Password protection method
A password protection and password technology, applied in the direction of instruments, digital data authentication, electronic digital data processing, etc., can solve problems such as password leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0019] In this embodiment, by setting a plurality of invisible input areas on the touch screen, when inputting a password, the input button is not real, and the original screen is maintained. Password input is performed by operating a plurality of invisible input areas that the user himself knows. In this way, even if other people see the user's operations, they don't know that those operations are password input actions, which effectively protects the password from being leaked.
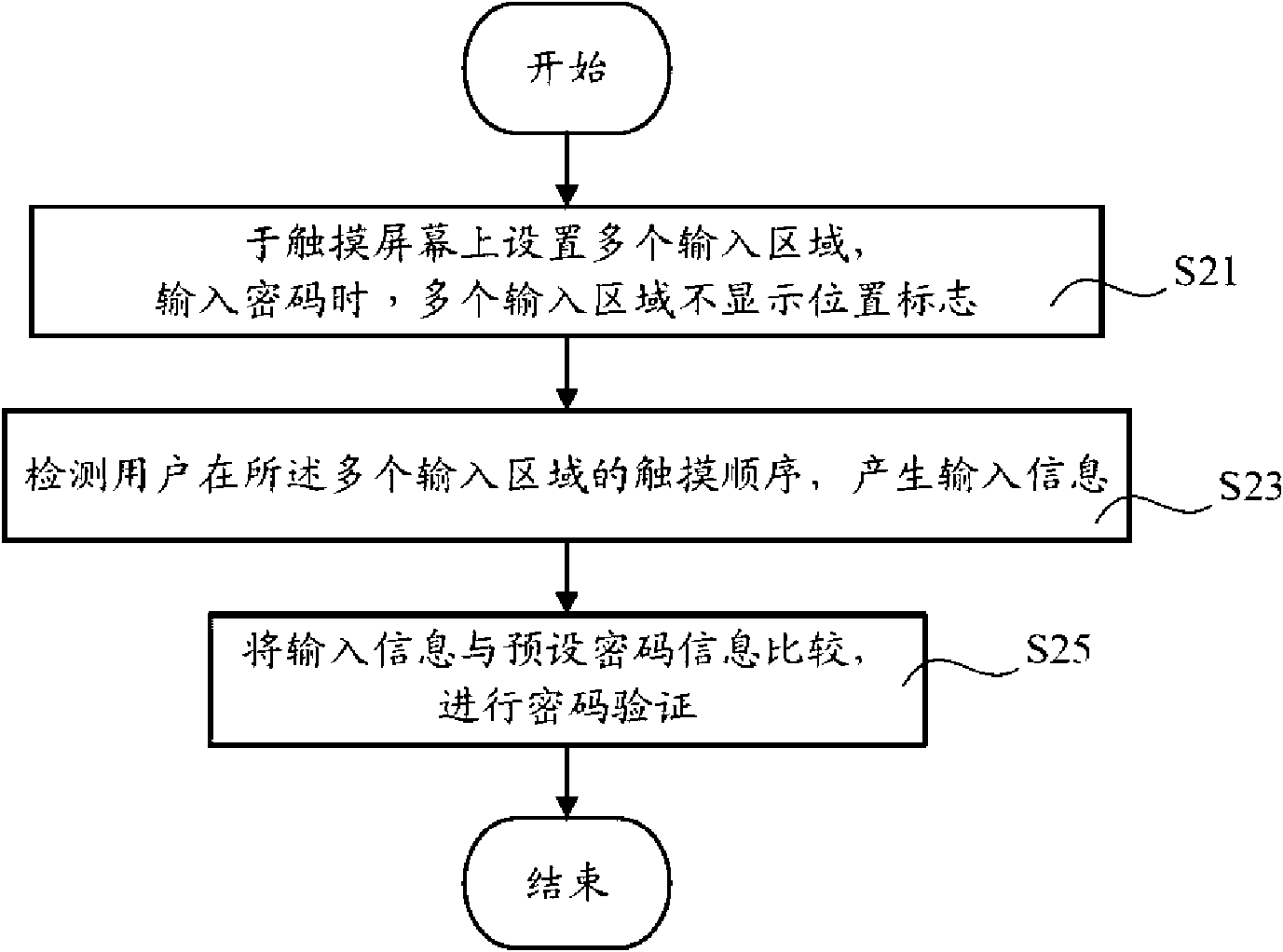
[0020] Please also see figure 1 , which are respectively a flow chart of the steps of a password protection method in a preferred embodiment, including the following steps:
[0021] Step S21, setting multiple input areas on the touch screen. When entering the password, the multiple input areas do not display position marks, such as keeping the original screen or displaying a screen that has nothing to do with the position of the input area, as if providing multiple invisible input buttons. Such as...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More