User authorization method and system and device thereof
A user authorization and user technology, applied in the network field, can solve the problems of reducing system security, unclear validity period, and unclear user authorization timeliness and scope, and achieves the effect of improving security and solving service inefficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
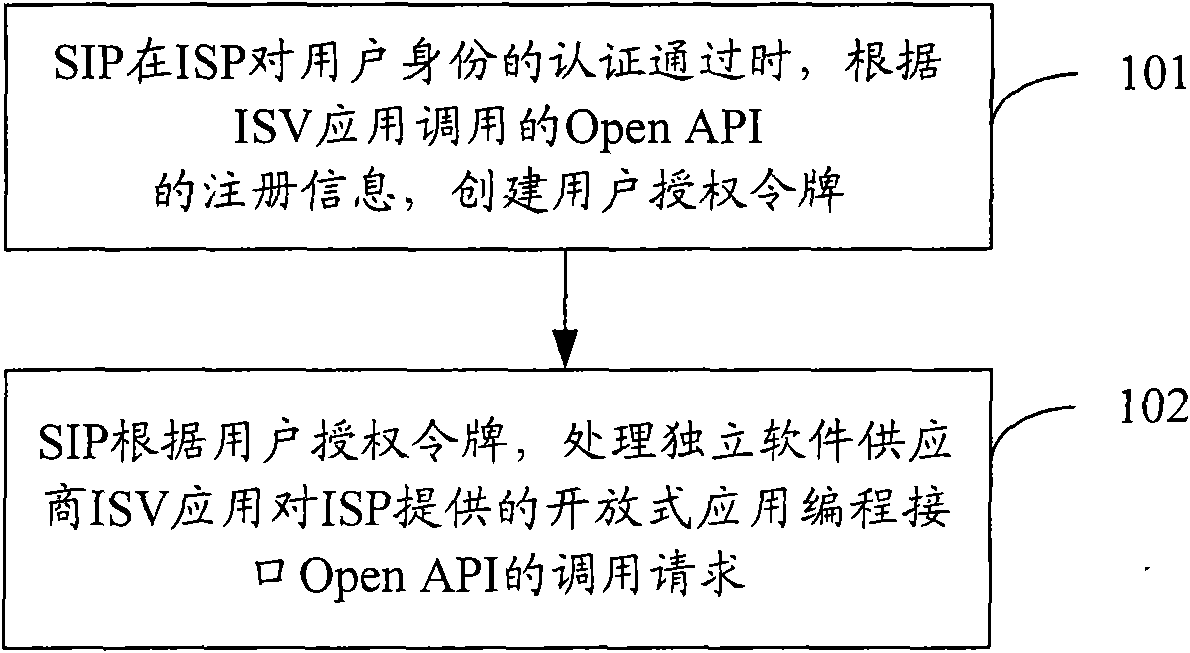
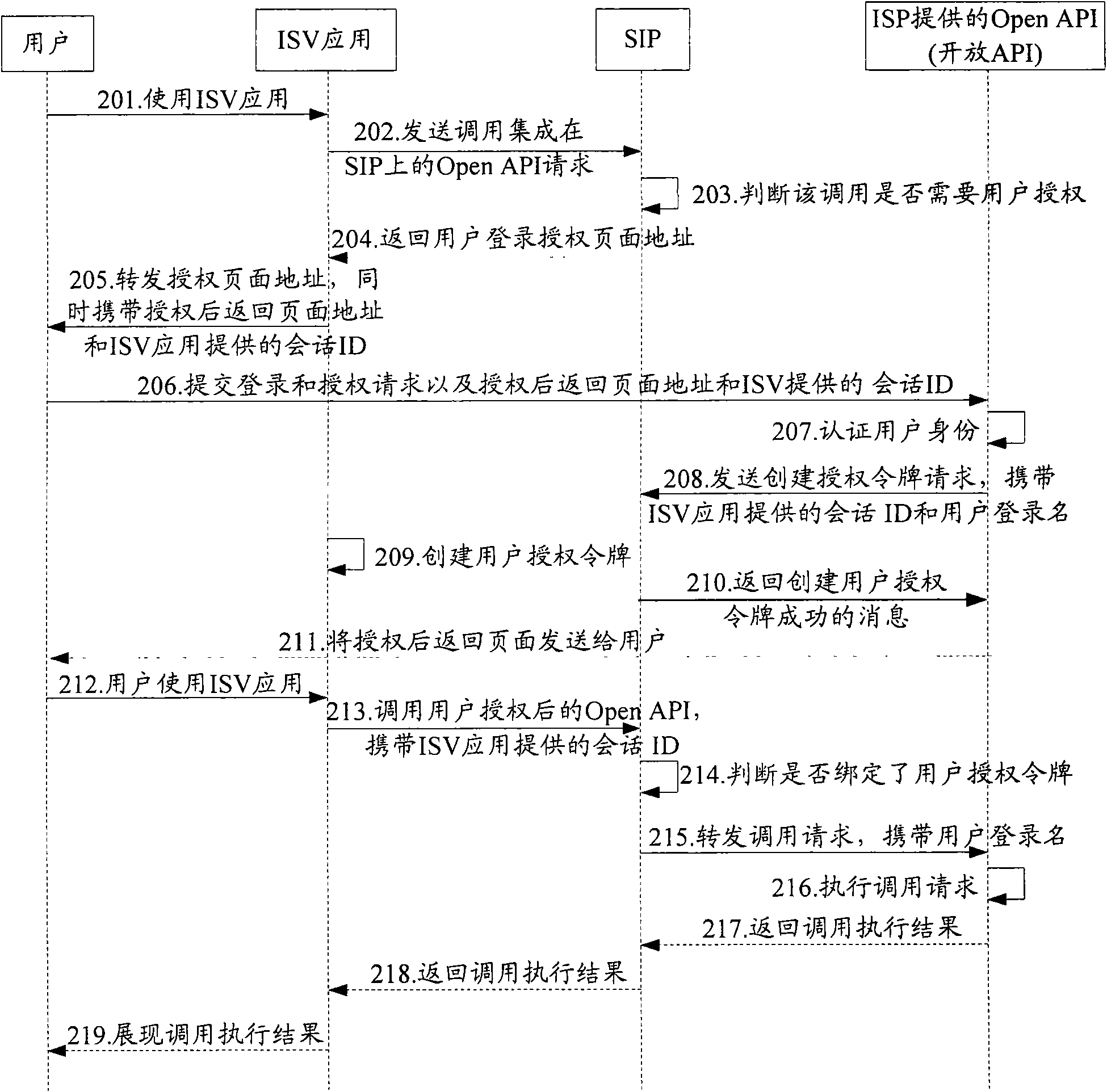
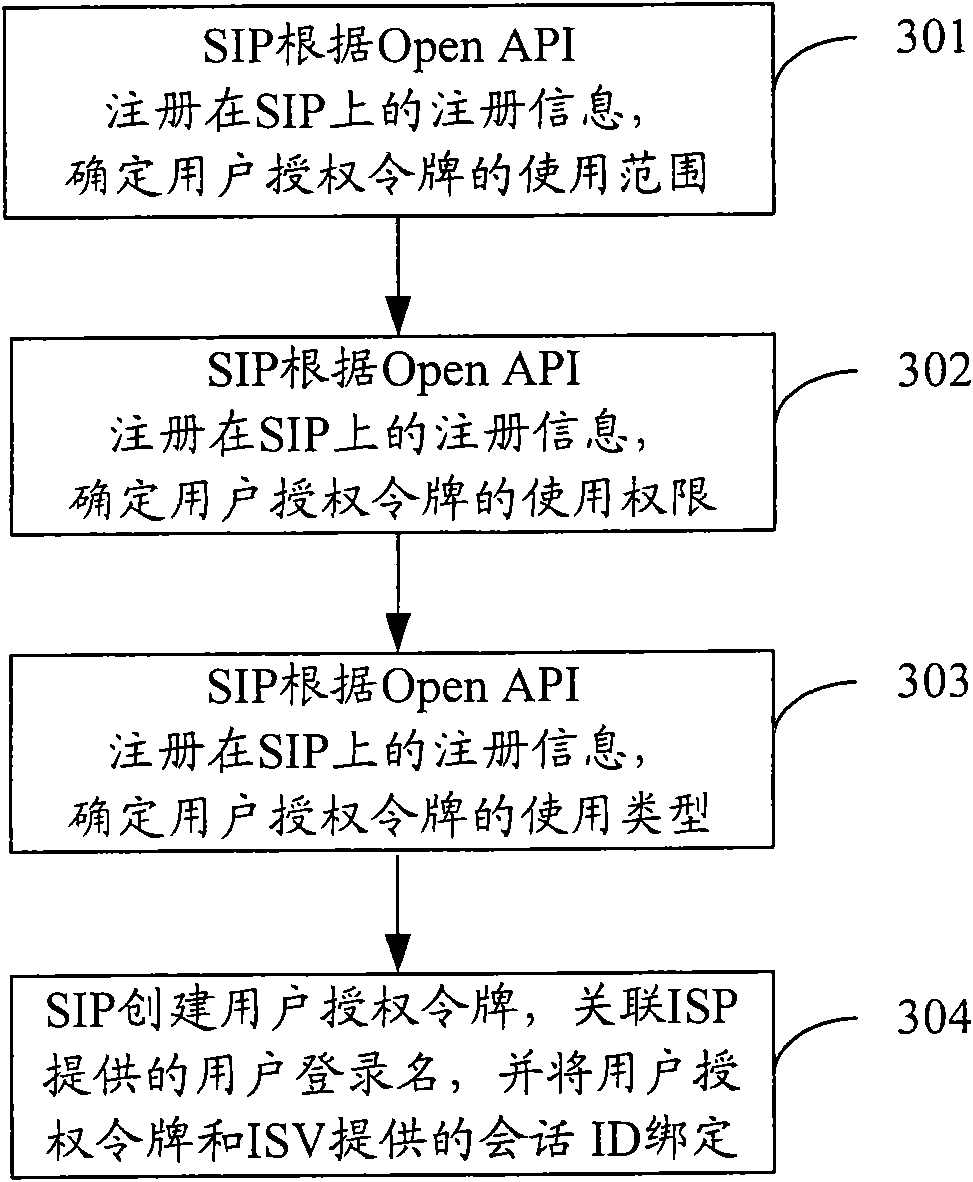
[0081] The main idea of this application is that the service integration platform SIP creates a user authorization token according to the registration information of the Open API called by the ISV application when the Internet service provider ISP passes the authentication of the user identity; , processing the calling request of the ISV application to the OpenAPI provided by the ISP.
[0082] The technical solutions in this application will be clearly and completely described below in conjunction with the drawings in this application. Apparently, the described embodiments are part of the embodiments of this application, not all of them. Based on the embodiments in the present application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present application.
[0083] ISV applications provide its users with a variety of software, such as e-fax, online recruitment tools, e-magazines, an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More