The authentication server that points A and B are connected to. There are asymmetric encryption algorithms on user node A, user node B and authentication server respectively. User nodes in the P2P network will get their own certificates during the login process, and mutual identity authentication can be realized by using this certificate. refer to image 3 , firstly, the process of obtaining the user node certificate is d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More